
Business email compromise (BEC) scammers are now focusing on building rapport with victims to increase their chances of success. Just as a little background, a BEC scam begins with an actor launching spear-phishing or whaling attacks against a senior, C-level executive. If the attack proves successful, the actor spends some time researching how the company processes wire transfers and invoices. They then contact someone in the finance department using the compromised executive's email and request that the victim wires money to an account under their control. BEC scammers have thus far met with great success in tricking their victims. Worldwide, over 22,000 companies have pennied up at least 3.1 billion USD to those fraudsters since October 2013. Not included in that pool of organizations is Leoni AG, one of the world’s leading wire and cable manufacturers which lost 100 million USD to a BEC scam in September 2016. But scammers are always looking for ways to improve their chances of success, which is why some actors have injected a personal touch into their schemes. Binny Kuriakose of Symantec explains:
"To better draw out a response from recipients, BEC scammers now use informal and familiar language such as 'hi, are you in office today?' and then gradually build the plot with further emails to establish rapport with the victims and invite their trust. The scammers do not reveal the account information or other details for the transfer until they are reasonably convinced that the victim will comply."
Here's one example of a fraudster checking to see if the victim is at their desk and asking if they need anything to submit the wire transfer request.
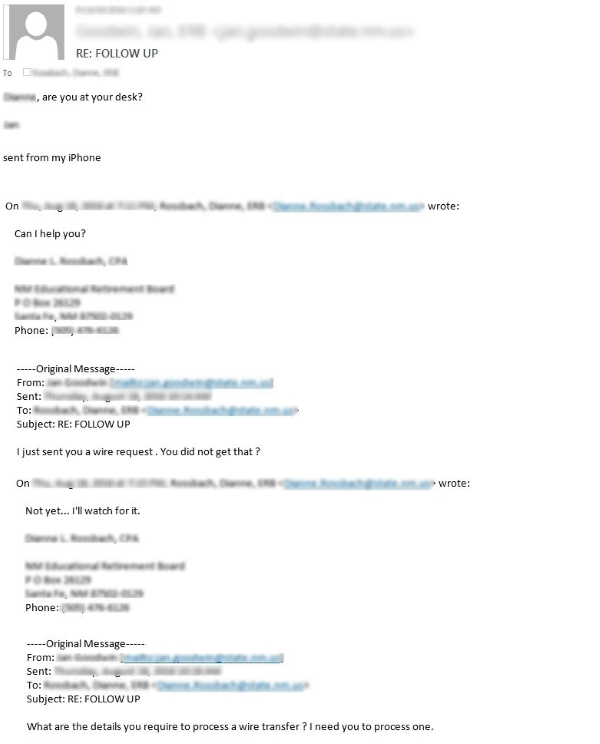
Spammer starts with an availability inquiry before gradually moving on to the wire transfer request. (Source: Symantec) After a little back and forth, the fraudster asks that the victim make the payment as soon as possible and says they will send over an invoice later on. In the event they demand too much money, a scammer may sometimes ask to break up the transfer into manageable amounts that don't require any documentation. That's exactly what happens here. The fraudster originally asks for a transfer of 20,987.56 USD but then revises their demand to 10,000 USD in order to avoid filling out a W-9.
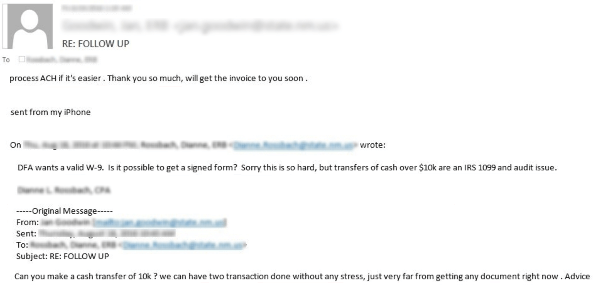
Scammer insists on altering the payment in any way which will not require any document upfront. (Source: Symantec) To protect against these scams and their increasingly complex social engineering techniques, financial and HR employees should report any suspicious emails that ask them to break protocol, including those sent from an executive, to the proper authorities. Senior executives should also undergo some awareness training that teaches them how to spot a phish.

