
Vulnerabilities are weaknesses leveraged by adversaries to compromise the confidentiality, availability or integrity of a resource. The vulnerability ecosystem has matured considerably in the last few years. A significant amount of effort has been invested to capture, curate, taxonomize and communicate the vulnerabilities in terms of severity, impact and complexity of the associated exploit or attack. Standardization in the description of vulnerabilities contributes not only to effective threat intelligence sharing but also to potentially efficient threat management if organizations, vendors and security researchers employ vulnerability management techniques and practices to actively seek to discover the vulnerabilities and respond in a timely fashion. Significant efforts are being made to standardize this information to reduce communication barriers and complexity, leading to a more effective analysis of vulnerabilities and a better understanding of the context within which different vulnerabilities are discovered. However, due to the challenges of categorizing vulnerabilities, these efforts are fraught with difficulty. Vulnerability data can be incomplete, inaccessible or inaccurate, and the quality of the resulting information has an impact on decision making, policies, and practices. Moreover, the vulnerability disclosure is influenced by a variety of factors, including financial incentives, the agenda of the disclosing stakeholder and the interaction of the various actors. Additionally, it’s important to note that this is all performed in a highly dynamic information security market.
The ENISA Report on the State of Vulnerabilities
To identify and highlight all the issues pertaining to effective vulnerability information sharing, ENISA collaborated with CERT-EU and academia to analyze and provide insight into both the opportunities and limitations that the vulnerability ecosystem offers. Using the vulnerabilities published during the year of 2018 and Q1-Q2 of 2019 as a vehicle, the ENISA “State of Vulnerabilities 2018/2019” report attempts to answer questions related to the reliability, accuracy of the vulnerability sources and the widely accepted evaluation metrics. This study aims to address these challenges by completing three objectives:
- Represent the state of cybersecurity vulnerabilities in a form that allows stakeholders to make informed decisions on cybersecurity investments.
- Comprehensively analyze and correlate vulnerability data to better contextualize vulnerabilities.
- Analyze vulnerability data from a quality and reliability perspective.
Additionally, the report leverages the ATT&CK vulnerability taxonomy to explore and identify more intrinsic relationships and characteristics. The end goal of the report is to help the information security community, public/private organizations and vendors to make informed decisions about patching, prioritization of security controls and to improve their risk assessment process.
Vulnerabilities’ Standardization
Frequently, disclosed vulnerabilities are uniquely identified in accordance with the Common Vulnerabilities and Exposures (CVE) referencing system developed by MITRE. However, not all publicly disclosed vulnerabilities have an associated CVE-ID. Vulnerabilities kept private and not publicly disclosed are often referred to as “zero-day vulnerabilities,” and the corresponding exploits are referred to as zero-day (0day) exploits. The severity of the impact of a vulnerability is defined using the Common Vulnerability Scoring System (CVSS) maintained by the Forum of Incident Response and Security Teams (FIRST). It is often provided as a qualitative value (Low, Medium or High) based on a quantitative calculation derived from the characteristics of individual vulnerabilities. The current CVSS version is v3.1, implemented in June 2019, but v2.0 values are often quoted for vulnerabilities prior to June 2015 when v3.0 was published. The modern vulnerability lifecycle depicted in the figure below identifies significant milestones and events that define risk transitioning boundaries. The significance of risks increases as vulnerabilities trigger the creation of the associated exploits and decrease when the patches become available.
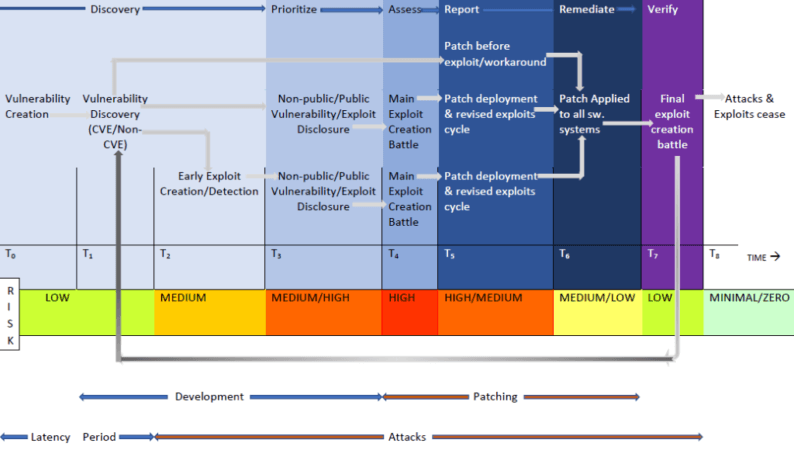
Figure 1: Vulnerability Lifecycle. Source: ENISA
Key Findings
The report provides a thorough analysis of the vulnerabilities’ datasets from January 2018 to August 2019. It’s is worth reading it to learn some of the key findings. It’s apparent there are inconsistencies and discrepancies between the different sources. Although there is an authoritative database capturing vulnerability details, this does not imply that the information in that database is accurate. These inconsistencies have certain implications for organizations. Relying solely on one source – no matter how authoritative it may be – will lead an organization to potentially miss vital vulnerability information that affects their systems. In addition, although capable of providing a good reference for assessing, understanding and contrasting the impact and severity of vulnerabilities, the CVSS scoring system does not necessarily make up the “ground truth,” as other stakeholders may have a different view on the severity of a vulnerability. Comparing the vulnerabilities over ATT&CK tactics, it is also evident that there is an uneven distribution. Defense Evasion, Persistence and Discovery are the preferred tactics for the exploits while Exfiltration, Initial Access and Impact tactics are not represented in the dataset.
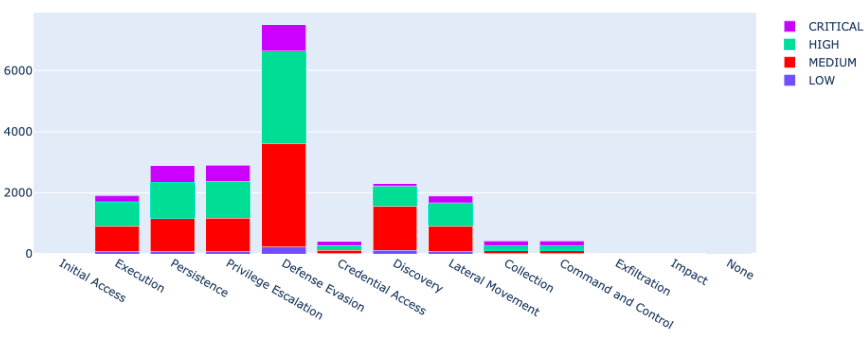
Figure 2: Vulnerabilities vs ATT&CK tactics and CVSS v3 base score. Source: ENISA There are significant differences between the two vulnerability measurement systems (CVSS v2 and CVSS v3) regarding the underlying recorded values, as well, which leads to different severity classifications. This is possibly attributed to the different wording of the categorical variables, thus creating a subjective bias that may, in turn, affect the risk management, planning and decision-making processes.
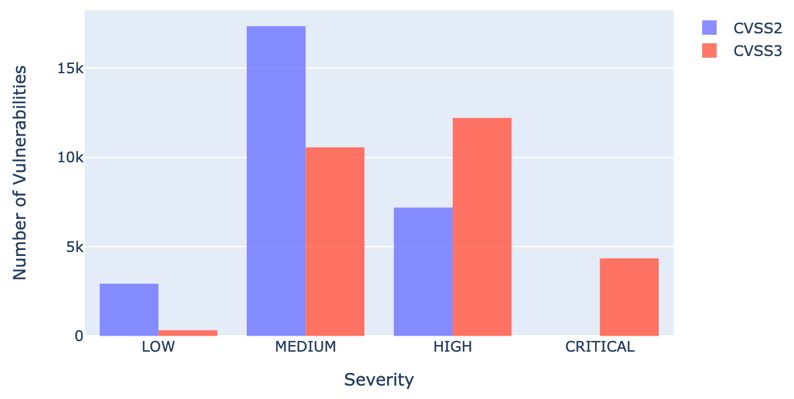
Figure 3: CVSS2 vs CVSS3. Source: ENISA Microsoft has the highest number of vulnerabilities (600), which is more than 50% higher than the runner-up, Qualcomm. From an ATT&CK framework perspective, Cisco and Canonical have highly scoring vulnerabilities across the range of the tactics, whereas Microsoft is ranked among the lowest.
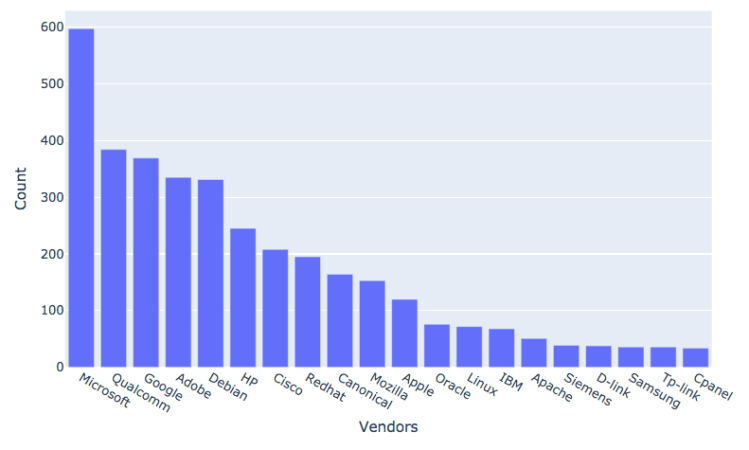
Figure 4: Vendors with most CVEs. Source: ENISA The exploit publication date of CRITICAL vulnerabilities is close to the vulnerability publication date, with the most exploits being published shortly before or after the vulnerability publication date. The top 10 weaknesses account for almost two thirds (64%) of the vulnerabilities. Most exploits target web and client-side related vulnerabilities. A considerable amount of activity surrounds vulnerabilities that do not enter the CVE ecosystem, or if they do, it happens at a very late stage. Using the Zero Day Initiative (ZDI) dataset, ENISA concluded that there are statistically significant differences between the severity level of CVE (officially recorded) and non-CVE vulnerabilities (i.e. those that were not listed or included in the CVE databases), with the latter showing a higher score. At least 8.65% of the vulnerabilities are exploitable. This number is expected to be higher due to zero-day exploits and the incompleteness of the datasets.
Conclusion
The ENISA report is an indication of the potential to generate intelligence, make informed decisions, and perform risk assessment exercises on software vulnerabilities. The systematic efforts of the computer security community to create a taxonomy and develop databases populated by structured vulnerability descriptors pave the way for a deeper exploration of the vulnerability ecosystem. Tripwire is a strong proponent of an effective vulnerability management program. You may learn more by reading this anthology.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

