Image

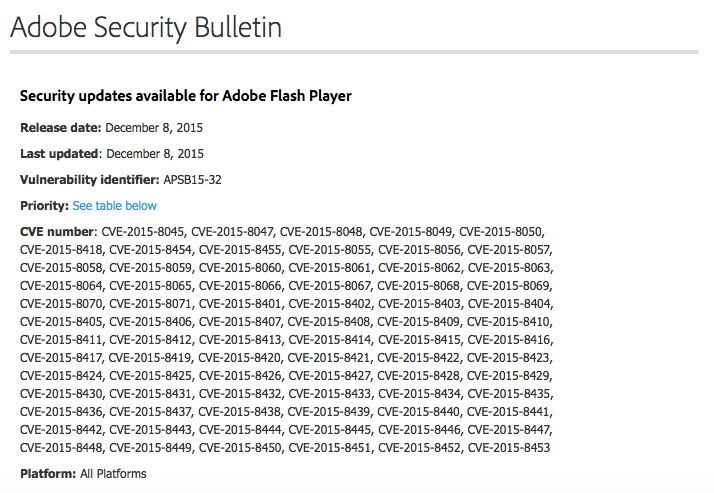
Adobe has patched 79 "critical" vulnerabilities affecting Flash Player in its December 2015 security bulletin. The alert, which bears the vulnerability identifier APSB15-32, warns that all platforms are affected by the flaws. This includes Windows and Macintosh regarding the Flash desktop version 19.0.0.245 and earlier, as well as the Google Chrome, Microsoft Edge, and Internet Explorer (10 and 11) browsers.
"Adobe has released security updates for Adobe Flash Player," the bulletin reads. "These updates address critical vulnerabilities that could potentially allow an attacker to take control of the affected system."56 of the vulnerabilities identified by Adobe are use-after-free bugs that could lead to code execution. The alert also addresses a dozen memory corruption vulnerabilities and two heap buffer overflow flaws, among other issues.
Image
“All but three of the vulnerabilities could be used by an attacker to gain code execution running under the user in the browser. From there a second vulnerability would have to be used to become system on the machine (look at MS15-135 for an example), but then the attacker would have full control.” Qualys CTO Wolfgang Kandek said in a post on his company's blog, referencing the 12 security bulletins recently published by Microsoft (analysis here). “Flash-based attacks have been a favorite for attackers for the year with many exploit kits providing very up-to-date exploits - include this in your high priority items.”Adobe recommends that users download the newest version of Flash Player as soon as possible. You can do so here. The Register observes that for many developers, users, and site operators, the size of this bulletin is another indication that Adobe should discontinue Flash Player altogether. This is in part motivated by research demonstrating that even if the browser-facing components of Flash are disabled, attackers can still inject code and exploit vulnerabilities. Adobe recently re-branded Flash Professional as Animate, which some in the industry have indicated is a sign that the company wishes to ultimately phase out Flash. But this development is more of a change in name only, leading The Register to identify removal of Flash as "the only option". If removal is impossible, investigative infosec journalist Brian Krebs recommends using a dual-browser approach or enabling Click-to-Play, a feature which lets you activate certain Flash content when you load up a page.

