
An attack campaign known as Dragonfly 2.0 is currently targeting Western energy companies with a variety of infection vectors. The series of attacks constitutes the latest push from Dragonfly, a threat actor which has been around since at least 2011 but then reemerged in 2014. Available evidence suggests the Dragonfly 2.0 attack campaign has been underway since December 2015. Judging by the operation's tactics and techniques, the attackers appear interested not only in learning how energy facilities operate but also in potentially gaining access to operational systems at targeted organizations. Entities in the United States, Turkey, and Switzerland have recently reported indications of Dragonfly 2.0 activity, including infection vectors the group is known to use in an attempt to gain access to a targeted company's network. In some cases, Dragonfly leverages emails laden with malware to leak victims' network credentials and exfiltrate them to an external server. The threat actor has a particular proclivity for Phishery, a template injection toolkit which made its way onto GitHub in late 2016. That's not all for which Dragonfly is known. Symantec's Security Response identifies another infection vector preferred by the threat actor:
"As well as sending malicious emails, the attackers also used watering hole attacks to harvest network credentials, by compromising websites that were likely to be visited by those involved in the energy sector.
"The stolen credentials were then used in follow-up attacks against the target organizations. In one instance, after a victim visited one of the compromised servers, Backdoor.Goodor was installed on their machine via PowerShell 11 days later. Backdoor.Goodor provides the attackers with remote access to the victim’s machine."
Finally, Dragonfly is known for sending backdoors like Trojan.Heriplor and Trojan.Karagany.B as fake Flash updates or legitimate software that's been compromised to victims' inboxes.
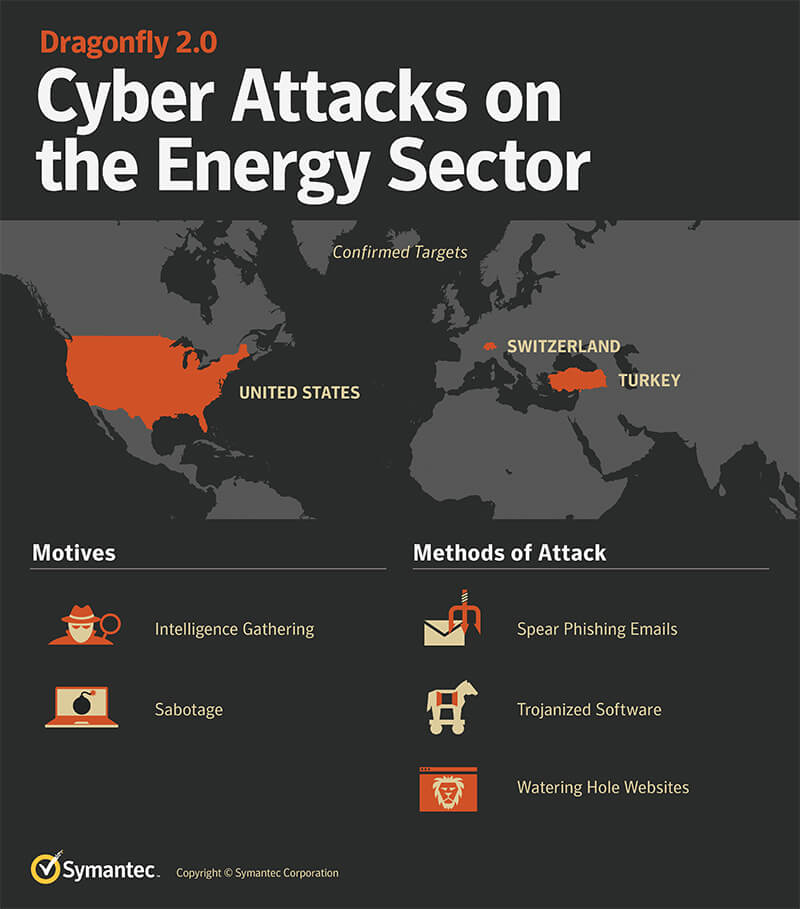
An outline of the Dragonfly group's activities in its most recent campaign. (Source: Security Response) The appearance of Trojan.Heriplor and Trojan.Karagany.B makes Security Response's team suspect these attacks indeed share a connection with Dragonfly. That's because both backdoors aren't widely available. Trojan.Heriplor is thought to be Dragonfly's custom malware, whereas Trojan.Karagany.B has appeared in previous attacks against energy organizations. As of this writing, attribution for the individuals behind Dragonfly is lacking. But it's somewhat clearer as to what they might be after. Here's Security Response once more:
"The original Dragonfly campaigns now appear to have been a more exploratory phase where the attackers were simply trying to gain access to the networks of targeted organizations. The Dragonfly 2.0 campaigns show how the attackers may be entering into a new phase, with recent campaigns potentially providing them with access to operational systems, access that could be used for more disruptive purposes in future."The most concerning evidence of this is in their use of screen captures. In one particular instance the attackers used a clear format for naming the screen capture files, [machine description and location].[organization name]. The string 'cntrl' (control) is used in many of the machine descriptions, possibly indicating that these machines have access to operational systems."
Given the persistence of the Dragonfly 2.0 attack campaign, it's important that energy organizations take steps to protect themselves against digital threats. They should educate their employees about phishing attacks and consider segmenting their networks, for example. They should also look to leverage security controls to better defend their industrial control systems (ICS). Learn how Tripwire's products can ramp up your organization's ICS defense strategy here.
Achieving Resilience with NERC CIP
Explore the critical role of cybersecurity in protecting national Bulk Electric Systems. Tripwire's NERC CIP Solution Suite offers advanced tools for continuous monitoring and automation solutions, ensuring compliance with evolving standards and enhancing overall security resilience.

