
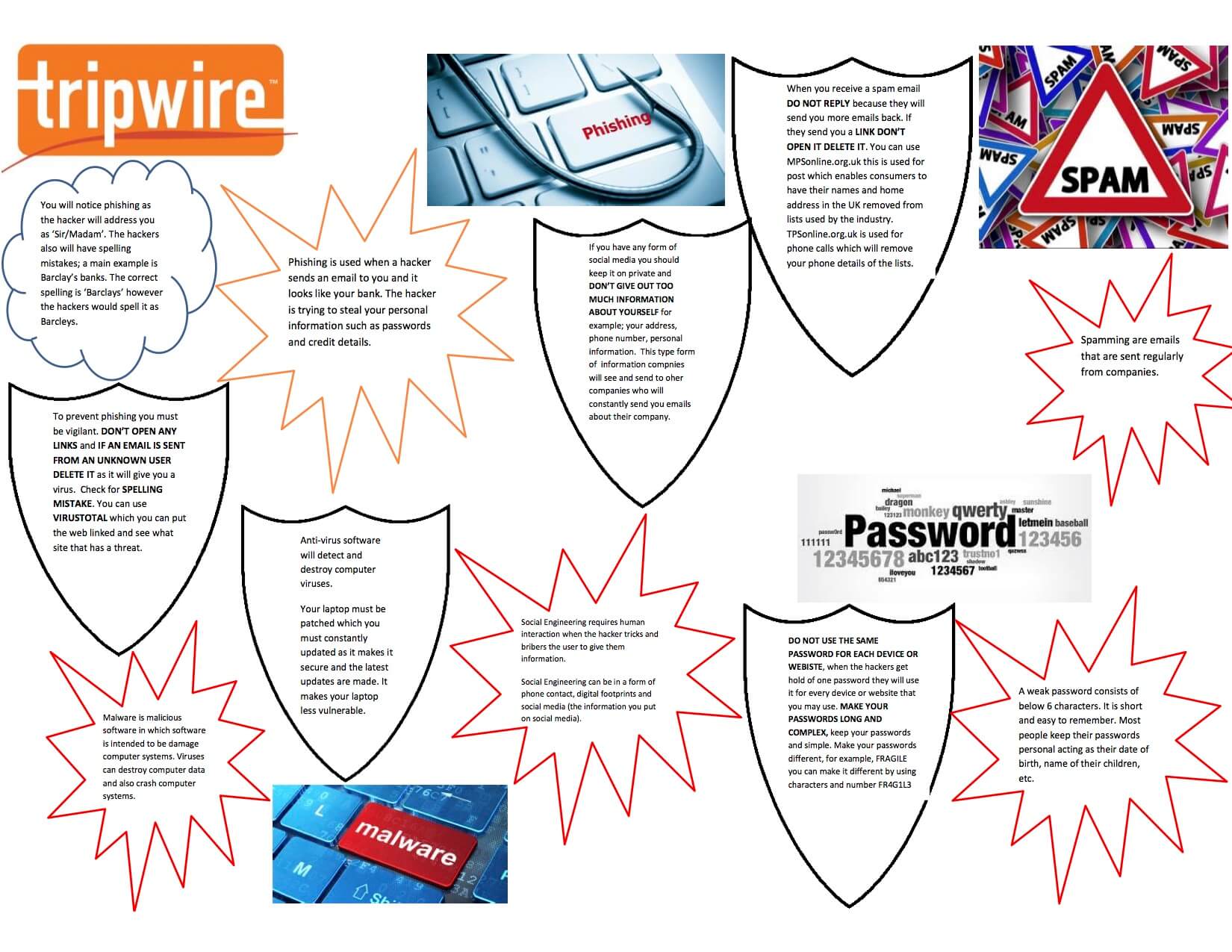
Recently, I had the pleasure of working with Amrit Chana, a 15-year-old girl from Newlands Girl School in Maidenhead, UK, who completed a week's worth of work experience at Tripwire. Amrit helped with the content of this article, providing input on the areas we believe need to be addressed by every user of a computer system. One of the tasks Amrit undertook during her week at Tripwire was to create a general security awareness poster. Amrit and I had a few discussions around what the common threats out there were and how to limit the risks. I was pleasantly surprised at the level of knowledge and awareness Amrit had surrounding good security practices. It demonstrated to me that pupils at schools are being educated on today’s threats and that they do learn about good security practices. Amrit had a lot of good questions, though. She knew she had to keep her system and antivirus signatures up-to-date, but she didn’t know why she had to do it. Once I explained it to her, she said she would pay more attention to updates and implement them more often.
Phishing Attacks
Phishing emails are messages that masquerade as legitimate emails, encouraging the end user to click on a link that takes them to a malicious website or to open a malicious attachment. There are technologies out there that help reduce the amount of phishing emails, but one of the best methods of defense against these types of attacks is user awareness. Prevention Tips:
- Do not click links or open attachments from emails you are not expecting or from unknown senders.
- Be vigilant on clicking links from people you do know. It may not be them sending them!
- Check the URL by hovering the mouse pointer over the link and take a look at the address. Does it look lengthy, and does it have a lot of random characters? If so, it's probably not a good link.
- Legitimate companies, banks, etc. won’t put a web link in their email to you. They will instead advise you to visit their webpage and log in.
- If you are not sure if the URL is safe, do not click it. Carefully copy the URL into the clipboard, visit https://www.virustotal.com, and paste the URL in there. The site will do some analysis of the URL and provide a high-level report on its security.
Malware and Viruses
Every day, there are thousands of new viruses created and released in the wild. Some are brand new; some are variants of existing viruses. Many viruses have a unique signature, a footprint of how it compromises a system. Anti-virus vendors create signature sets for their antivirus products that need to be kept up-to-date. Using an analogy, I explained this to Amrit to help her understand:
Imagine you have a security guard sitting outside your house. This guard has a very large list of people’s names on it. If anyone comes along who is on that list, they are not allowed in the house. If they are not known to the security guard, though, then they gain access to the house and cause havoc. The following day, the security guard receives an updated list, and when the same person comes back, the guard does not allow that person in the house. It’s the same principle with virus signatures; the software blocks and prevents the virus causing havoc if the signature database is up-to-date with the latest threats.
Prevention Tips:
- Ensure you have anti-virus software installed on your computer and that it’s a currently supported version.
- Ensure the software is set to automatically get its signature updates. Check to see when the last update was installed. If it wasn’t in the last week, then check for update issues.
Software and Operating system updates
On a regular basis, operating systems provide updates. Microsoft releases significant updates once a month and releases urgent updates as and when it’s required. Modern-day Windows operating systems are configured to automatically download and install the updates, prompting you to reboot your computer. It’s important to stay on top of these updates and reboots. Applications also have their own update mechanisms that usually check for fixes on a regular basis. It’s equally important to keep these up-to-date to ensure the integrity of your computer system. Amrit stated she knew she had to do the updates but that she didn’t know why. I explained that from time to time, software and operating systems develop bugs or security professionals identify a weakness in the code. As such, the vendors need to fix those flaws before a malicious person exploits the weakness and gains access. Prevention Tips:
- Ensure security updates are enabled within your operating system.
- Make sure you are using a supported version of the operating system. There are a lot of people out there who are running older versions of Windows, such as Windows XP, that are no longer supported. As it’s not supported, security patches are not supplied by the vendors for these operating systems.
- Regularly ensure your operating system is up-to-date by running Windows Update or an equivalent program, and remember to reboot after applying these updates. Otherwise, they won't have any effect.
Social Engineering
Social engineering involves manipulating people into performing actions or divulging confidential information. A common example is a cold caller who phones up victims attempting to gain personal information about the individual, such as bank details or a date of birth. Alternatively, they could try to get them to answer common security questions like their mother’s maiden name. Other social engineering methods are common on social media. For example, posts that ask you to answer 20 questions about yourself and then asks you to share it with your friends can act as treasure troves for attackers. Those questions will relate to habits, favorite things and personal information, data which can be harvested to create a ‘digital footprint’ on the individual. It’s also incredibly easy for people to look over your shoulder in public areas to see what you are typing. How often have you noticed other information on laptops and smartphones when traveling on public transport? I’ve often seen people enter their PIN on phones, see a chat conversation with a loved one, and read confidential emails on a laptop on a train. I’ve challenged a business man once when I sat next to him at the table on the train. He told me to mind my own business, and then he shortly stopped what he was doing afterwards. At least it made him think! Prevention Tips:
- Be vigilant about what you disclose when taking cold calls whether you are at home or at work. Remember these callers are trying to find out information to build a profile about you.
- Social media harvests a lot of personal information from us each day. As mentioned before, review your privacy settings and be conscious about those emails and posts you receive that ask you questions about yourself.
- Be aware of your surroundings, especially on public transport. Did the passenger over your shoulder just see you enter your PIN to your phone? Can they read your emails or social media profile? If you have to work in public areas, consider using a privacy filter on your screen.
Passwords
One of the biggest failings we're sometimes guilty of is using weak passwords and using the same password for more than one account. If one of your accounts, whether it’s for a retailer, social media platform, email account, etc. is compromised and your credentials have been stolen, this information can be easily made available to anyone on the internet. Hackers will then use those credentials to attempt to log in to other common services and steal your information or to compromise you. The simple solution to this is to use unique passwords for all your accounts and use complex passwords that are not easy to guess. The challenge that comes with this is that you can’t remember all these passwords. So, there are ‘password managers’ out there that will help you with this. I have used a few of these password managers in the past, but I have always fallen back to one that I have had the most success with: LastPass. These password managers allow you to generate random secure passwords that are stored online. They are also encrypted by a security passphrase from your master account. The challenge here is that this could be seen as a single point of failure. If you don’t use a secure passphrase for your password manager account and that is compromised, then you stand to lose all your passwords to an attacker. One of the ways to mitigate this single point of failure risk is to enable two-factor authentication. There are a lot of services now that provide two-factor authentication (2FA for short), such as banks, Facebook, Dropbox, Gmail, and even password managers like LastPass. Two-factor authentication is a combination of something you know and something you have. For example, you will enter your password as you would normally. Then, the system will send a SMS to your registered mobile phone with a one-time code or password that expires after a time period of between 30-120 seconds. Other methods are code generators like DUO or RSA SecurID where you have to generate an authentication code. To help with convenience, some services allow you to save ‘trusted devices’ for a period of time during which they won’t prompt you for your a code. Facebook is an example. Prevention Tips:
- Always use a secure password with as many characters as possible (a minimum of 8). Consider using a mix of alphanumeric, upper-case, and lower-case characters. To make it even more secure, use a special character like ‘$&@\*’ etc.
- Never use the same password for more than one account. Always generate a new password.
- Consider using a password manager like LastPass, but do enable two-factor authentication to increase the security around this.
- Never disclose your password to anyone. No-one should need to have your password, not your helpdesk, not your bank, and not your closest friend.
- Shield your device when entering your password or PIN in public areas.
- NEVER write your password down anywhere.
Summary
As we are moving more into the 21st Century, there are more and more services available online. Our lives have moved to a digital age now where everything is available on the internet in some shape or form. We all get very concerned when we hear attacks and breaches in the news and wonder if our data and systems are safe and secure. This article is here to help you stay a little safer on line and in the digital world. Prevention Tips:
- Keep your operating systems and software up to the latest and current versions.
- Install and update your anti-virus software.
- Keep backups of your important data: consider using online cloud providers to store data or external hard disk drives.
- Use secure and complex passwords, and never use the same password for more than one account – consider a password manager instead.
- Never share your password with others.
- Remain vigilant when receiving cold calls and responding to social media posts. Make sure to review your online privacy settings.
This is not a comprehensive list of things to remain safe on line, but it’s a start. *This article was written in conjunction with Amrit Chana, a 15-year-old work experience pupil from Newlands Girl School, Maidenhead, UK.
Tips to Improve Your Security Hygiene by Amrit Chana, 15

