
Attackers provided victims who paid with an updated Ryuk ransomware decryptor that could potentially damage their larger files. Emsisoft found that malicious actors had added numerous new features to Ryuk ransomware over the past year. In a lesser-known case, attackers gave Ryuk the ability to partially encrypt files that exceeded 54.4 MB in size. This update helped newer variants of the ransomware save time in their encryption process so that they could affect all relevant data before the victim notices. Partially encrypted files demonstrate an unusual footer at the end of the file, which is where Ryuk's Hermes file marker stores its RSA-encrypted AES key. This location also usually contains an indicator that shows how many 1,000,000-byte blocks are encrypted by the threat.
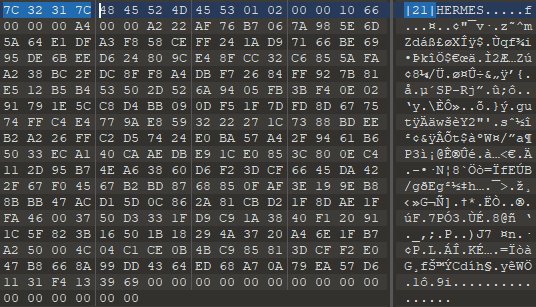
The extended version of the Ryuk file footer that highlights the number of encrypted blocks for partially encrypted files. (Source: Emsisoft) In its latest versions, however, Ryuk ransomware began calculating the length of the footer a bit differently. These changes caused the attackers' decryptor to cut off one too many bytes at the very end of the file. Such truncation could damage the file depending on its type. As Emsisoft explained in its research:
In the best case scenario, the byte that was cut off by the buggy decryptor was unused and just some slack space at the end created by aligning the file towards certain file size boundaries. However, a lot of virtual disk type files like VHD/VHDX as well as a lot of database files like Oracle database files will store important information in that last byte and files damaged this way will fail to load properly after they are decrypted.
In response the issues described above, Emsisoft urged victims of Ryuk ransomware to contact its team members so that they could send over the security firm's own decryption tool that works properly. It also emphasized the importance of victims backing up their data before attempting to use any decryptor. Sometimes, these tools don't work properly the first time they're used; data backups ensure that victims can attempt to recover their data again, if that's the case. Ransomware victims should also follow these steps to prevent an infection in the first place.

