
Security researchers found several clues linking the WebNavigator web browser to well-known search hijackers.
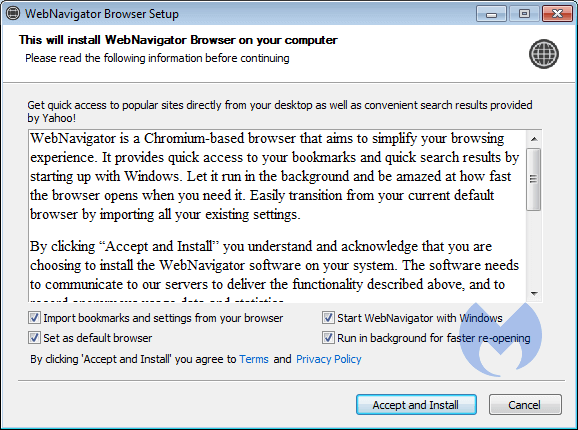
A Chromium-based browser, WebNavigator promises users that it'll simplify their web browsing experience by providing "quick access" to their bookmarks. The browser also claims to yield quick search results by starting up with Windows and by constantly running in the background.
However, Malwarebytes analyzed the web browser and found a connection to what's known as "search hijackers."
Pieter Arntz, malware intelligence researcher with the security firm, explained in a blog post that these search hijackers are all about directing unsuspecting visitors to sponsored ads:
Every time someone clicks on a sponsored advertisement, the requisite search engine earns money on a pay-per-click basis. They are paid by advertisers, who shell out for beneficial placement in the search results for keyword phrases of their choice.
While searching for new variants of an established family of search hijackers, Arntz came across some websites advertising WebNavigator. This was the first clue that the web browser and the search hijackers were connected.
Digging into those websites itself, Arntz found that whoever designed them had used the same layout that tells users how to install a Chrome extension. Those individuals just changed the text to provide instructions for installing their web browser.
The final indication came when Arntz tested out the browser and found that it added graphic search recommendations into a user's search results.
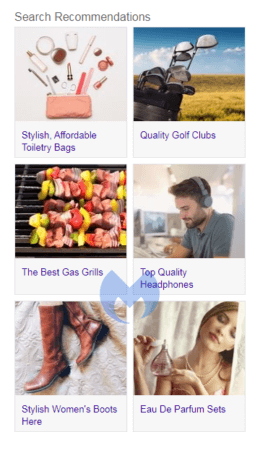
These recommendations led to the types of sponsored advertisements referenced by Arntz above.
Malwarebytes detected this program as PUP.Optional.WebNavigator at the time of writing.
The emergence of browsers like WebNavigator highlights the need for organizations to augment their email and web browser protections. Towards that end, they can use the Center for Internet Security's Critical Security Control #7. Information on how to implement that security measure is available here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

