In June 2016, researchers at Sucuri Security tracked a distributed denial-of-service (DDoS) attack against one its customers. The campaign consisted of a layer 7 attack (HTTP Flood) that generated 50,000 requests per second (RPS) for several days. Such intensity is not by itself unusual. What made this campaign stand out, however, was the attackers' use of more than 25,000 CCTV devices to keep up the traffic level. DDoS attacks have been around for decades but as Sucuri's research illustrates, this type of attack continues to grow in frequency, size and complexity each year. That is also the overarching finding of Arbor ATLAS 1H 2016 DDoS Update, a report published by Arbor Networks, which provides DDoS attack data for the first six months of 2016. Provided below are some of the major findings from the study.
Increased Size, Sophistication and Steadiness
For its report, Arbor Networks relied on ATLAS, a partnership of 339 service provider customers that contributed with anonymous information regarding today's threat environment. Their intelligence together offers a comprehensive look into the current state of DDoS attacks. DDoS campaigns continue to be a steady fixture in the world of digital threats. Indeed, the ATLAS network tracked 124,000 events each week between January 2015 and June 2016. In the first six months of 2016 alone, ATLAS spotted 274 attacks over 100Gbps (versus 223 in all of 2015) and 46 attacks over 200Gbps (versus 16 in all of 2015). Arbor Networks also saw a rise in the number of attacks targeting DNS and HTTPS, as well as port 4444.
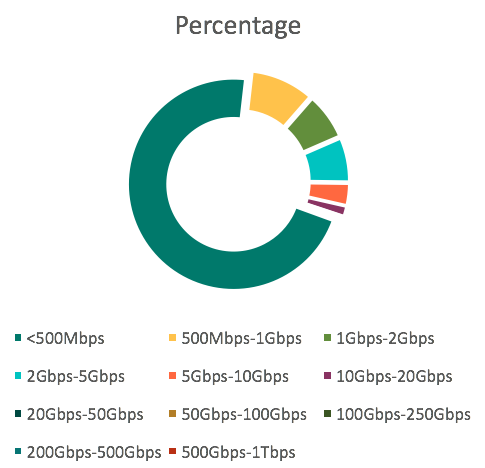
In addition to higher frequency, DDoS attacks increased in both peak and average attack size in 1H 2016. In 2014, the peak size was 325 Gigabits per second (Gbps). That bumped up slightly to 354 Gbps in 2015. But then 2016 arrived, and with it a 73 percent growth in peak attack size to 579 Gbps. Similarly, the peak attack size in 2015 was 377.15 million packets per second (Mpps), but in 1H of 2016, the size increased by 28 percent to 481.6 Mpps. As for average attack size, DDoS attacks in 1H 2016 averaged at about 986 Mbps. That number represents a 30 percent growth over 2015, and it is expected to increase to 1.15 Gbps by the end of 2016. Given this increase in size, it's not surprising only 80.9 percent of attacks registered at less than 1 Gbps, as compared to 84 percent in 2015. Large DDoS attacks don't need to use reflection amplification techniques due to the rise of botnets like LizardStresser. Even so, DDoS campaigns that rely on such tactics continue to grow in size and complexity. These types of campaigns leverage DNS, NTP, and SSDP, with DNS the most widely employed protocol in 2016. The peak monitored reflection amplification attack size in 1H 2016 was 480 Gbps, and it used DNS to get the job done. Acknowledging the increase in frequency, size, and complexity of attacks in 1H 2016, Darren Anstee, Arbor Networks Chief Security Technologist, explains organizations require a layered defense system to defend against today's DDoS campaigns.
"The data demonstrates the need for hybrid, or multi-layer DDoS defense. High bandwidth attacks can only be mitigated in the cloud, away from the intended target. However, despite massive growth in attack size at the top end, 80 percent of all attacks are still less than 1Gbps and 90 percent last less than one hour. On-premise protection provides the rapid reaction needed and is key against 'low and slow' application-layer attacks, as well as state exhaustion attacks targeting infrastructure such as firewalls and IPS."
For expert recommendations on how you can protect your network against a DDoS attack, click here and here.

