
Digital criminals have launched a new attack campaign that they're using to target U.S. petroleum companies with the Adwind RAT. Netskope discovered the operation in the beginning of September and found that it was distributing the Adwind RAT from “members[.]westnet[.]com[.]au/~joeven/.” With this URL in mind, it's likely that the individual responsible for the campaign either compromised someone's account for Westnet, an Australian ISP, or was a Westnet user at the time of the attack. Researchers also observed that multiple Westnet users appeared to be hosting the same RAT, with some of them using multiple file extensions such as *.png.jar.jar to conceal the malware's actual file format from a targeted user. This campaign differed from other recent Adwind attacks in that it used multiple embedded JAR archives as a means of obfuscation before unpacking the malware payload. That being said, the operation didn't stray too far from the pack in its use of time-tested techniques. It still created a registry key to maintain persistence, and it leveraged WMI scripts to disable firewalls and/or antivirus services running on the infected computer.
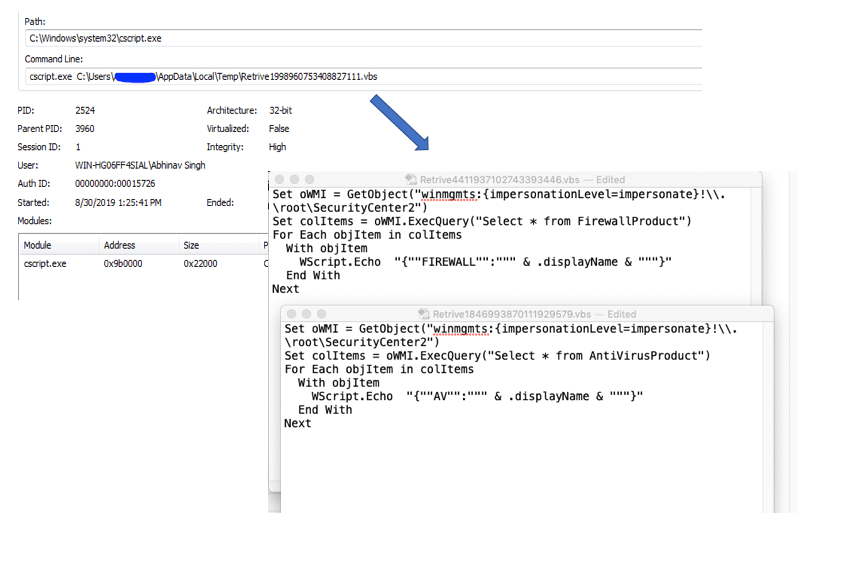
WMI scripts created by the first stage JAR payload. (Source: Netskope) Ultimately, the campaign loaded a DLL containing Adwind's main functionality. This malware was cross-platform in nature, and it arrived with the ability to capture webcams, encrypt and exfiltrate data as well as perform other tasks. In its analysis, Netskope noticed that the individual responsible for the campaign had encountered some success in helping their campaign evade detection. As quoted in its research:
The samples we analyzed showed that the VirusTotal detection ratio for the top-level JAR was 5/56 while that of the final decrypted JAR was 49/58. These detection ratios indicate that attackers have largely been successful in developing new, innovative obfuscation techniques to evade detection.
This conclusion on the part of Netskope highlights the need for organizations to defend themselves against ever-evolving malware families. They can do this by investing in a sophisticated tool that's capable of tracking known malware signatures and spotting behavior that's indicative of zero-day threats. Learn how Tripwire can help in both respects.

