
What's happened? A widespread vulnerability has been found in WordPress, that impacts millions of websites running the popular blogging software and content management system. What's the vulnerability? It's a cross-site scripting (XSS) vulnerability inside the popular JetPack plugin. and the default Twenty Fifteen theme installed on all WordPress sites. The problem lies in the genericons package, specifically a file called example.html. Any plugin which makes use of the package is potentially vulnerable. If a website administrator was tricked into clicking on a malicious link, the vulnerability can be exploited to hijack the website - making changes to it code or altering settings. Who found the vulnerability? David Dede, a researcher with security firm Sucuri, uncovered the problem and blogged about it yesterday:
"The main issue here is the genericons package, so any plugin that makes use of this package is potentially vulnerable if it includes the example.html file that comes with the package. That means the XSS payload is never sent to the server side and is executed directly at the browser." "What is interesting about this attack is that we detected it in the wild days before disclosure."
In the wild? Dede means that evidence has been seen of attackers exploiting the vulnerability before it was disclosed and before remediations were available. Yuck Yes, quite. How did this bug get onto so many websites? In short, the WordPress team goofed up by shipping a file which contained the vulnerability in its default install package: In his blog post, Dede is clear that the WordPress guys are responsible for putting sites at risk:
"We cannot forget one of the basic principles of security, in which we must maintain a pristine environment in production. This means we remove debug or test files before you move into production. In this case, Automattic and the WordPress team left a simple example.html file that had the vulnerability embedded. What’s more concerning here is the reach the plugin and theme have combined; they are installed in many cases, by default in all WordPress installations. Simple oversight, that could have devastating impacts on unsuspecting website owners and businesses alike."
It's hard to argue with that. So what can be done? The brute force solution is to remove the genericons/example.html file from your WordPress installation. But a better solution is probably to upgrade to the newly released security update for WordPress (4.2.2).

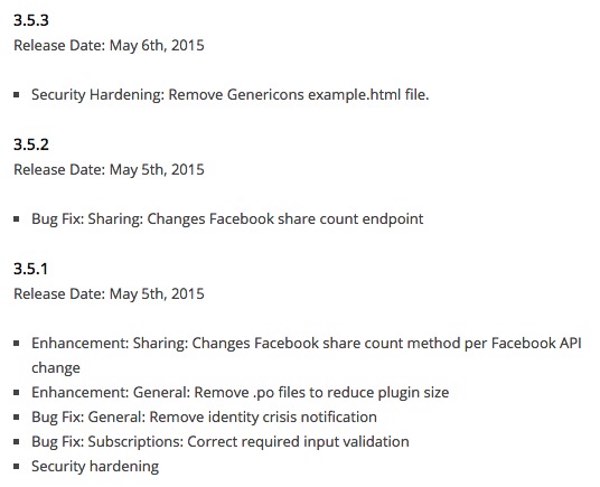
Updating WordPress has the advantage of fixing a number of other bugs too. Kudos to the WordPress security team for addressing the problem so quickly. Can I configure WordPress to automatically update itself? Yes you can. Since WordPress 3.7 was released in October 2013, the software has come with the ability to automatically update itself. Automatic updates are not for everyone of course, and many site admins working inside organisations are nervous of rolling out new versions of software on their websites before they have a had a chance to test that they won't introduce other problems. The sad truth, of course, is that many websites out there are still running older, vulnerable versions of WordPress where this may not be the only exploit that could be exploited. Shouldn't I also update JetPack? If you've updated the WordPress software then you don't *have* to update the JetPack plugin as well, but it's probably recommended anyway. Automattic, the developer of JetPack, has released version 3.5.3 of the plugin which reportedly fixes the problem. So, once again, it's a case of WordPress users being required to update their plugins to ensure they are protected. A look at JetPack's changelog reveals that administrators self-hosting their own installations of WordPress should be no stranger to updating that particular plugin - this appears to have been the third update in about 24 hours, although not all of them are for security reasons.
Keeping WordPress safe from threats is a real pain Yes, if you run WordPress on your website (as many millions of sites do) then it does come with some responsibilities. Fortunately, Sucuri says that it notified a number of the most popular webhosts to ensure that they had already patched the security hole on the sites they host, saving you some of the hassle. Those hosts include GoDaddy, HostPapa, DreamHost, ClickHost, Inmotion, WPEngine, Pagely, Pressable, Websynthesis, Site5 and Siteground. It's possible that your webhost has also taken action to reduce the threat to your site, but frankly I recommend always taking some ownership of the security of your website. After all, it's your brand that's at stake and your company's relationship with its customers which could be at risk. My website is at example.wordpress.com. That means I'm using WordPress, right? Am I at risk? It's important to differentiate between the different versions of WordPress. When I refer to self-hosted installations of WordPress, I mean when folks install the open-source WordPress software on a web server themselves and can tweak it in a wide variety of ways. Although it's true that many millions of websites run WordPress in this self-hosted fashion (known as wordpress.org), there are also many millions of users who are either less technically-minded or don't want the hassle of running their own WordPress installation, who choose to host their site on wordpress.com instead. If you are running your site on wordpress.com, then security doesn't need to be anything like as much as a priority for you because the (very competent) people who run that site are responsible for its updating and security and already limit just how much you can do with your site in terms of the themes and plugins you can use. In effect, it's a bit like a "walled garden". If you find the similarity in names between wordpress.org and wordpress.com somewhat confusing, you're not alone. But, in answer to your question, if you're using wordpress.com you are not at risk. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

