
A security researcher has released an updated list of 500 million breached passwords so that organizations can use it to protect their systems. On 22 February, Australian web security expert Troy Hunt published the second version of "Pwned Passwords." The feature enables users to check a new or used password against a list of 501,636,842 combinations previously compromised by data breaches. In so doing, organizations can leverage the feature to ensure users are choosing secrets that are unaffected by any known security incidents. People can either download the entire list or use an online search tool to verify their passwords. If they choose the latter, the utility will notify users if their password is contained in the list. It will also display a number that indicates how many times the service found their secret across the various data sources of which it consists.
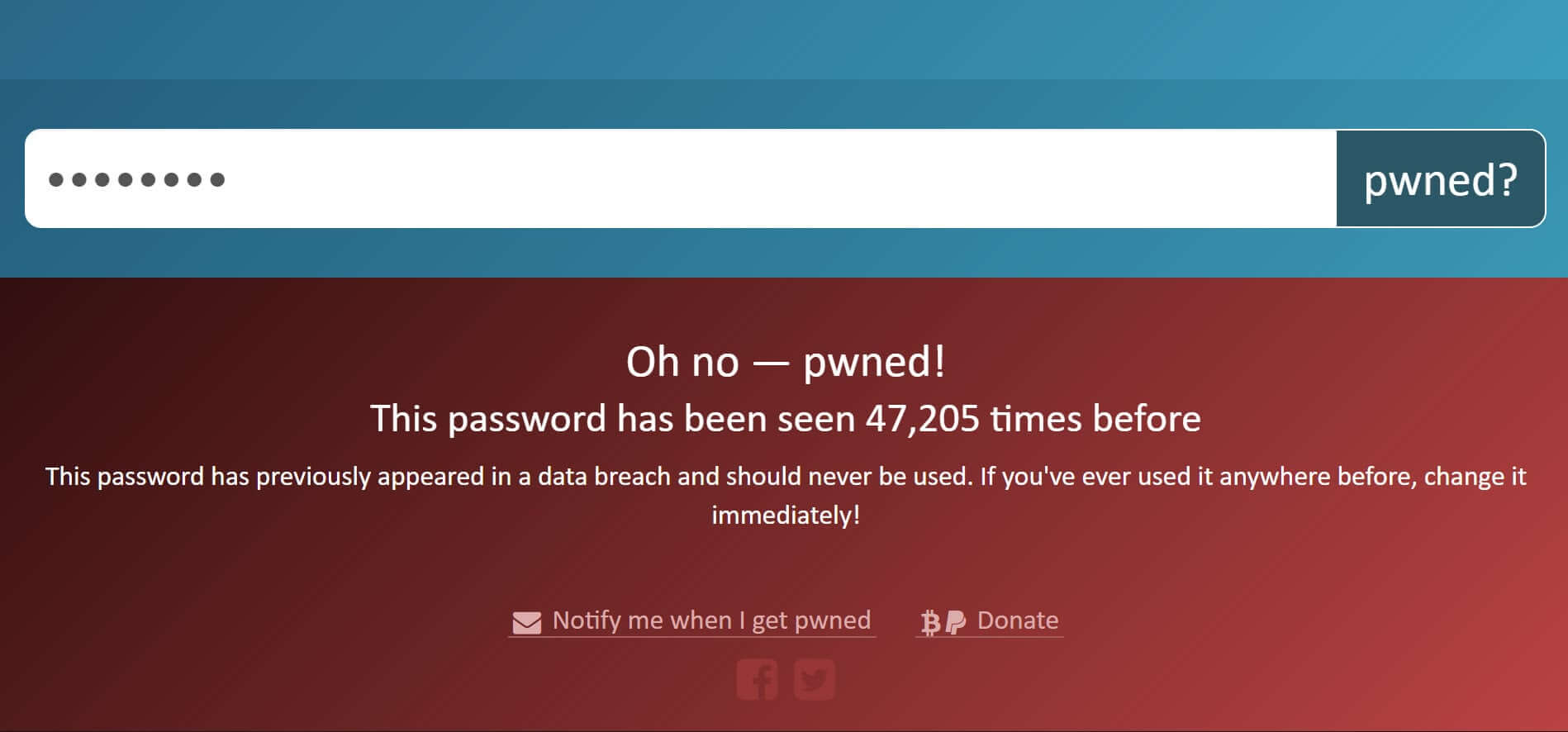
Pwned Passwords v2 (Source: Troy Hunt) Such a feature has many potential applications in the security world. 1Password recognized one when it integrated the feature's k-Anonymity model into its password manager. This fusion lets users gauge their exposure should they choose to opt into 1Password's new option. https://twitter.com/troyhunt/status/966798677577576448 As with the first version of the feature, Hunt decided to SHA-1 hash the entries contained in Pwned Passwords. He did so not because he thinks SHA-1 is a sufficiently robust algorithm for protecting sensitive data like passwords. Rather, he believes it's important to "to ensure that any personal info in the source data is obfuscated such that it requires a concerted effort to remove the protection, but that the data is still usable for its intended purposes." The data contained in Pwned Passwords isn't perfect, either. CynoSure Prime examined the feature and identified junk strings contained in some of its entries. The security researcher says those strings make up a fraction of a fraction of the item's overall data size. He also admits he's not trying to create something that's perfect:
This list is not perfect - it's not meant to be perfect - and there will be some junk due to input data quality and some missing passwords because they weren't in the source data sets. It's simply meant to be a list of strings that pose an elevated risk if used for passwords and for that purpose, it's enormously effective.
To learn more about Pwned Passwords v2, check out Hunt's blog post here. The updated feature is contained within Have I Been Pwned, Hunt's service which allows people to verify if a security incident such as the Wishbone data breach has exposed their email addresses or usernames.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

