
A security firm has discovered a variant of Android ransomware that masquerades as a pornography app called "Adult Player." According to a post published on Zscaler's blog, the ransomware, which is not found on legitimate app stores like Google Play Store and the Apple App Store, successfully loads onto a device after asking for admin permissions. It then uses a technique known as reflection to load test.apk from its local storage. If the front camera is enabled, it snaps a picture of the user, which it later displays on the ransom page. Next, the ransomware connects to four hard-coded domains (hxxp://directavsecurity[.]com, hxxp://avsecurityorbit[.]com, hxxp://protectforavno[.]net, and hxxp://trustedsecurityav[.]net), to which it sends information about the victim's device including the product build and OS version.
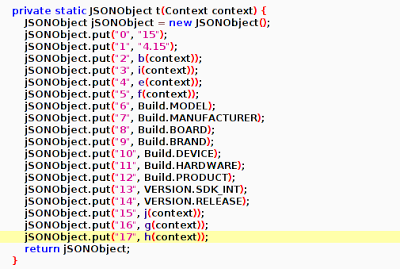
Data sent by requests (Source: Zscaler) Finally, the malware displays a ransom page purporting to originate from the FBI and warning the victim that their device has been locked after having discovered "forbidden pornographic sites." It asks for a $500USD fine to unlock the device. News of this ransomware follows the release of McAfee Labs' Threat Report: May 2015, a publication which observed a 165% increase in ransomware over the first quarter of 2015.
"One of the reasons for the increase is that it's very easy to make," Raj Samani, chief technology officer for Intel Security in Europe, told BBC News. "There are people you can pay to do the work for you, and it pays really well. One group we tracked made more than $75,000 in 10 weeks. Apps like this rely on the embarrassment factor. If you don't pay, your reputation is on the line."
The ransomware cannot be removed via a reboot of the device, as the malicious program becomes active again immediately after reboot. For a complete guide that explains how to remove the ransomware off of an infected device, please click here. To learn more about ransomware in general, including tips on how you can protect yourself from becoming a victim, click here.

