Fortra's Tripwire protects the world’s leading organizations against the most damaging cyber attacks. Our solutions work on-site and in the cloud to find, monitor and minimize a wide range of threats without disrupting daily operations or productivity. Think of us as the invisible web of detection that keeps systems safe.
Imagine becoming more effective and efficient at securing your infrastructure. Tripwire has always been the leader in file integrity monitoring (FIM) and change control, but we offer much more. Our solutions provide superior security, continuous compliance and reliable operations for enterprises, industrial organizations, service providers and government agencies. Tripwire solutions combine essential capabilities that deliver breach detection, remediation and compliance, while addressing nearly every compliance standard—PCI DSS, NIST, FISMA, NERC, HIPAA, ISO/IEC 27002, DISA, SOX, and many others.
Tripwire Enterprise: Security Configuration Management and File Integrity Monitoring Made Easy
Tripwire Enterprise pairs the industry’s most respected FIM with security configuration management (SCM) to provide real-time change intelligence and threat detection. For the compliance officer, it delivers proactive system hardening and automated compliance enforcement—resulting in a reduction of audit cycles and cost.
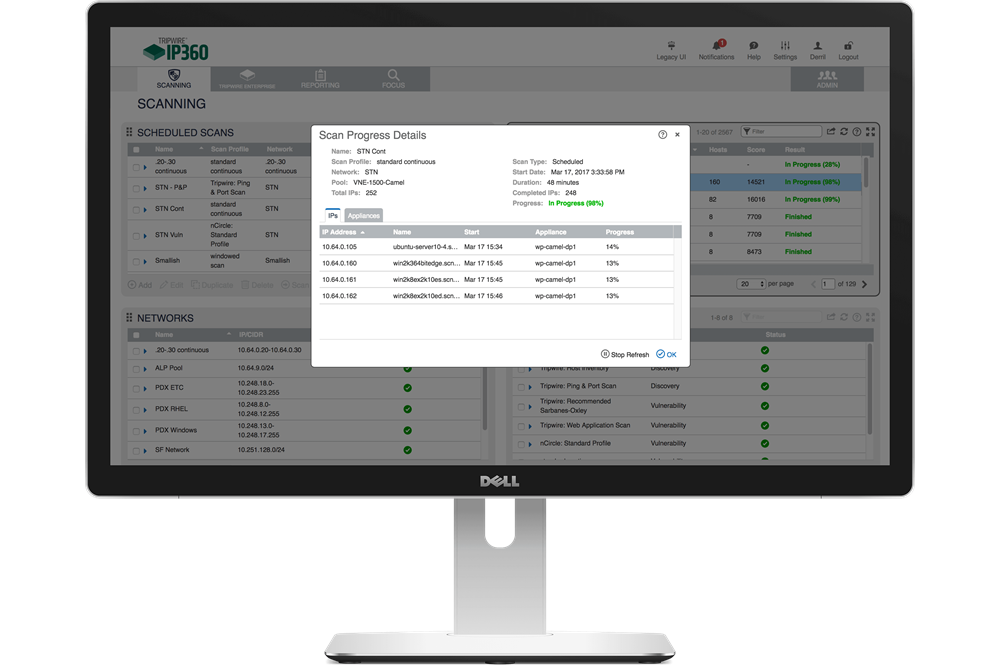
Tripwire IP360: The Definitive Vulnerability Management Solution
Tripwire IP360™ proactively discovers, profiles and assesses the vulnerability risk of your organization’s assets and can stand as the fundamental solution of your vulnerability management (VM) program. It enables fast detection of vulnerabilities, granular prioritization of risk, and remediation management.
Tripwire ExpertOps: Managed Security and Compliance
Tripwire ExpertOps delivers a cloud-based managed services model of the industry’s best SCM and VM. A single subscription includes personalized consulting from trained experts and hands-on tool management to help you achieve and maintain compliance and critical asset security.
More Tripwire Products
Better Together
While each product in the Tripwire portfolio provides valuable capabilities in a stand-alone implementation, customers receive maximum value when they are integrated—with each other or with third-party products—to achieve faster and more accurate security and compliance in both IT and OT environments.
Tripwire integrates with a wide array of third-party products to offer a multitude of benefits and use-cases in these distinct categories:
- Threat intelligence
- Network security
- Analytics and security information and event management (SIEM)
- IT service management (ITSM)
- Integrated access management (IAM)
- Industrial control systems (ICS)
- Factory automation systems (FAS)
- Government risk compliance (GRC)
- DevOps workflow tools
You’ll gain a significant advantage against operational inefficiencies with Tripwire integrations. These integrations automate the sharing and validating of critical data and intelligence. They also drive productivity by enabling richer collaboration between your IT operations and security teams.
Tripwire provides the advanced foundational controls that should serve as the bedrock for your security and compliance efforts. Known and trusted, we keep complex digital systems protected in a world of unknowns.
Get Started Today
See how we protect the world's leading organizations against the most damaging cyber attacks.