Cybersecurity awareness, protection, and prevention is all-encompassing. In addition to implementing the right tools and resources, and hiring skilled professionals with the right cybersecurity education and experience, organizations should be aware of the latest CVEs.
What Is a CVE?
The acronym “CVE” stands for Common Vulnerabilities and Exposures, and it refers to known computer security flaws that have been publicly identified and documented.
The National Institute of Standards and Technology (NIST) defines a CVE as: "A weakness in the computational logic (e.g., code) found in software and hardware components that, when exploited, results in a negative impact to confidentiality, integrity, or availability.”
A reference to a specific CVE means that the flaw has been assigned a specific identification number and logged into the official CVE system, which is run by the MITRE Corporation with funding assistance from the Cybersecurity & Infrastructure Security Agency (CISA).
As of mid-December 2021, a total number of 165,133 CVEs had been recorded since the system was first devised.
How Does the System Work?
CVE entries are concise, detailed accounts. They do not include technical data; that information appears in other databases, including the U.S. National Vulnerability Database (NVD), and the CERT/CC Vulnerability Notes Database.
Here is an example from 2021:
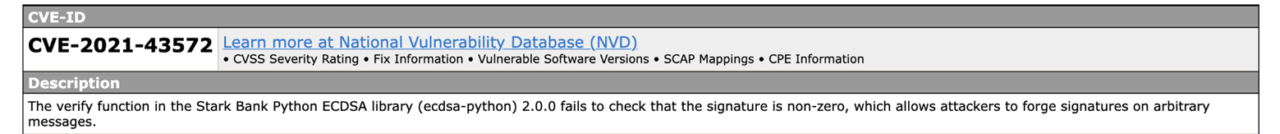
CVE reports can come from vendors, researchers, cybersecurity professionals — essentially from anyone who deals with these types of security issues.
The CVE Numbering Authority (CNA) is composed of software vendors, open source projects, coordination centers, hosted services and research groups; CNA members are authorized by the CVE Program to assign CVE numbers and publish CVE records.
Organizations and businesses that are CNAs include Adobe, Apple, Google, IBM, Microsoft and Intel. There are minimal requirements to become a partner, a relationship that includes no fees or contracts.
Here is a brief explanation of how the CVE system works:
- A vulnerability or exposure is identified;
- The vulnerability or exposure is assigned a CVE number by the CNA;
- The CNA creates a description of the issue and provides references;
- The completed CVE entry is added to the comprehensive list and published on the official CVE website.
Why Are CVEs Important?
The more information a business or organization can access about potential exposures and vulnerabilities, the better.
As BMC Software explains:
“The CVE Project is a great resource for all IT organizations to use. It’s especially important for researchers and product developers to utilize CVE entries and to use products and services that are compatible with CVE. Additionally, it’s important to always be looking for vulnerabilities in software and to share any that your organization finds when using open-source software. Further, it’s key to communicate about vulnerabilities internally and externally to help prevent attacks and to efficiently resolve issues.”
If you’re wondering whether criminals can use the CVE list to their advantage, the answer is yes — but the risks outweigh the benefits. As the official FAQ explains, these flaws are publicly known issues, so it’s likely that cyber criminals already know about them.
Top CVE Trends
A 2021 report from CISA details the top 30 CVEs “routinely exploited by malicious cyber actors in 2020 and those being widely exploited thus far in 2021.”
Some of the most targeted vulnerabilities in 2020 and 2021 affected remote work, VPNs or cloud-based technologies, according to the report.
Cognyte released a report earlier this year, outlining the top CVE threats of 2021. Some of the most notable ones include:
- Microsoft Office memory corruption
- A remote code execution vulnerability
- Vulnerability in Microsoft products
Threatpost, a news site focusing on IT and business security, outlined the six CVEs most popular with criminals, some of which include:
- Privilege vulnerability
- Remote code execution vulnerability
- Microsoft Office/WordPad remote code execution vulnerability with Windows
How to Protect Your Business
Cyber attacks are frequent — as evidenced by the constant news reports about such crimes — but there are steps you can take to protect your business, including:
- Limiting employee access to data and information.
- Regularly patching operating systems and software.
- Installing and activating software and hardware firewalls.
- Securing wireless access points and networks.
- Using encryption for sensitive information.
- Training your employees in security awareness.
Additional cybersecurity best practices include:
- Avoiding pop-ups, emails from unknown senders, and unfamiliar links.
- Using strong passwords and multi-factor authentication.
- Connecting to secure Wi-Fi.
- Investing in security systems.
- Talking to your IT department.
CVEs aren’t entirely avoidable, but proper education and awareness are crucial components of cybersecurity protection. The CVE framework identifies vulnerabilities and exposures that could become a problem for your business or organization now — or in the future.
About the author: Michelle Moore, Ph.D., is an academic director and professor of practice for the University of San Diego’s innovative online Master of Science in Cyber Security Operations and Leadership program. She is also a researcher and author with over two decades of private-sector and government experience as a cybersecurity expert.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

