
Cisco has released patches for SSH keys vulnerabilities affecting several of its virtual appliances. The vulnerabilities were discovered during internal security testing and have been found to affect Cisco Web Security Virtual Appliance (WSAv), Cisco Email Security Virtual Appliance (ESAv), and Cisco Security Management Virtual Appliance (SMAv).
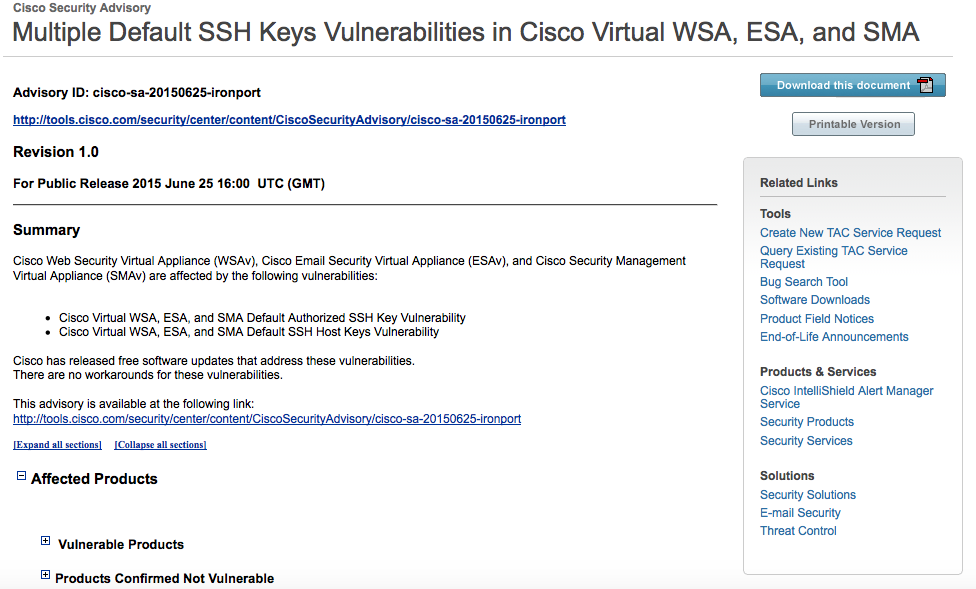
The first flaw, a Cisco Virtual WSA, ESA, and SMA Default Authorized SSH Key Vulnerability, is located in all three affected virtual appliances' remote support functionality, according to a security advisory released by Cisco. A remote hacker can use this vulnerability to connect to an affected system with the privileges of a root user. The second bug is a SSH Host Keys Vulnerability that also affects Cisco Virtual WSA, ESA, and SMA.
"At attacker with possession of compromised keys, who is able to intercept traffic between the WSAv or ESAv and a host it is communicating with, would be able to decrypt the communication with a man-in-the-middle attack," warns the advisory. "Exploiting this vulnerability on Cisco SMAv is possible in all cases in which SMAv is used to manage any content security appliance. Successfully exploiting this vulnerability on Cisco SMAv allows an attacker to decrypt communication toward SMAv, impersonate SMAv, and send altered data to a configured content appliance. An attacker can exploit this vulnerability on a communication link toward any content security appliance that was ever managed by any SMAv."
Cisco states that there are no workarounds for this issue. However, the technology company has released a patch that deletes the preinstalled SSH keys and provides instructions for how customers can fix the problem. The patch, known as “cisco-sa-20150625-ironport SSH Keys Vulnerability Fix”, must be manually installed from the command line interface. It is not required for physical hardware appliances or for virtual appliance downloads or upgrades after Thursday. In the meantime, Cisco has pulled WSAv, ESAv, and SMAv images while it patches them, but it says that new versions will be posted “in the following days." This news follows a patch issued by the company earlier this spring for an eavesdropping vulnerability on two Cisco IP phones.

