
The 2016 Verizon Data Breach Investigations Report (DBIR) is out, and I’m excited to announce that this year’s findings leveraged vulnerability data from Tripwire and other vendors, including our partner Kenna Security. The 2016 Verizon DBIR recommends establishing “a process for vulnerability remediation that targets vulnerabilities which attackers are exploiting in the wild” (DBIR, pg. 16). Meaning, you should try to find the things hackers are actually breaking into and try to fix those things first. So, what kind of vulnerabilities are being attacked in the wild? According to the DBIR, there are two primary targets:
- Vulnerabilities that are old
- Vulnerabilities that are easy to exploit
Those seem to be two high-priority targets for attackers. The DBIR explains further…
“…the tally of really old CVEs which still get exploited in 201 suggests that the oldies are still goodies. Secondly, attackers automate certain weaponized vulnerabilities and spray and pray them across the internet, sometimes yielding incredible success.” (DBIR, pg. 15).
Just like all of us, hackers have limited time and resources, so they attempt to go after the low hanging fruit—the things that will get them the biggest bang for their buck. Exploit kits – malicious toolkits used to exploit vulnerabilities in software applications with the primary purpose of spreading malware – make the spray-and-pray approach an easy 24/7 operation for hackers at little cost. Along the same lines, vulnerabilities that have existed for a while have been around long enough for hackers to understand how to best use them to attack their target and create automated exploit kits. Hence, it can be helpful to consider the age of a vulnerability, as well as an exploit’s availability, to determine which vulnerabilities pose the highest risk to your organization. So, how do you find the old vulnerabilities that are easy to exploit? The DBIR then recommends:
“Establish a process for vulnerability remediation that targets vulnerabilities which attackers are exploiting in the wild, followed by vulnerabilities with known exploits or proof-of-concept code.” (DBIR, pg. 16)
As an example, risk prioritization is one way to do just that.
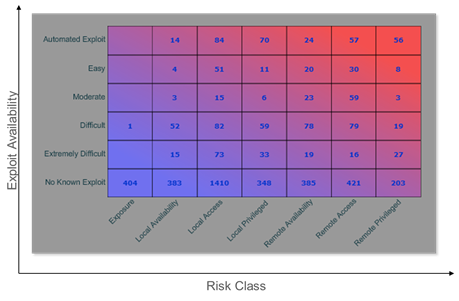
In this sample report, the numbers in each box represent the number of vulnerabilities in that category. For example, in the top right box, 56 vulnerabilities were found to have automated exploits and provide remote privileged access. The Tripwire Risk Score used by Tripwire IP360 is designed around a few risk-based criteria, including the age of the vulnerability, as well as skill level required by an attacker (is there an automated exploit available?), and what level of access would be gained by a successful attacker (“risk class”). The IP360 Scoring System is designed around a few basic concepts: 1) Remote vulnerabilities are generally more critical than local vulnerabilities. 2) Older vulnerabilities are often more critical than newer vulnerabilities. 3) The availability of an exploit (and the ease of using said exploit) directly affect the criticality of a vulnerability. Every organization is unique, and since the Tripwire Risk Score default configuration is not always a one-size-fits-all, scoring options exist that allow further manipulation of scoring to better meet a specific requirements. In some cases, that means the Tripwire Risk Score can provide a better prioritization metric than standards like CVSS. To learn more about how risk prioritization can help you establish a process for vulnerability remediation, like the one recommended in the Verizon DBIR, check out the Tripwire Risk Score Whitepaper. Title image courtesy of ShutterStock

