Tripwire provides out-of-the-box integration of Tripwire® Enterprise, a security configuration management solution, and Tripwire LogCenter®, a complete log management and SIEM solution. By joining these solutions, you can automatically correlate changes detected in Tripwire Enterprise with log and event data captured by Tripwire LogCenter.
Combined, they grant immediate visibility to file and configuration changes, along with information about the context in which those changes were made. This added risk context helps security professionals prioritize changes based on risk to the business.
By joining forces, Tripwire Enterprise and Tripwire LogCenter offer visible, actionable intelligence with several outof-the-box, real-time integration points:
Change/Event Correlation Provides Change and Risk Context
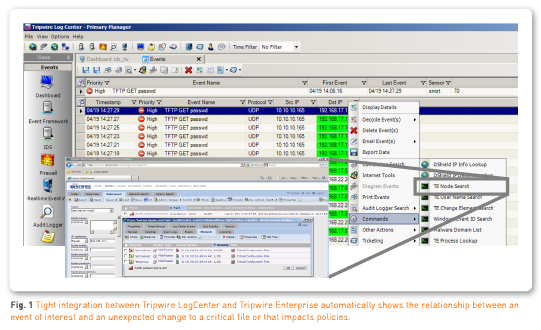
Any SIEM can detect a security event. It’s far more powerful when a SIEM can show you that there’s a relationship between an event and an unexpected change to a critical file or setting. This reduces false positives and focuses your incident detection efforts on the events that actually matter.
The out-of-the-box integration between Tripwire Enterprise and Tripwire LogCenter automatically correlates changes that impact policies with events detected by Tripwire LogCenter. By providing this real-time visibility into changes and their context through consoles and dashboards, it’s far easier to identify impending threats.
Bi-Directional Context Enables Forensic Discovery and Investigation
Quickly find vulnerabilities, respond to attacks and recover from breaches. The integration between Tripwire Enterprise and Tripwire LogCenter provides contextual controls that give you unprecedented levels of visibility and intelligence. For example, in Tripwire Enterprise you can investigate suspicious activity on a server, device or other IT asset by seeing related security events from Tripwire LogCenter—all without leaving the console you work from most. Similarly, from Tripwire LogCenter you can view the Tripwire Enterprise asset associated with an event of interest to inspect potentially related changes detected on that asset.
Global Event Search Reveals Trends and Threats
Save time by obtaining more accurate and comprehensive results from your queries. Identify unexpected threat patterns faster. In Tripwire Enterprise you can now execute standards-based queries against log and event information captured by Tripwire LogCenter. This can provide hard evidence of a threat to back up a gut suspicion. It can also reveal an anomaly that may indicate the seeds of a coordinated attack. For example, you can query for all files changed by a specific user or for “portmap scanning” messages that can reveal an external threat.
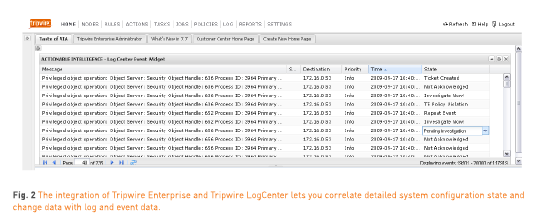
Tripwire LogCenter “Event Widget” Displays Real-Time Information
Save time finding security incidents and out-of-compliance status. A Tripwire LogCenter event widget can now be placed in Tripwire Enterprise dashboards (Fig. 1) to provide real-time event information from Tripwire LogCenter for monitored servers, applications and devices. Status updates to these events are made in Tripwire Enterprise and then updated in Tripwire LogCenter upon synchronization. Plus, Tripwire Enterprise and Tripwire LogCenter continue monitoring the infrastructure to protect critical files and systems, detect incidents at the speed of change, and remediate issues before damage is done.
The Tripwire Enterprise and Tripwire LogCenter Integration in Action
Tripwire Enterprise indicates that a file share’s configuration settings have been changed to allow anyone to access critical data anonymously. Whenever someone accesses this file share, Tripwire LogCenter sends you an alert. Clearly there’s a problem. To fix the problem, you return the configuration to its previously known and trusted state using automated remediation in Tripwire Enterprise. In this case, it fixes the configuration setting so that it prohibits guests and unauthorized users from accessing the files. and requires each user to authenticate to view the material. The next time an unauthorized user or perpetrator tries to login to the system, access is denied. Problem solved.
Hyperlogging Rapidly Re-Enables Critical Logs That Have Been Disabled
Reduce the risk associated with gaps in logging coverage and satisfy requirements for logging continuity. Hyperlogging rapidly and automatically re-enables logging of critical logs that have been disabled—an action hackers or malicious insiders often take to cover their tracks. Tripwire Enterprise detects when logging systems in Tripwire LogCenter have been disabled and immediately re-enables them. It also provides reports to auditors and real-time alerts of compliance violations.

Tripwire Enterprise Agents Deliver Instant Log Data
Enable deep logging on different systems without difficult, manual efforts. The integration helps you meet this longstanding log management need much more easily. Take advantage of Tripwire Enterprise agents that are already deployed to immediately send detailed system state, change and configuration information to Tripwire LogCenter. If you’re an existing Tripwire Enterprise user, you can obtain this instant logging capability with a simple console upgrade if your deployed agents are version 7.5 or higher.