
Researchers have discovered that certain versions of the popular CCleaner app were modified by hackers to deliver malware to millions of unsuspecting users. Created by Piriform and recently acquired by security firm Avast, the application allows users to perform routine maintenance on their systems, including the cleaning of temporary files and analyzing the system for performance optimization. However, on September 13, Cisco Talos researchers detected a multi-stage malware payload in the 32-bit versions of CCleaner v5.33.6162 and CCleaner Cloud v1.07.3181. “An unauthorized modification of the CCleaner.exe binary resulted in an insertion of a two-stage backdoor capable of running code received from a remote IP address on affected systems,” Paul Young, VP of Products at Piriform, explained in a blog post. Piriform acknowledged that the compromise could cause the transmission of information, such as computer name, IP address, list of installed software, list of active software, list of network adapters, to a third-party computer server in the US. Meanwhile, Avast’s own figures show roughly 2.27 million users ran the infected software – a small but significant percentage of the app’s 2 billion downloads.
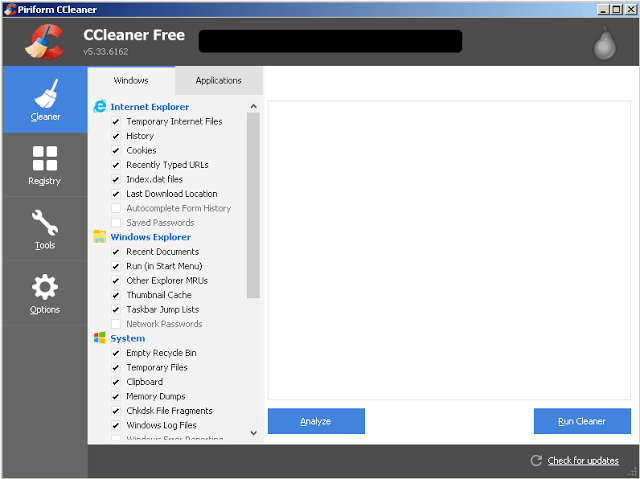
Figure 1: Screenshot of CCleaner v5.33.6162 Piriform said it is working with law enforcement to further investigate the incident:
"At this stage, we don’t want to speculate how the unauthorized code appeared in the CCleaner software, where the attack originated from, how long it was being prepared and who stood behind it. The investigation is still ongoing."
Newer versions of both CCleaner 5.3 and CCleaner Cloud have since been released. Users are strongly encouraged to update to the latest versions of the app. Cisco Talos researchers added: "This is a prime example of the extent that attackers are willing to go through in their attempt to distribute malware to organizations and individuals around the world. By exploiting the trust relationship between software vendors and the users of their software, attackers can benefit from users' inherent trust in the files and web servers used to distribute updates."

