The financial services market is a key target for cyber criminals given potential financial rewards. Their motives can also be political since financial systems are critical infrastructure for society. The New York State Department of Financial Services (DFS), the regulatory body that oversees financial services companies licensed by or operating in the state, has been closely observing the ever- growing threat posed to information and financial systems by nation-states, terrorist organizations and independent criminal actors.
DFS has mandated new rules, Part 500 of Title 23 of the Official Compilation of Codes, Rules and Regulations of the State of New York, or 23 NYCRR 500 for short, that require the financial services organizations covered and licensed by them to establish and maintain a cybersecurity program. The regulation was developed based on a survey of regulated banking institutions and insurance companies, and consultations with cybersecurity experts. While 47 states in the US have adopted different breach notification statutes, individual states have not yet adopted broad cybersecurity mandates; New York is the first. “… designed to promote the protection of customer information as well as the information technology systems of regulated entities. This regulation requires each company to assess its specific risk profile and design a program that addresses its risks in a robust fashion.” (www. dfs.ny.gov/legal/regulations/adoptions/ rf23-nycrr-500_cybersecurity.pdf)
The effective date for the new regulation is March 1, 2017, and covered entities have 180 days from that date to comply with the rules. A further requirement to provide a Certification of Compliance to the DFS will commence January 2018. The regulation language does not include fines if entities are not in compliance, but DFS has a reputation for levying steep fines.
“Although still much more prescriptive than what we’ve seen out of other regulators, the revised regulations are now more flexible and tied more closely to each organization’s particular risk assessment,” said Edward McAndrew, a partner at Ballard Spahr, who serves as co-leader of his firm’s Privacy and Data Security Group. “That said, they have teeth and will require substantial investment of time and resources to ensure initial and ongoing compliance. … I fully expect other states to follow suit with similar regulations both in the financial services and other industries.” (www. scmagazine.com December 29, 2016)
Achieve 23 NYCRR 500 Compliance With Tripwire
Tripwire has a proven track record with many cybersecurity regulations (e.g. PCI, NERC CIP, SOX, HIPAA) and frameworks (e.g. NIST, CSC 20). Tripwire automates cybersecurity regulatory compliance, allowing organizations to not only achieve compliance but also reduce time spent preparing for and maintaining compliance through continuous monitoring and audit-ready evidence. In addition, Tripwire offers an open architecture with integrations to many other tools to enhance security and operations.
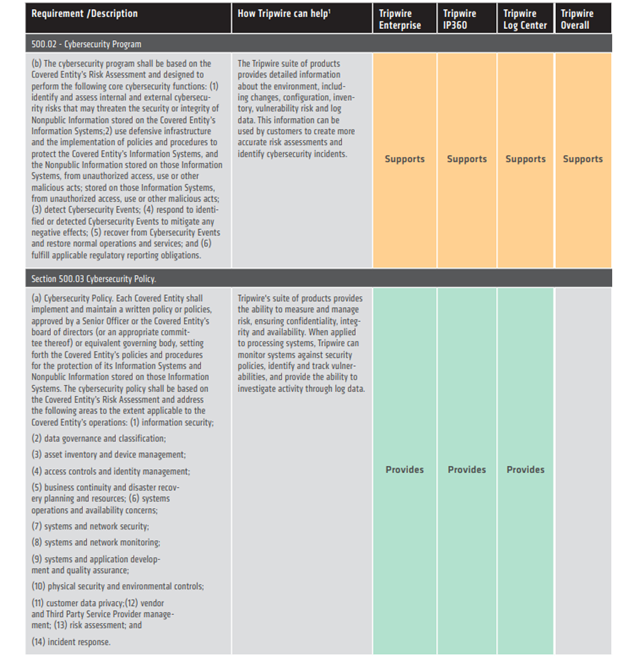
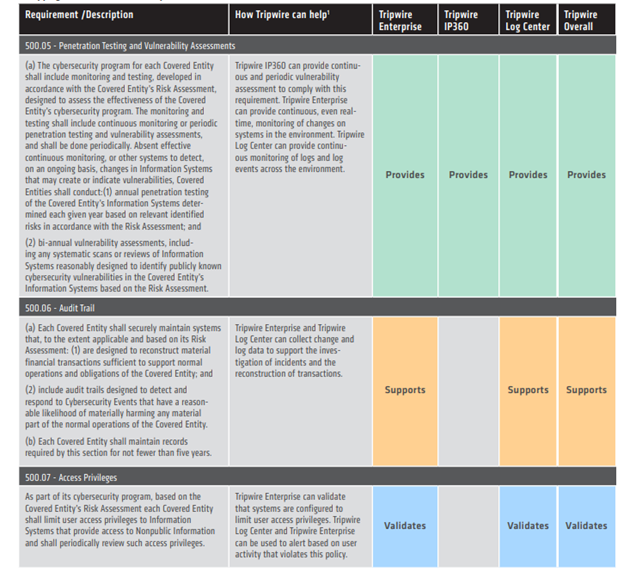
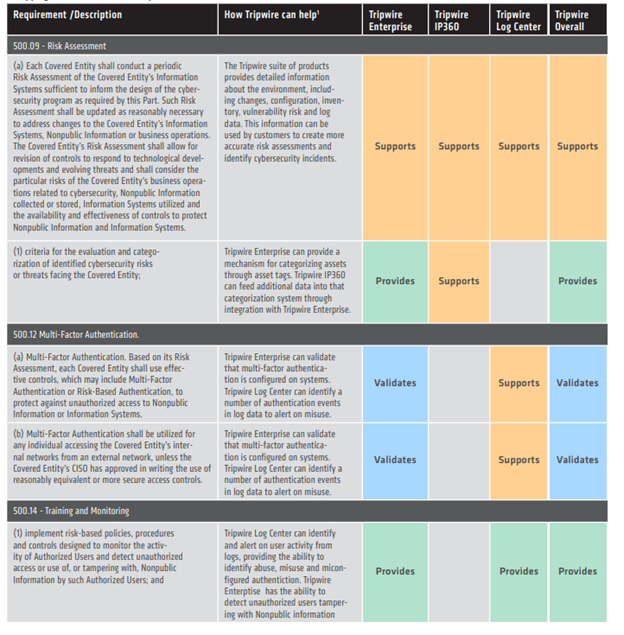
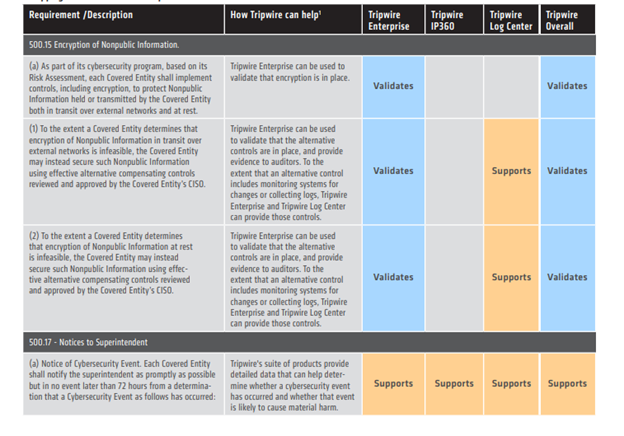
The new DFS regulations require that organizations take a programmatic, risk-assessment based approach to secure non-pubic information and the organization’s information systems. Tripwire’s suite of products can provide specific required controls, validate that organizations are in compliance with the standard, and support compliance by providing relevant data and reports. Tripwire’s core capabilities for integrity monitoring, policy compliance, vulnerability management and centralized log collection are vital to achieving and maintaining compliance with 23 NYCRR 500.
Mapping of 23 NYCRR 500 to Tripwire Products