Is your vulnerability management program ready for DevOps, cloud infrastructure, and the evolving threat landscape? Many organizations have already developed a mature VM program for their traditional enterprise and application platforms. But radical new shifts in the tech ecosystem mean you will need to protect your systems on new platforms and processes against a wide assortment of potential vulnerabilities.
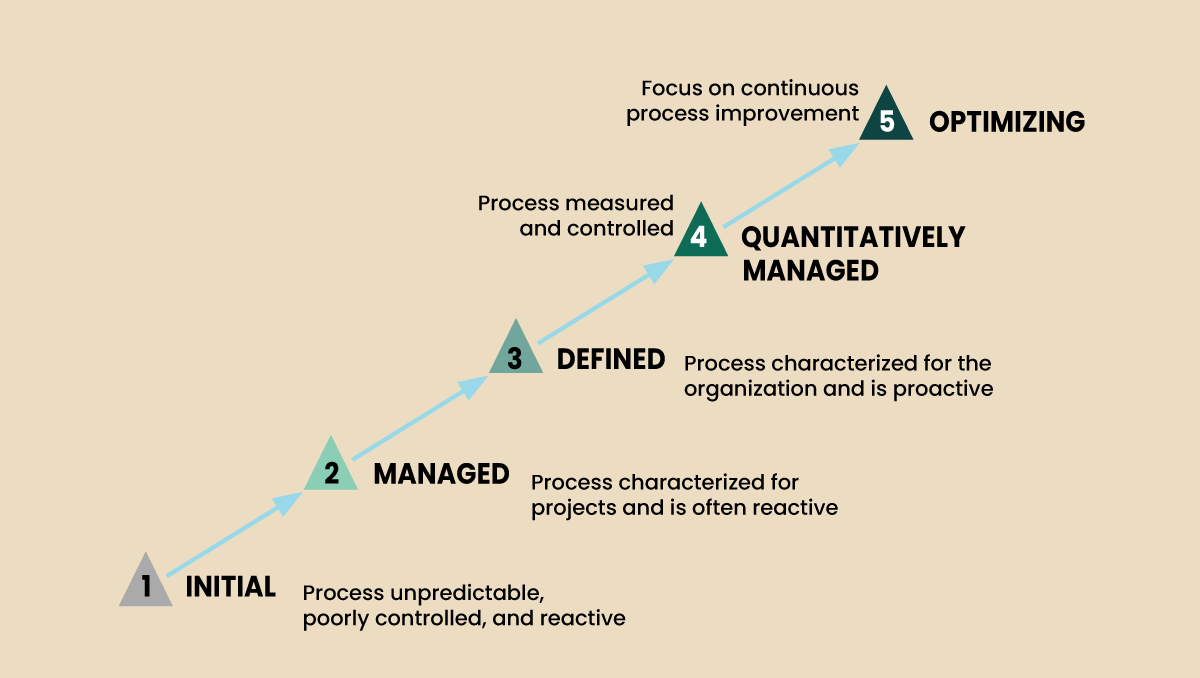
This paper outlines the five stages of VM maturity to help you determine where you are and what work is required to improve your program—even in the face of emerging DevOps and cloud complications. The need for on-demand and real-time assessment is now more critical than ever as security programs need to keep up with current trends.