
In less than a decade, cryptocurrency became almost mainstream. Many people are familiar with Bitcoin, which was the first decentralized digital currency. In fact, there are more than 10 different cryptocurrencies with a market cap exceeding 1 billion US dollars. Some are very similar, but others significantly differ in the mathematical and computational properties of their implementation. As a direct result of that, there are major differences in the financial properties between cryptocurrencies. For example, some provide little to no anonymity, while others’ cryptographic properties assure you that no one will ever know the identity of one or even both sides of a transaction. Technology that provides you with anonymity can be marvelous. TOR, for example, helps enable oppressed citizens to speak against their regimes without being prosecuted. However, the anonymity provided by TOR is often being used by cybercriminals, drug dealers and pedophiles. Cryptocurrency is a similarly wonderful idea, but unfortunately, the anonymity some digital coins provide is abused just like TOR. Monero is the best example of a legitimate cryptocurrency widely that's been adopted by cybercriminals. Unlike Bitcoin, it sports built-in completely anonymous transactions, and it can be efficiently mined on consumer-grade CPUs. The first property saves criminals the need of complex inefficient money mules, as they can simply pay directly with their loot without being afraid that the payment can be traced back to them. The second one makes almost any PC worldwide a potential moneymaker, mining Monero without the knowledge or consent of users Only last year, we experienced many interesting incidents involving Monero mining including:
- Adylkuzz: a cryptominer spreading over SMB that started using ETERNALBLUE and DOUBLEPULSAR even before WannaCry and NotPetya
- Coinhive: a service providing a JS script that once embedded in a site will mine Monero from users browsing it
- Unknown attackers leveraging an exploit to install an open-source miner on vulnerable servers, gaining over 63,000 dollars
On the good side, Monero (and other) cryptominers are quite easy to detect. Most are modified versions of open-source projects like XMRig and NiceHash. Moreover, unlike other types of malware, the more optimized a cryptominer is, the more revenue it will make. Interestingly, this forces bad guys not to use obfuscators, which make their malware less detectable but will also have a negative impact on its efficiency. Currently, it is quite easy to detect a miner either by networking activity associated with pools or by the fact that many times the miner consumes over 90 percent of the CPU and can be found using a simple task manager. It seems that the main challenge nowadays is not to detect the cryptominer; it is all about deciding if it was started by a user is knowingly.
What’s Next?
Security products are catching up quickly by blocking domains that host mining scripts. One of these hosts, Coinhive, reacted to it by adding a consent form to their miner. At the moment, it is unclear whether this will be sufficient to please the vendors blacklisting it. My prediction is that we will see adoption of Exploit-Kit like tactics to evade blacklisting, including serving the mining script from countless disposable websites and exploits to detect sniffers and analysis environment.
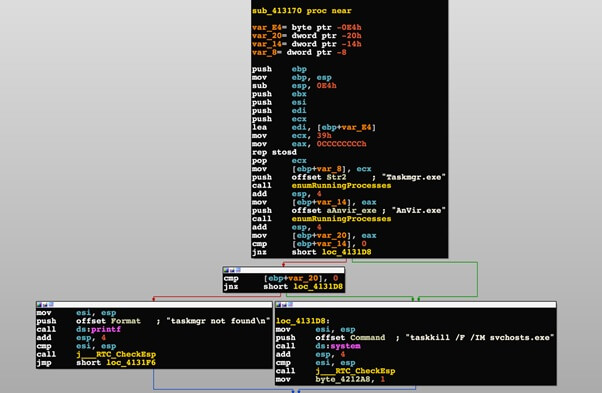
Miner testing if monitoring programs are opened and terminates itself if so All the above applies to web-based miners, but what about binaries running on endpoints? My team and I recently uncovered an evasive cryptominer dubbed WaterMiner. To evade detection by average Joe’s opening their Windows Task Manager, WaterMiner will simply shut down when it finds such program is running. This evasion technique will possibly be increasingly adopted as well, as it is easy to integrate and effective while not having an impact on performance as obfuscation.

About the Author: Gal Bitensky is a 29-year-old geek from Tel-Aviv and breaker of stuff. Currently working as a senior malware psychologist in the Israeli start-up Minerva Labs, he is experienced in various fields, ranging from web application security and Windows internals to SCADA. Fluent in exotic languages like PHP, LISP and Arabic, Gal is an advocate of simple and effective solutions. You can follow him on Twitter and LinkedIn. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

