
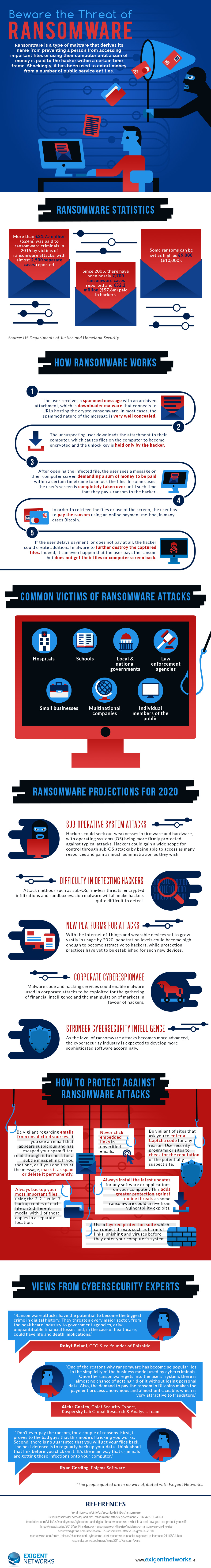
The recent WannaCry ransomware attack left thousands of businesses in more than 150 countries worldwide reeling, with countless Internet users coerced into paying a Bitcoin ransom in the hope they'd regain access to their critical files. For all the advances that have been made by IT security providers to halt such malicious online activity, the expertise of black hat hackers is evolving at a quicker pace, so there remains considerable scope for improvement to halt future ransomware attacks like WannaCry. Where does ransomware protection go from here? Attack methodology, such as sub-OS, file-less threats, encrypted infiltrations and sandbox evasion is likely to make hackers even more difficult to ensnare. Sub-OS attacks could be especially problematic, as hackers look for chinks in firmware and hardware to bypass greater protective measures of the operating system. With these types of low-level forays, hackers’ scope for control is massive, as they could gain access to as many resources and as much administrative power as they wish. The Internet of Things (IoT) and wearable devices could also help hackers instigate ransomware attacks. These devices and concepts have not been in existence long enough for adequate protection to be established. Lastly, the WannaCry attacks highlighted the firm possibility of future attacks at the corporate level, with malware potentially being exploited for the accumulation of financial information. It could even be used by hackers to tamper with markets and manipulate them in their favor. This infographic from Exigent Networks explains more about ransomware and predicts what the situation could be like by 2020. As the infographic and the WannaCry attacks both demonstrate, ransomware protection has a long way to go to catch up to the resources at hackers’ disposal.

About the Author: Orla Forrest is a marketing executive with Ireland-based network solutions provider Exigent Networks. She has worked with the company for more than six years and boasts a large degree of experience in the IT solutions sector. She is highly literate on technological matters and frequently writes content around key issues within the field. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

