
An attack which targeted users of the Telegram app on Wednesday might be linked to protests in Hong Kong that turned violent. That's one of the theories in circulation, after a distributed denial-of-service (DDoS) attack disrupted legitimate access to the Telegram secure messaging app by swamping it with "garbage requests." Pitched battles broke out in Hong Kong on Wednesday between police and protestors over proposals to allow the extradition of suspects to mainland China. Smartphone messaging apps like Telegram and the less well-known FireChat - which creates a mesh network using Bluetooth and peer-to-peer Wi-Fi, allowing users to communicate even when they don't have a cellular signal or internet access - are currently amongst the most popular downloads in Hong Kong's iOS app store and were being widely used by protesters. Many of those involved in the demonstrations, fearful of potential repercussions if facial recognition technology was deployed by law enforcement, covered their faces with masks and queued to buy public transport tickets rather than using Oyster cards that might be tracked. https://twitter.com/MsKateLyons/status/1138689891368226817 Clearly any disruption of encrypted messaging apps being used by protesters would be massively inconvenient. In a series of tweets, Telegram described that it was under attack and offered one of the most humorous descriptions of a denial-of-service attack that I've ever heard:
We’re currently experiencing a powerful DDoS attack, Telegram users in the Americas and some users from other countries may experience connection issues. A DDoS is a “Distributed Denial of Service attack”: your servers get GADZILLIONS of garbage requests which stop them from processing legitimate requests. Imagine that an army of lemmings just jumped the queue at McDonald’s in front of you – and each is ordering a whopper. The server is busy telling the whopper lemmings they came to the wrong place – but there are so many of them that the server can’t even see you to try and take your order. To generate these garbage requests, bad guys use “botnets” made up of computers of unsuspecting users which were infected with malware at some point in the past. This makes a DDoS similar to the zombie apocalypse: one of the whopper lemmings just might be your grandpa. There’s a bright side: All of these lemmings are there just to overload the servers with extra work – they can’t take away your BigMac and coke. Your data is safe.
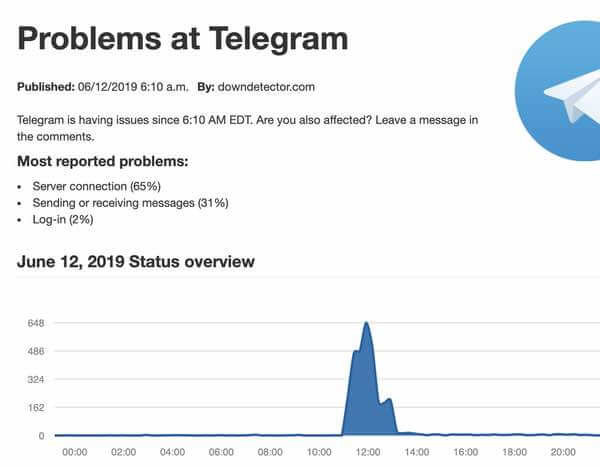
Users of Telegram turned to social media to complain that Telegram was hard to access, with complaints originating from countries around the world including the United Kingdom, the east coast of the USA, Germany, Russia, China, and Hong Kong. Fortunately, within a couple of hours, things began to stabilise.
As Bloomberg reports, Telegram's founder Pavel Durov tweeted that the attack mostly came from computers with IP addresses in China, and noted that they coincided with the Hong Kong protests. https://twitter.com/durov/status/1138942773430804480 Of course, it's important to stress that there's a big difference between identifying IP addresses used in a DDoS attack, and attributing responsibility for an attack to a particular country. But the sheer scale of the attack has made observers suspect that the attack may have been state-sponsored. We will have to wait and see if anyone claims responsibility for the attack or, as seems likely, those responsible choose to keep their heads down and plot for how their next attempt to disrupt encrypted communications might be more successful.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

