Many organizations face the challenging threat environment by strategically choosing a security controls framework as a reference for initiating, implementing, measuring, and evaluating their security posture, as well as managing risk. While many frameworks are available, one of the most notable and commonly used is the Center for Internet Security’s CIS Controls.
This well known framework has the goal of offering combined knowledge and proven guidance for protecting confidentiality, integrity, and availability of critical assets, infrastructure, and information. Security controls themselves are technical safeguards and operational procedures that strengthen defenses against threats. They typically involve the triad of technology, people, and process and when implemented and automated.
One of the main reasons organizations put off choosing a security controls framework is the fear that it may be too large an undertaking and will not get completed. However, security is a job that is never done, and getting started is essential. If your organization is serious about improving its security posture, it should have a strategic plan, a framework and a set of security controls against which progress can be measured and evaluated. The CIS Controls help guide organizations by starting with implementing the most critical controls and work their way to implementing all 20.
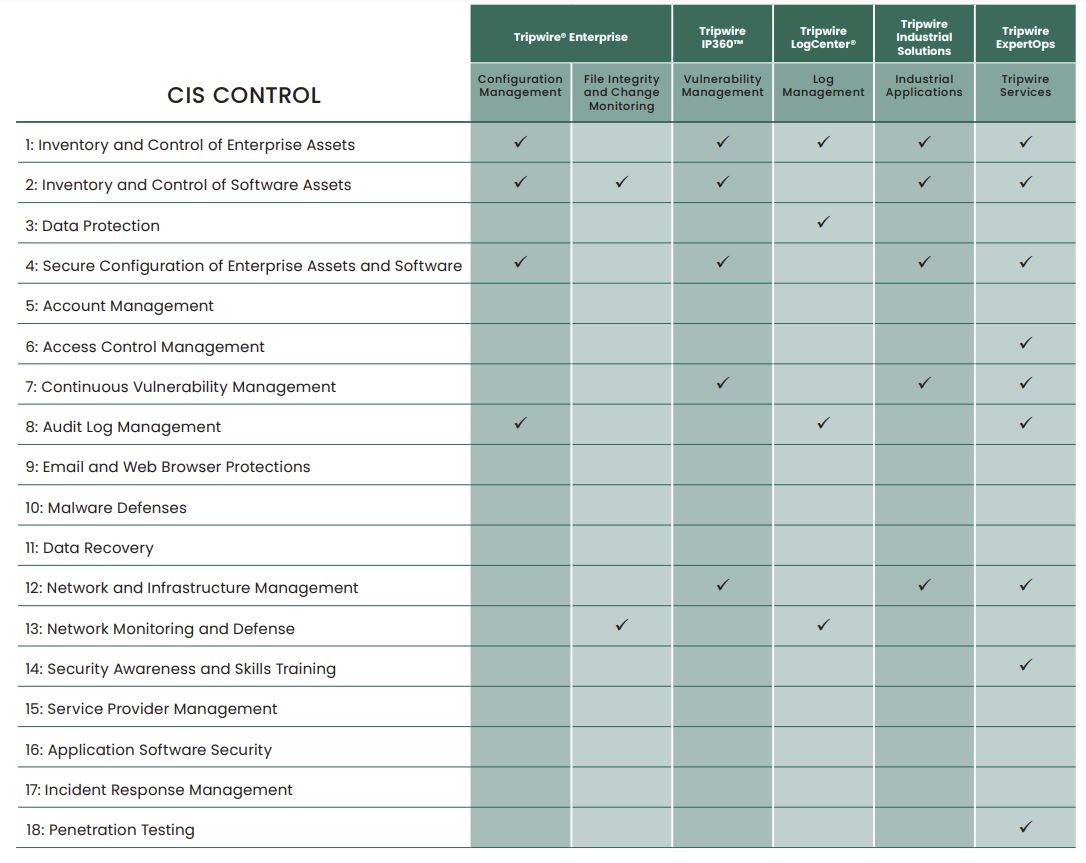
Fortra's Tripwire provides solutions that align with each of the Controls, as well as many other other security control frameworks. Tripwire can accelerate your organization’s efforts to evaluate risk, improve security, and achieve immediate short term wins and long term confidence.
CIS Controls Overview
The CIS Controls (formerly known as the SANS Top 20 Critical Security Controls) reflect the combined knowledge of actual attacks and effective defenses as well as exclusive and deep knowledge about current threats by a broad range of industry experts. The Controls are a foundational reference and starting point for any organization..
Background
- A prioritized, agreed upon set of “most critical controls,” heavily informed/drawn from NIST SP 800 53
- Developed by a consortium of information security experts
- Customizable and applicable regardless of organization size, type (government or commercial), maturity level, likely threat vectors, or technologies in use
- Recommended for use by Verizon’s Data Breach Investigations Report to address the majority of breaches they investigate.
- Provides detailed guidance to prioritize implementation and customize your security controls as well as sequence, test, and achieve continuous automation Regardless of your organization’s starting point, there is a lot of implementation flexibility. Tripwire solutions enable faster adoption of your chosen security framework as they meet key criteria, multiple controls, continuous monitoring automation, and the evolving threat environment.
Accelerate Security Management
Security control frameworks give freely researched and broadly validated guidelines for protecting confidentiality, integrity, and availability of critical assets, infrastructure, and information. Tripwire knows that some of the biggest security gains against the most common threat vectors can be simply and inexpensively achieved by starting with the foundational controls, as documented in the CIS Controls framework. Implementing Controls 1 through 5 assures that you know your network assets and what’s on them (e.g. hardware, software, configurations, locations, etc.), and that their configurations are in a secure, hardened state regularly scanned for vulnerabilities, policy compliance and other weaknesses. And finally, that as they are discovered, issues are remediated. Getting started is the most important step, and the CIS Controls apply to nearly any enterprise.
Schedule Your Demo Today
Let us take you through a demo of Tripwire security and compliance solutions and answer any of your questions.