
A hacker group known as the Armada Collective is currently targeting secure email services with prolonged blackmail distributed denial-of-service (DDoS) attack campaigns. Last week, Geneva-based encrypted email service ProtonMail announced that it had been temporarily knocked offline by a DDoS attack. After issuing a post explaining what it was doing to correct the ongoing downtime, the email service decided to pay the $6000 ransom demanded by the attackers--a hacker group that calls itself the Armada Collective. But the onslaught did not end.
"Attacks against infrastructure continued throughout the evening and in order to keep other customers online, our ISP was forced to stop announcing our IP range, effectively taking us offline," the company says, as reported by ZDNet. "The attack disrupted traffic across the ISP's entire network and got so serious that the criminals who extorted us previously even found it necessary to write us to deny responsibility for the second attack."
To the company's surprise, the attackers even began sending Bitcoin back to ProtonMail, presumably in an effort to distance itself from the follow-up DDoS attack campaign.
“Somebody with great power, who wants ProtonMail dead, jumped in after our initial attack!” read one note by the criminals, according to Forbes. Another read: “We have no such power to crash data center and no reason to attack ProtonMail any more!”
It might be possible that someone is using the Armada Collective name to go after ProtonMail. Whoever they are, the group is capable of conducting devastating DDoS attack campaigns against its targets:
"Our attacks are extremely powerful - sometimes over 1 Tbps per second. So, no cheap protection will help," reads the group's generic ransom note, which is available on Graham Cluley's website.
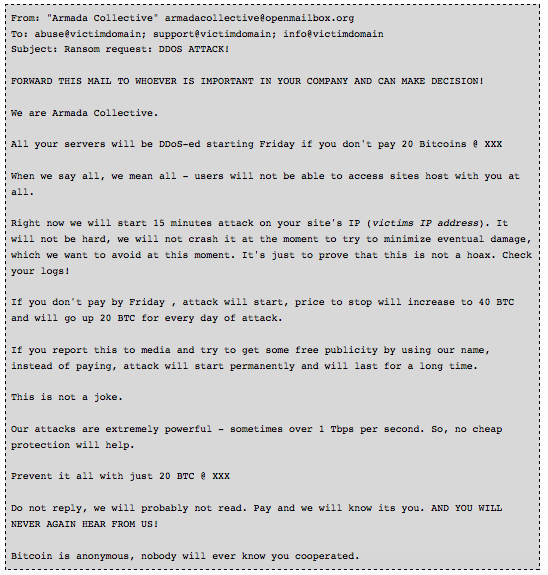
The Armada Collective's full ransom note (Source: Swiss Governmental Computer Emergency Response Team) This month alone, in addition to attacking ProtonMail, a group of criminals claiming themselves to be the Armada Collective has targeted a number of other secure email services, including Hushmail, Neomailbox, VFEmail, and Runbox, as well as business solutions provider Zoho.com. These campaigns follow after the group's targeted attacks against four Thai banks last month. Notwithstanding its ongoing operations, some feel that the group's tactics, which are not unlike that of fellow ransom DDOS-based hacker group DD4BC, will ultimately be the group's undoing. Andy Yen, head ProtonMail, told Forbes over Skype that he believes the hackers are now “feeling the heat”.
“They know they are being hunted,” he said.
Businesses that run a website are encouraged to maintain up-to-date security software and implement patches as soon as possible in order to avoid being hijacked by a botnet--a common DDoS machine. It is also recommended that organizations investigate anti-DDoS solutions to help avoid downtime should they be targeted by a group like the Armada Collective.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

