Accurately detect and protect against advanced and evasive threats by combining Tripwire Enterprise security configuration management with FireEye threat intelligence and malware analysis.
Discover Risks
Use Tripwire to detect suspicious changes and flag unauthorized files.
Use Tripwire to detect suspicious changes and flag unauthorized files.
Evaluate Threats
Use FireEye to analyze suspicious files to determine if they are malicious.
Use FireEye to analyze suspicious files to determine if they are malicious.
Correct Problems
Apply Tripwire workflows and remediation guidance to fix compromised systems.
Apply Tripwire workflows and remediation guidance to fix compromised systems.
Catch Zero-Day Attacks
Use FireEye to confirm malware with full-system sandbox emulation.
Use FireEye to confirm malware with full-system sandbox emulation.
Leverage Tripwire and FireEye for Optimal Situational Awareness
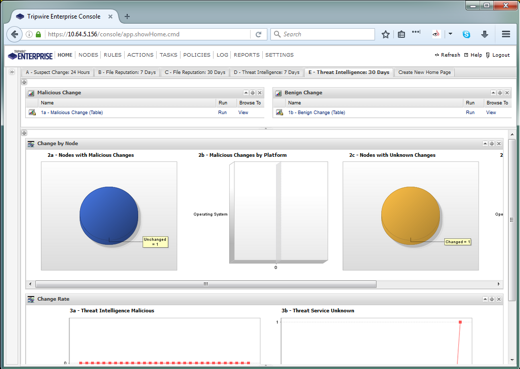
Tripwire Enterprise integrated with FireEye greatly enhances your ability to detect and defend against advanced persistent threats and zero-day attacks. Use Tripwire to monitor for suspicious activity, and then use FireEye’s Threat Analytics Platform (TAP) to differentiate benign changes from malicious threats. Zero-day malware can be tested using FireEye’s full-system emulation sandbox technology.
Image
Image
Reduce Security Vulnerabilities in SCADA and ICS environments
The combination of Tripwire solutions, FireEye iSight technology and Mandiant incident response services provides best-in-class solutions for addressing increasingly sophisticated cyberattacks targeting critical infrastructure systems.
Find out more about Tripwire / FireEye Integrated Solutions
Not Sure Which Product Is Right for You?
Contact one of our security and compliance experts to understand your needs and match them with the best Tripwire solution.