In today's world, our notion of endpoints has evolved from something with a user and a keyboard to something with exploitable vulnerabilities. This conceptualization therefore covers network connections beyond laptops, personal computers and mobile devices. Indeed, vulnerabilities arising from Internet of Things (IoT) appliances; automobiles, such as security holes that ultimately resulted in a class-action lawsuit against Fiat Chrysler and Harman International; and point-of-sale (PoS) terminals, machines which are now increasingly compromised by threats like BlackPOS and other evasive malware, can now disrupt our networks if these endpoints are not properly secured. Traditional security solutions, such as anti-virus software and personal firewalls, are not adequate to protect all of our endpoints. Neither are many of the tools available today, for many of them generate large amounts of information without context or measurability. This predicament leads into the main topic of a recent webcast hosted by the SANS Institute: “Behind the Curve: Getting Started on Endpoint Security Maturity”. During the presentation, Mark Hardy, a SANS instructor and analyst as well as a recognized international expert in the field of information security, looks to the Gartner model (shown below) as an effective illustration of an endpoint security maturity program.
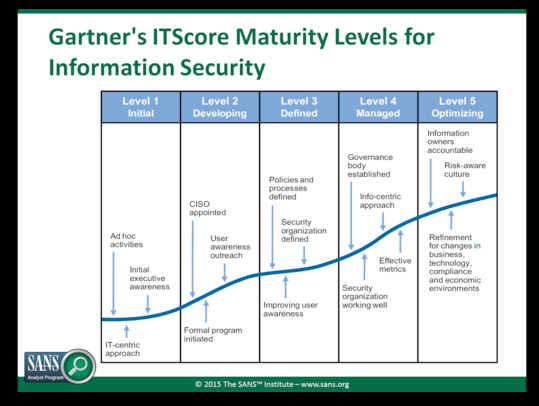
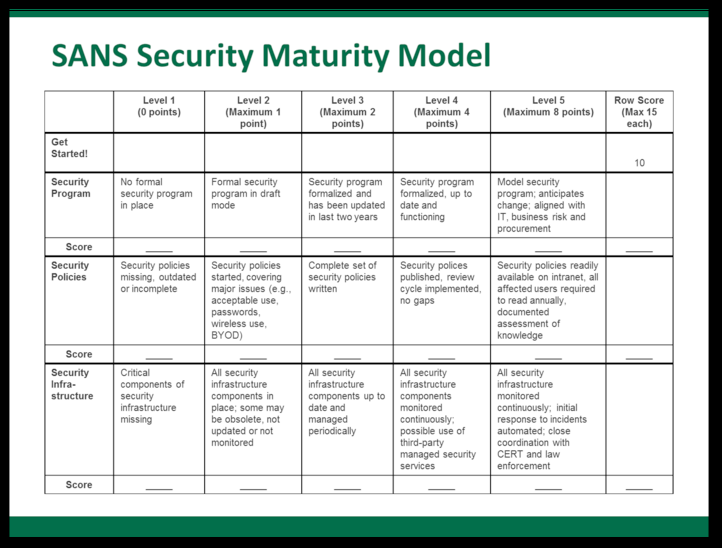
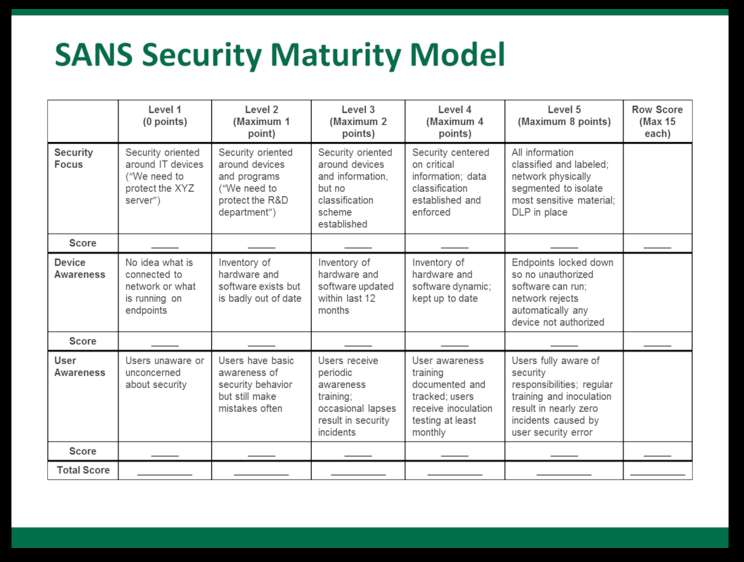
Clearly, the model has certain advantages with regards to measurability and understandability. However, as Hardy points out, Gartner's framework has its drawbacks, which include an organization-wide focus that might prevent security professionals and executives alike from understanding how well they are performing in key security areas. If security personnel are to practice good endpoint security, we must embrace a model that incorporates the most basic tenets of security. Accordingly, by analyzing security's foundations, we realize that endpoints must be protected with special attention paid to the use of certain key elements, including security programs, security policies, security infrastructure, security focus, device awareness, and user awareness. The extent to which an organization embraces each of these features can me measured via a multi-level system that embraces points and grading standards. Subsequently, in contrast to Gartner's framework, a model such as Hardy's (seen below) provides for incremental measurability with respect to the evolution of an organization's endpoint security strategy:
The complexity of today's evolving threat landscape might lead some to believe that endpoint security is nothing more than ticking a box. But as Hardy's and Gartner's models both illustrate, endpoint security maturity is much more than that. It is a culture of doing things right, of protecting information using secure configurations, and of emphasizing user awareness so that all network endpoints, old and new, are accounted for. Following Hardy's presentation, Tripwire CTO Dwayne Melancon leads the talk on how Tripwire factors into endpoint security protection. You can learn more by watching the webcast in full here. Alternatively, you can learn more about Tripwire's endpoint security solutions by clicking here. Title image courtesy of ShutterStock
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

