
A cryptocurrency miner has earned its place on a list of the top 10 most wanted malware for the month of October 2017. The browser-mining service in question goes by the name "CoinHive." It's a piece of JavaScript that site owners can embed into their websites. Whenever a user visits their domain thereafter, CoinHive will activate and begin mining for Monero, a cryptocurrency which already has a history with MineCrunch and other cryptominers like it. Site owners commonly keep cryptocurrency miners a secret from visitors. This is a problem, as mining for cryptocurrency is resource-intensive. In October 2017, Check Point found that this process can consume as much as 65 percent of an unsuspecting user's CPU, thereby degrading their computer's performance. For that reason, the software provider decided to award CoinHive 6th place on its list of the 10 most wanted malware for the month. Check Point feels it has just reason to do so:
"Crypto mining is emerging as a silent, yet significant, actor in the threat landscape, allowing threat actors to extract substantial profits while victims’ endpoints and networks suffer from latency and decreased performance. The emergence of Seamless and CoinHive once again highlights the breadth and depth of the challenges organizations face in securing their networks against cyber-criminals."
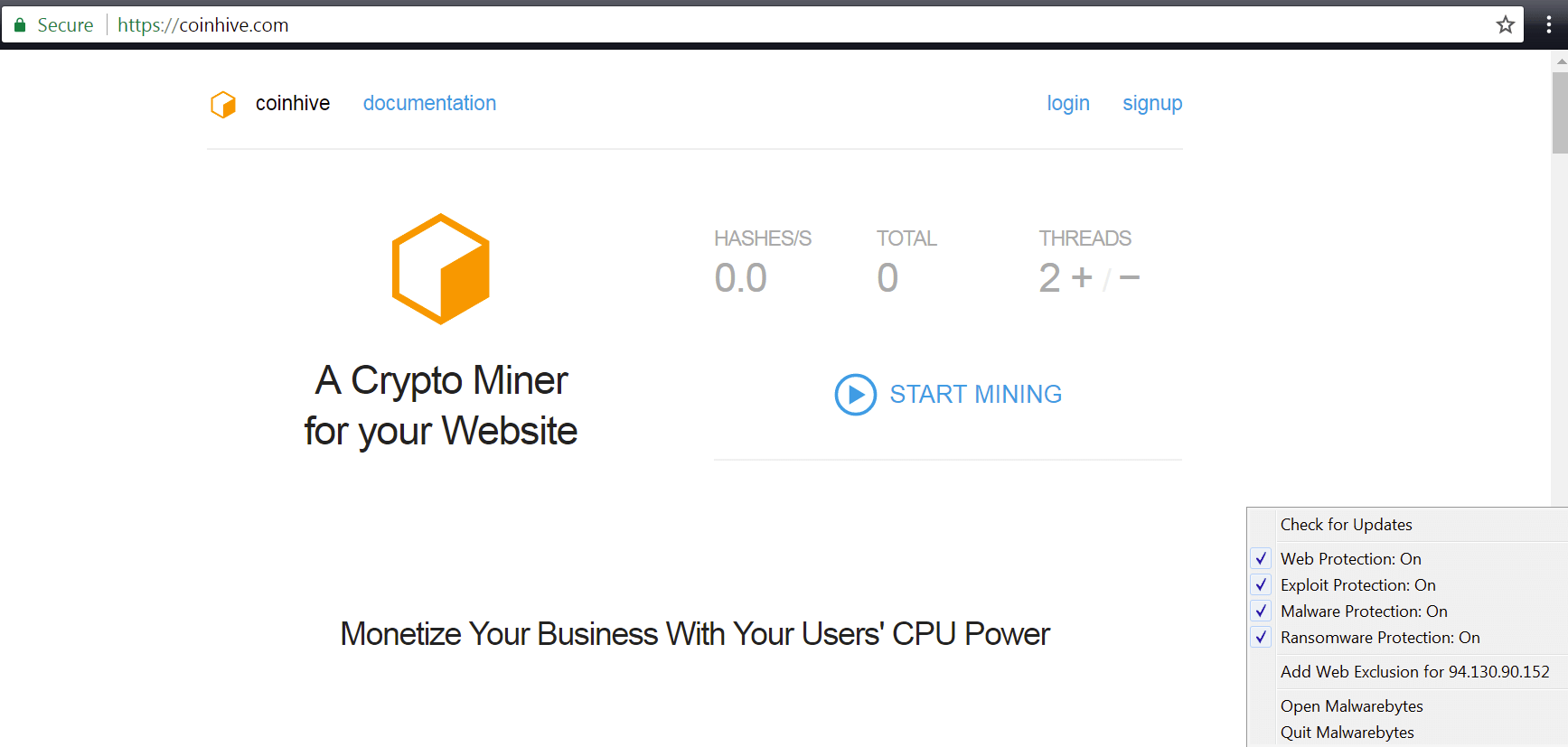
Coinhive. (Source: Malwarebytes) Meanwhile, a malvertising campaign known as RoughTed and Locky ransomware earned first and second place on Check Point's list, respectively. They were joined by Seamless Traffic Distribution System (TDS) at third place. This malware redirects users to a malicious web page that exposes them to an exploit kit. If that program locates a software vulnerability it can exploit, it downloads additional malware onto the victim's machine. Researchers at Check Point are urging organizations to be on the lookout for threats like TDS:
"There is no doubt that this new form of malware is here to stay, highlights the need for advanced threat prevention technologies. This should involve a multi-layered cybersecurity strategy that protects against both established malware families and brand new, zero-day threats."
To learn how Tripwire's vulnerability management and other threat prevention solutions can help protect your organization, please click here. In the meantime, users can protect themselves against JavaScript-based cryptocurrency miners by using a browser add-on like NoScript to block JavaScript on all unfamiliar sites they visit.

