
An Android trojan is using SMS phishing texts (or "smishing" messages) to prey upon unsuspecting South Korean mobile users. In July 2017, users uploaded to South Korean websites screenshots of texts asking them to click on suspicious shortened links. One message warns recipients that someone might have leaked a private picture of them to the web. Another claims the user had made it into the news.
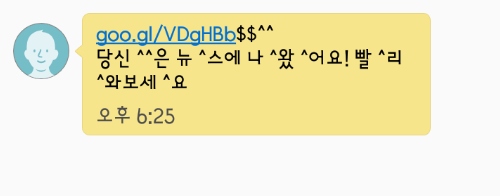
Figure 2: “You are in the news! Please check.” (Source: Naver) For those who click the link using a non-Android device like an iPad, the campaign redirects them to a security page for the search engine Naver. Android users, meanwhile, receive a prompt to download a "new version of Chrome ... with enhanced features." This APK asks for several unusual permissions, like the ability to place calls, read text messages, and access a device's saved contacts. Approving these rights establishes persistence for the program, which is in actuality a form of malware known as "Android/MoqHao." The trojan doesn't waste any time making the most out of its administrator access. McAfee's Jaewon Min and Carlos Castillo elaborate on Android/MoqHao's behavior after it conceals its app icon on an infected device:
"First, Android/MoqHao dynamically registers a broadcast receiver for various system events such as new package install, screen state, SMS messages, and so on. This broadcast receiver spies on the device and sends device status information to the control server. "Next, Android/MoqHao connects to the first-stage remote server. The IP for second-stage control server communication is dynamically retrieved from the user profile page of Chinese search engine Baidu...."
The above-referenced server receives an initial message from the malware consisting of basic information pertaining to an infected device. Thereafter, Android/MoqHao periodically sends over status data like the device's battery level and Wi-Fi signal level. But that's not all it does. Whenever the infected device receives an SMS text message, the trojan transmits the sender address and contents to its server. Android/MoqHao also attempts to steal a user's banking credentials by attempting to download fake or trojanized versions of popular mobile banking apps. Finally, it uses a fake alert message to try to steal data pertaining to a user's Google account, like their name and birthday, off a phishing page.
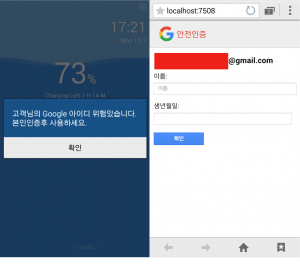
Alert message: “Your Google identity is at risk. Please use it after you certify yourself.” (Source: McAfee) Trojans such as Android/MoqHao should serve as a reminder to users to install applications from only trusted sources and to not click on suspicious shortened links. Even with developers whom they do trust, users should not authorize the installation of any apps that request an unusual number or quality of device permissions. Finally, they should install an anti-virus solution onto their phones and consider enabling two-step verification (2SV) on each of their web accounts that offers the feature.

