
A new report from ENISA, the European Union Agency for Cybersecurity, looking at cyberattacks targeting the European transport network over a period of almost two years, has identified that ransomware has become the prominent threat.
ENISA's report, its first ever analysis of the myriad of cybersecurity threats facing the transport sector in the EU, mapped and studied cyber incidents targeting aviation, maritime, railway, and road transport between January 2021 and October 2022.
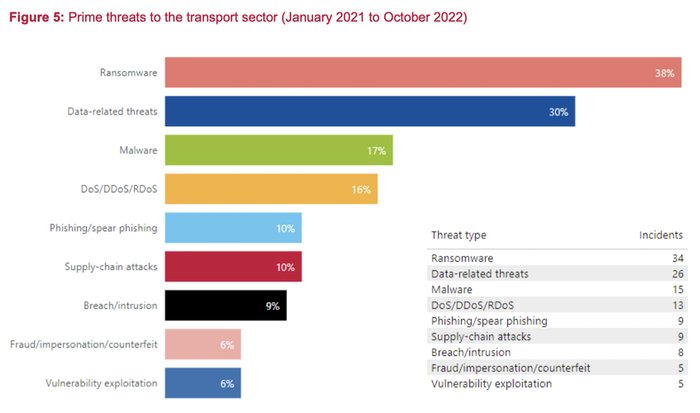
During this period, the three major threats identified were:
- ransomware attacks (38%)
- data-related threats (30%)
- malware (17%)
- denial-of-service attacks (16%)
- phishing/spear-phishing (10%)
- supply-chain attacks (10%)
What is particularly interesting is to note how threats appear to have changed between 2021 and 2022, with a dramatic rise in the proportion of ransomware attacks targeting the transport sector rising from 13% to 25%, and denial-of-service attacks exploding from 2% in 2021 to 13% in 2022.
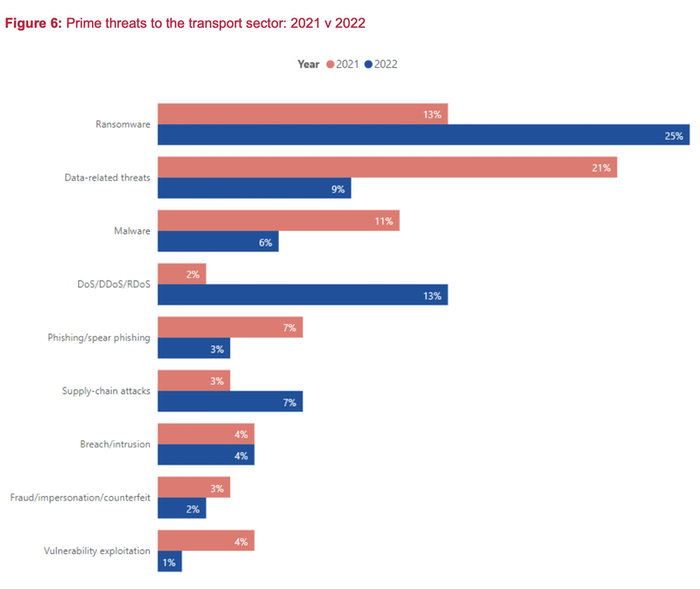
The rise in denial-of-service attacks - with European airports and railway companies being hit at an increasing rate - is said by ENISA to be most likely linked to hacktivists, much of it seemingly in response to Russia's invasion of Ukraine. Such attacks often lead to operational disruption, preventing members of the public from travelling or disrupting the movement of goods.
Meanwhile, data-related threats (such as breaches and data leaks, which often involve login credentials, employee and customer data, as well as intellectual property) declined as a proportion when compared to ransomware, falling from 21% in 2021 to 9% in 2022.
It should be noted that ENISA's report only examines those cybersecurity incidents which have been reported to it. The writers of the report admits that "we still have limited knowledge and information regarding such incidents. The analysis in this report indicates that publicly disclosed incidents are just the tip of the iceberg."
2024 will see a new European directive (NIS2) that will call upon member states to boost their cybersecurity across all industry sectors, improve their reporting of attacks, and compel countries to assemble effective response teams as part of a wider effort to improve defences against state and non-state actors.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

