
Microsoft announced its Identity Bounty Program through which security researchers can earn up to $100,000 for an eligible submission. On 17 July, Microsoft Security Response Center (MSRC) unveiled the creation of a new bug bounty program to help it remediate vulnerabilities affecting its Identity services. Phillip Misner, principal security group manager of MSRC, noted that security today depends largely upon protecting a customer's digital identity. This helps explain Microsoft's commitment to identity-based solutions, as Misner said in a blog post:
Modern security depends today on collaborative communication of identities and identity data within and across domains. A customer’s digital identity is often the key to accessing services and interacting across the internet. Microsoft has invested heavily in the security and privacy of both our consumer (Microsoft Account) and enterprise (Azure Active Directory) identity solutions. We have strongly invested in the creation, implementation, and improvement of identity-related specifications that foster strong authentication, secure sign-on, sessions, API security, and other critical infrastructure tasks, as part of the community of standards experts within official standards bodies such as IETF, W3C, or the OpenID Foundation. In recognition of that strong commitment to our customer’s security we are launching the Microsoft Identity Bounty Program.
According to its terms and conditions, the Microsoft Identity Bounty Program welcomes reports detailing previous unreported critical or important vulnerabilities that affects one of its in-scope Identity services. Those include account.live.com and Microsoft's mobile Authenticator app, amongst others, as well as several standards such as OpenID Connect Core and OAuth 2.0 Form Post Response Types. Certain issues such as reports from automated scans, denial-of-service (DoS) flaws and vulnerabilities likely requiring user interaction aren't in scope. When it comes to the rewards security researchers can receive for an eligible submission, the amounts vary widely. Participants can expect to make at least $500 for an incomplete submission detailing an authorization flaw or instance of sensitive data exposure. On the other end of the spectrum, they can earn up to $100,000 for a high-quality submission disclosing enough information for an engineer to reproduce, grasp the specifics of and fix a multi-factor authentication bypass or standards design vulnerabilities.
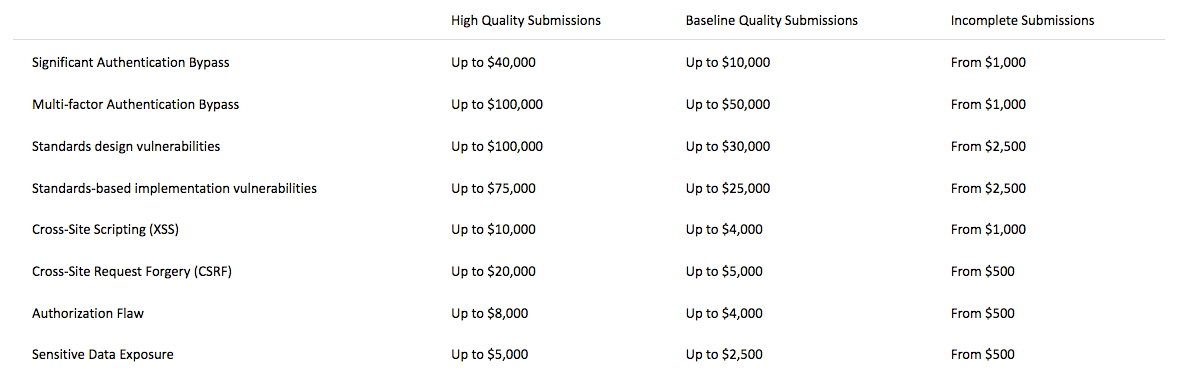
The reward scheme for the Microsoft Identity Bounty Program Microsoft notes that participants of its Identity Bounty Program must avoid privacy violations and the destruction of data. They are also prohibited from using certain methods of research such as DoS testing, automated security testing and phishing testing against company employees. Researchers are required to set up test accounts and test tenants in order to look for security issues. Specifically, they can create an Azure free trial and/or a Microsoft test account. News of this program follows approximately two months after Microsoft launched a limited-time bug bounty program to help discover and address vulnerabilities similar to Spectre and Meltdown.

