What is this AvosLocker thing I’ve heard about?
AvosLocker is a ransomware-as-a-service (RaaS) gang that first appeared in mid-2021. It has since become notorious for its attacks targeting critical infrastructure in the United States, including the sectors of financial services, critical manufacturing, and government facilities.
In March 2022, the FBI and US Treasury Department issued a warning about the attacks.
So I only have to worry if I work for an organisation related to US critical infrastructure?
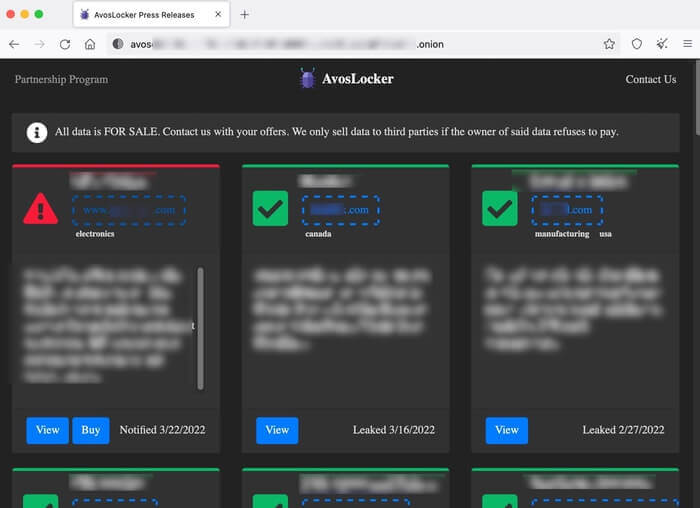
I'm afraid not. The group's leak site on the dark web lists victims around the world, including the United Kingdom, Germany, Canada, China, Spain, Belgium, Turkey, UAE, Syria, Saudi Arabia, and Taiwan. Many of the attacks will have been undertaken by other criminals who are working with the AvosLocker group as affiliates.
Why would anyone want to become an affiliate of a ransomware gang?
If you have no morals about breaking the law then it's a way to make money through ransomware without having to go to all the effort of actually coding the malware, or creating the infrastructure to extort a ransom out of your victims.
The AvosLocker website, located on the dark web, describes it as their "Partnership Program" and says the group can provide "consultancy on operations", "assistance in negotiations", "highly configurable builds" of the malware, and even access to a "diverse network of penetration testers, access brokers and other contacts."
Why would access to a network of other criminals and hackers be useful?
Well, they're the ones who might help you find a way into an organisation to plant the ransomware.
Nasty. This really is organised cybercrime isn't it?
Absolutely.
And if you don't pay up, they'll sell or leak the data they've stolen from your network?
Yes. It's not original, but it's a highly effective way of encouraging many companies to stump up the ransom.
Is there anything else that they do to encourage a ransom to be paid?
Yes, there have been cases where AvosLocker's corporate victims have received phone calls from the criminals themselves, encouraging them to visit the dark web to visit a negotiation portal.
In some instances, there have also been threats to launch distributed denial-of-service (DDoS) attacks against victims, compounding the disruption caused by the initial attack.
I guess that's one way to encourage firms to pay up faster.
It must certainly concentrate the focus of the victims.
What are the authorities doing about AvosLocker?
The FBI has published an advisory to raise awareness of the threat posed by AvosLocker, particularly in relation to critical infrastructure.
In the warning, it shares more information about how the AvosLocker ransomware typically operates, the other tools that are typically deployed in attacks, and specific vulnerabilities in Microsoft Exchange Server that have often been exploited to assist with the intrusion.
So how can my company protect itself from AvosLocker?
The best advice is to follow the same recommendations on protecting your organisation from other ransomware. Those include:
- Making secure offsite backups, and ensuring copies of critical data are not accessible for modification or deletion from the system where the data resides.
- Running up-to-date security solutions and ensuring that your computers are protected with the latest security patches against vulnerabilities.
- Using hard-to-crack unique passwords to protect sensitive data and accounts, as well as enabling multi-factor authentication.
- Encrypting sensitive data wherever possible.
- Reducing the attack surface by disabling functionality which your company does not need.
- Audit user accounts with administrative privileges and configure access controls with least privilege in mind. Do not give all users administrative privileges.
- Educating and informing staff about the risks and methods used by cybercriminals to launch attacks and steal data.
More tips are available in the official FBI advisory.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

