Although DNS rebinding attacks have been known for over a decade now, they are only recently receiving attention as a practical attack surface. In the last year, quite a few popular products have been shown to lack DNS rebinding protections, and as a result, someone could operate them remotely using a malicious web site. Manufacturers have made a habit of giving consumers connected devices that are controlled by unauthenticated HTTP requests via the local network. This mentality, that the private LAN is trusted, is undermined by the impact of DNS rebinding. It also turns out that vulnerabilities within HTTP-based applications can be unexpectedly exploited across network boundaries. For example, the recent ES File Explorer ‘Open Port Vuln’ was generally reported as only being exploitable by an attacker on the same WiFi network as the victim. This was in fact an understatement of the risk since the vulnerable HTTP server cannot differentiate between legit and relayed requests. Last year, I created an integrated DNS/HTTP server designed to facilitate DNS rebinding attacks which can be created on the fly with a simple UI. This software, called Dolos, has been used in Black Hat USA and SecTor training classes. Now, in coordination with my upcoming talk at Infosec EU, I have released the source code on GitHub! Dolos simplifies the process of creating an exploit by empowering users with two modes of network discovery as well as automated target discovery and payload delivery. In most cases, the Dolos operator will only need to supply a port number for the targeted HTTP server, a path which exists on that server and finally a JavaScript snippet intended to execute after the rebinding is complete. Dolos then generates HTML payloads which are saved as attack profiles. Once a victim browser on the targeted network opens the link, Dolos will attempt to use WebRTC to reveal a local IP address and then scan adjacent addresses for the expected file. If WebRTC is unavailable, Dolos will exploit a novel timing oracle within the HTML5 Fetch API to leak information about accessible networks by timing error messages. Any discovered networks will be scanned for the expected port/path. For each discovered IP:port with the expected page, an IFRAME is added to the browser using a special URL including the IP:port for rebinding as well as the payload to send from a newly generated rebinding domain. Alternatively, users can use Dolos without the Wizard UI to craft content for CSRF or rebinding attacks with a high degree of flexibility. Deploying your own Dolos infrastructure requires a Linux server that can receive connections on a public IP address. A publicly registered domain with an NS record pointing to the Dolos server is needed to perform DNS rebinding attacks. Remember to also open UDP/53 as well as whatever ports you wish to use for HTTP. (DNS rebinding attacks require running a server on the same port as the targeted server.) To get started with Dolos, simply clone the source files out of GitHub, update the configuration and start the service. Refer to the README.md for more details on deployment. Once Dolos is running, you can connect to it by browsing to the web UI using a URL similar to the following: http://loader.[dolos-domain]:[dolos-port]/gui This will bring you to a page similar to the following:
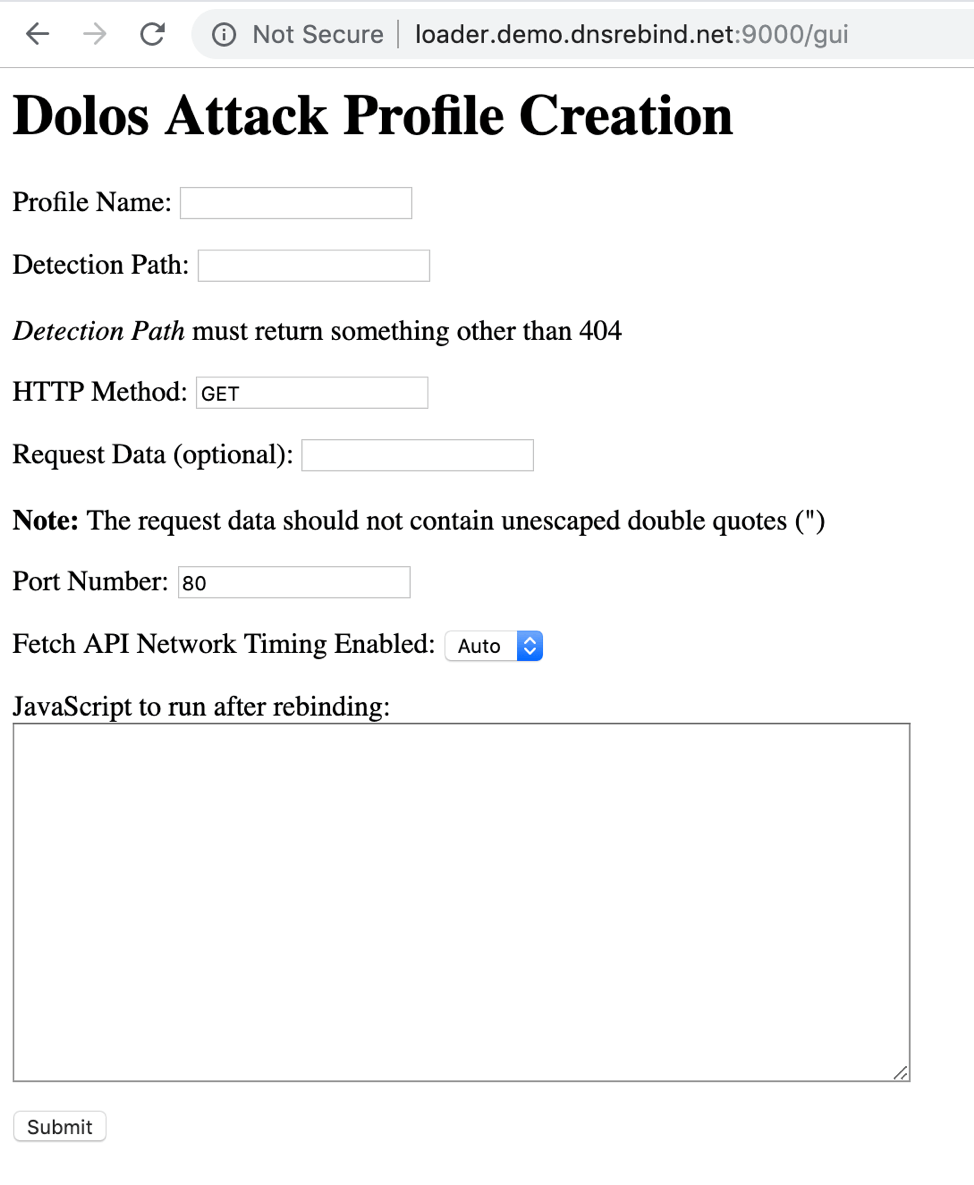
The fields on this form are spelled out in more detail in the readme, but the general idea is that the user describes the targeted application by supplying an HTTP port number along with a URL on the target which returns something other than an HTTP 404 status code. Finally, the user inputs some JavaScript they wish to run after the rebinding, and Dolos generates an attack profile which can be referenced with a short URL. Once a victim browser loads the attack profile link, JavaScript from Dolos will attempt to identify which private networks are accessible from the victim’s browser and send HTTP requests to the specified port/path from the attack profile. Each time a non-404 response is received, an IFRAME is added to the page referencing the Dolos /rebind URL with arguments to specify a IP/port and what content to serve. The /rebind request redirects to a newly created domain on the expected port. The content served from this page will make periodic queries to the Detection Path specified in the attack profile. Prior to the rebinding, these requests are received by Dolos, which sends a 404 error. After a successful rebinding, the request will go to the targeted system, which sends a different response. At this point, the supplied JavaScript is executed. When developing payloads, I’ve also found a very effective way to test iterations of the JavaScript payload without having to repeatedly wait for DNS rebinds. Instead, my trick is to open the targeted web app in a Chrome incognito tab and then paste my payload into the JavaScript console. As long as the target is vulnerable to DNS rebinding and there are no cached authentication cookies or credentials being used, JavaScript typically executes the same in this environment as it will after a successful rebinding. This allows for quickly testing changes to the payload before deploying a full exploit. Using Dolos has enabled me to rapidly develop several proof-of-concept exploits including hijacking routers, television sets, smart outlets, smart speakers and even the Android ES File Explorer app. Releasing Dolos is ultimately intended to draw more attention to the problem of DNS rebinding and encourage product vendors to implement fixes. Dolos is also designed with red teams and penetration testers in mind to encourage network operators to enable DNS rebinding mitigations. To do this, simply fork the project and reskin rebind_ip_scanner.html as needed to fit the scenario. Pull requests and issue reports are also encouraged.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

