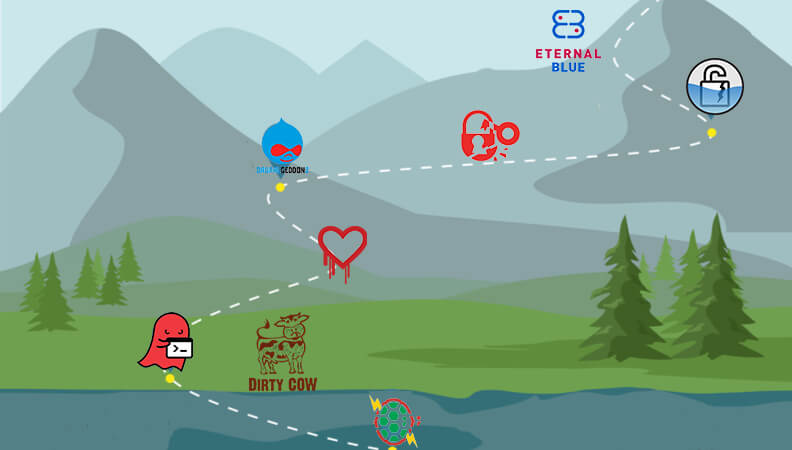
The purpose of this series of blogs is to guide you on your journey up the Vulnerability Management Mountain (VMM). Like climbing a mountain, there is a lot of planning and work required, but when you get to the top, the view is amazing and well worth the journey. Your progress will depend on your funding and priorities, but climbing at a quick steady pace will help secure your environment. As we climb, you will progress up the Vulnerability Management Maturity Model, and this process will be reusable over and over when new groups, organizations or acquisitions are brought in.
Step 1: Equipment and Preparations
It is inadvisable to just decide to start climbing a mountain without any preparations. The same holds true for Vulnerability Management Mountain (VMM), and doing so will lead to frustration and failure. To prepare for VMM, we build out our plan, and the equipment includes Tools, a plan (map) and companions.
The Plan (aka Map)
You would not climb a mountain without a map, and a vulnerability management plan serves that purpose here. This plan will not be static, and you are expected to make changes and notes as you progress. When a landslide has blocked a path, mark it and then draw in the alternative route. Here are some things to think about before you start.
Equipment
You can’t climb a mountain without the right gear, and the same holds true here. There are a lot of tools, both commercial and open source, that help you on this journey. You have the option of using a VM suite that will combine most of the tasks for you in a single product or which you can use to pick and choose tools to do the specific tasks. There are pros and cons to each tool and method, so choose what you feel most comfortable with and know that you can change if the tool is not working for you or you can use more than one. Having a backup is always a good idea.
Partners
It is advisable to climb with a partner, and the same holds true for climbing VMM. In this case, your partners include penetration testing teams (Pen Team) and trusted security advisors. The pen testing team can be internal or external, and they will assess the network and applications by combining various methods that are not as easy to deploy in a single VM application. Your trusted security advisors generally come from the commercial company you are buying tools from, business partners or industry contacts solving the same issues. When you buy a commercial VM tool, you should have access to a support organization that understands not only the product but VM best practices and the vulnerabilities themselves. A good vendor will also give you access to the team that writes the vulnerability content and does the research. Your business partners and industry contacts are key here, too, because information sharing is important to stay ahead of the threats. You are not expected to share your vulnerability information, but share news and trends in what attacks are occurring, share best practices and even share what is working and not working for the situation.
Network Layout
Unless you have a small flat network, you are going to need to decide how you want to break up your network for assessment. One large network assessment will return a ton of data that will be hard to sift through and will cause frustration. Start whiteboarding this layout now, and we will tweak it as needed in the coming steps. Some popular ways to divide up networks are by:
-
- Functional Group or Business Unit – HR, Engineering, Finance, Sales, DMZ, etc.
- Owners – Which System Administrations own the systems
- Geographical location – Countries, States, cities, etc
Okay, now go off, do your homework and draw up your map. In the next post, will we prep and start the climb.
Further reading on climbing the vulnerability managment mountain:
- Climbing the Vulnerability Management Mountain
- Climbing the Vulnerability Management Mountain: Gearing Up and Taking Step One
- Climbing the Vulnerability Management Mountain: Taking the First Steps Towards Enlightenment

