
Think of all the recent DDoS attacks. They all seem to share the common trait of bad guys disrupting the normal flow of data against a legitimate business. Sometimes, these attacks are used for revenge, and other times, they are used for ransom. Sometimes, however, the bad guys become the targets. This is the story of an odd caper that played out on the dark web in September. In this two-part series, I explore a recent attack that was carried out on the Tor network. In part one, I describe the event and what little information may be gathered from publicly available sources. In part two, I discuss what I deduced from the information, including how the attacks may have been carried out along with possible culprits.
Who doesn’t love a good mystery?
On September 14, 11 parallel DDoS attacks targeted the largest darknet drug markets, effectively taking an entire industry offline. This event poses a number of interesting questions about both the underlying technology and the motivation and identity of the attacker. As of this writing, the story is still unfolding. As a cybersecurity researcher, I found some fascinating and curious characteristics in this event that are worthy of exploration. First, let’s dispense with the ethical problem of such an exploration. All law-abiding citizens benefit from the eradication of illegal drug markets. Our job as cyber sleuths is to unravel some of the possible vulnerabilities that allow any enterprise to be taken offline. Such vulnerabilities, regardless of the target, threatens the entire e-commerce industry. In order to not promote any of these illegal enterprises (some of which are back online), I will not mention any of the illegal sites by name. The first hint of trouble came from some online posts by a site administrator. One message posted to the /r/DarknetMarkets subreddit forum signed with PGP keys associated with one of the drug markets stated that they had seen a massive influx of users, as they were originally not being attacked along with the other markets. However, presumably the same attacker then took down this market. An influx of new users, and then the site is taken down? The plot thickens! The site admin said they were trying to restore service to their users and would be working hard to get back online. They said they were trying to get more servers running and better load balance their site. Later that day after briefly coming online, the admins published another post saying that they were back online and describing the attack:
“After investigation, we do not believe there is a ToR exploit of any sort, however there is a potential flaw by design, which is helping to keep servers down.”
Is this a Tor exploit or something else? From the looks of the bandwidth activity from the time of the attack, there is nothing notable in the traffic. A DDoS traffic flood would show a spike, yet no such spike exists.
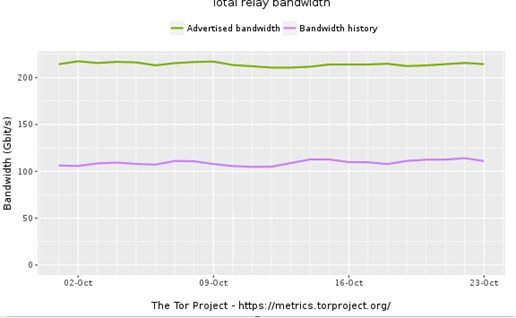
A network layer attack capable of taking down 11 sites that have a significant financial interest in staying online would likely use tens or hundreds of GB of bandwidth per second above the normal traffic flow. How is this possible, who would do this, and why? In part two this series, I explore what I have deduced from some of these clues, and identify some possible culprits. You can read part two here.

About the Author: Nick McKenna is a student researcher who has had an interest in cyber security for the past five years. Nick likes seeing how things work and trying to break them. If you have any questions, you can contact Nick here. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

