
On August 15th the NSA and FBI published a joint security alert containing details about a previously undisclosed Russian malware. The agencies say that the Linux strain malware has been developed and deployed in real-world attacks by Russian military hackers. The FBI says, “The Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS) military unit 26165, whose activity is sometimes identified by the private sector as Fancy Bear, Strontium, or APT 28, is deploying malware called Drovorub, designed for Linux systems as part of its cyber espionage operations.”
What is Drovorub?
The name Drovorub comes from a variety of artifacts discovered in Drovorub files, Drovo translates to “firewood” or “wood”, while Rub translates to “to fell, or “to chop.” Together, they translate to “woodcutter” or “to split wood.” Drovorub is like a Swiss-army knife for hacking Linux. The Linux malware toolset consists of an implant coupled with a kernel module root kit, a file transfer and port forwarding tool, and logic for connecting back to a Command and Control (C2) server. The below figure shows the Drovorub components and their functions.
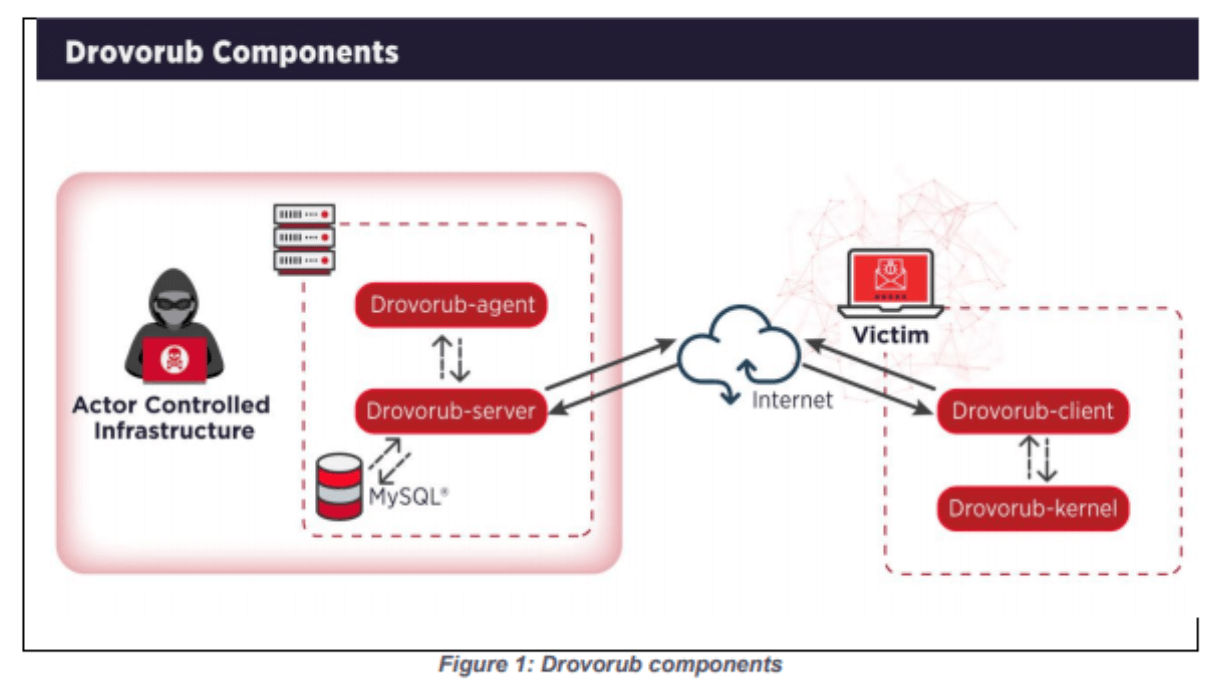
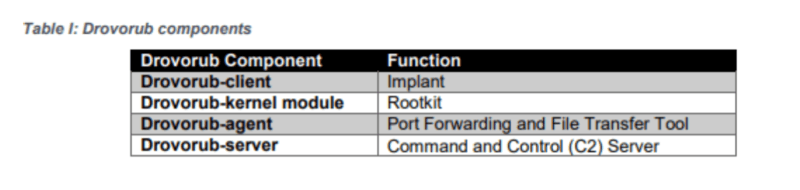
Drovorub malware is made up of four executable components: Drovorub-client, Drovorub-agent, Drovorub-kernel module and Drovorub-server. The components communicate via JSON over WebSockets. Below is a brief overview of each component.
Drovorub-Server
Installed on actor-controlled infrastructure, enables C2 for the Drovorub-client and Drovorub-agent. mySQL is used by the Drovorub-server to manage the connecting Drovorub-client(s) and Drovorub-agent(s). The database stores data that is used by the Drovorub-agent and client for registration, authentication and tasking.
Drovorub-client
The Drovorub-client is installed on target endpoints by the actor. The client receives commands from the remote Drovorub-server and offers file transfer to/from the victim, port forwarding, and a remote shell capability. The Drovorub-client is packaged within a Drovorub-kernel module which provides rootkit-based stealth functionality to hide the client and kernel module.
Drovorub-kernel module
The kernel module implements the stealth, hiding itself and various artifacts from user-space, including specified files and directories, network ports and sessions, the Drovorub-client process, and Drovorub-client child processes.
Drovorub-agent
The Drovorub-agent executable receives commands from its configured Drovorub-server. The agent is likely to be installed on internet-accessible hosts or actor controlled infrastructure. Unlike the Drovorub-client the Drovorub-agent does not include remote shell capability and is purposed based for uploading files to and download files from Drovorub-client endpoints, and forward network traffic through port relays.
Detection Methodologies
There are several detection techniques to effectively identify Drovorub malware activity. However, due to the stealth functionality of the Drovorub-kernel module, this poses a challenge to large-scale detection on the host because it hides Drovorub artifacts from tools commonly used for live-response at scale. Below are several detection methods.
Network-Based Detection
Network Intrusion Detection Systems (NIDS) can feasibly identify command and control messages between the Drovorub-client, Drovorub-agent and Drovorub-server. Some NIDS for example “Snort” can dynamically de-obfuscate “masked” WebSocket protocol messages via scripting capabilities. The following Snort rules can be used to detect the network communications from Drovorub-server to Drovorub-client. Rule 1 can also detect unmasked Drovorub-client to Drovorub-server communications.
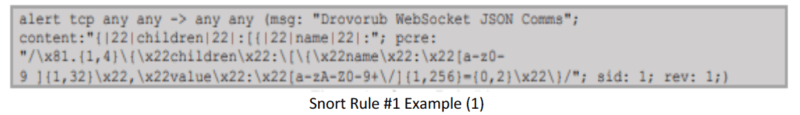
Snort Rule #1 Example (1)
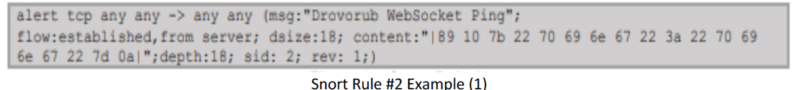
Snort Rule #2 Example (1) Advantages: High-confidence, large-scale (network-wide) detection of network command and control. Disadvantages: Subject to evasion via TLS or if the format of messages changes.
Host-Based Detection
A script to communicate with the Drovorub-kernel module using Yara rules attempts to probe whether the Drovorub-kernel module hides a specific file based on known preconfigured file prefixes. Below is an example of a Yara rule that looks for preconfigured file prefixes.
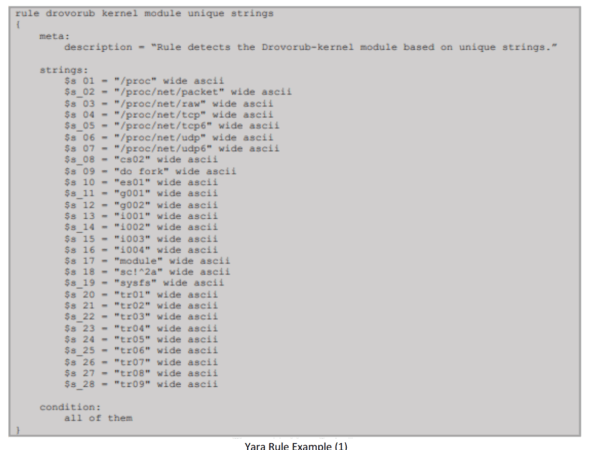
Yara Rule Example (1) Advantages: Quick, scalable deployment of detections to endpoints to detect known samples, with a relatively low risk of affecting system stability. Disadvantages: Subject to evasion if the file prefix differs from the known value.
Security Products (Antivirus, Endpoint Detection and Response, etc.)
Using different security products may provide visibility into various artifacts of Drovorub malware, including detection of the rootkit functionality. Additionally, properly configured logging by Linux Kernel Auditing System may reveal artifacts of the initial compromise and installation of Drovorub malware.
Live Response
Live response techniques include: searching for specific filenames, paths, hashes, and Yara rules on running systems using native system binaries and libraries to detect malicious activity at enterprise scale. As mentioned previously, the Drovorub-kernel module hides itself and related files, processes, and network connections by hooking certain kernel functions, significantly reducing the efficacy of this detection methodology. Therefore this detection method is subject to an increased risk of false negatives.
Memory Analysis
Analyzing the captured running memory of an endpoint is the most effective approach in detecting the Drovorub-kernel module because it offers the greatest insight into the behaviors the rootkit takes to hide itself and other artifacts on the system. There are several tools such as Linux Memory Grabber, LiME and Volatility, or Rekall that can be used to acquire and analyze memory. Below is are examples showing memory analysis with Volatility.
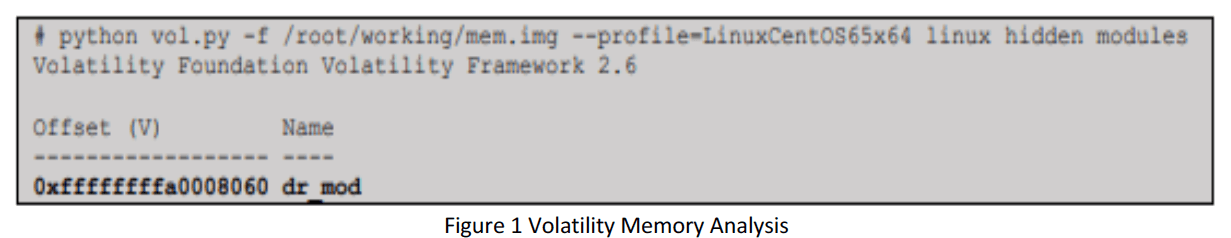
The above example shows a Volatility command run against a Linux host running CentOS memory image infected with Drovorub with a hidden kernel module.
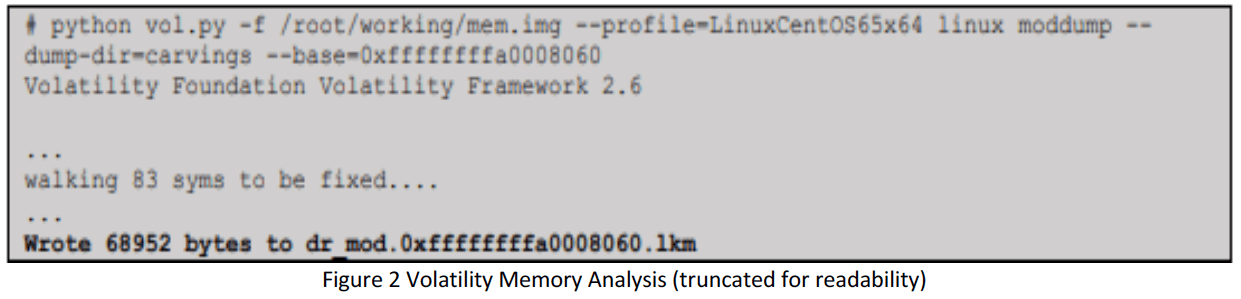
In Figure 2, Volatility is used to dump the module from the memory for further examination using the “linux_moddump” plugin.
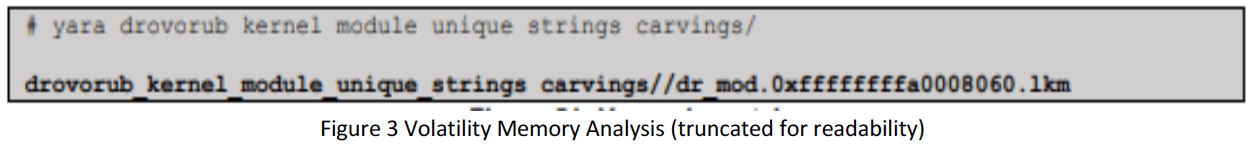
The file dr_mod.0xffffffffa008060.lkm is carved from memory to a folder “carvings”. With the Yara rule referenced in “Yara Rule Example”, you can run the rule against the file to determine if it is the Drovorub-kernel module. The above example in figure 3 shows a match for the malware. Advantages: Provides greatest level of visibility into specific rootkit behaviors and artifacts such as files, other processes, and network connections hidden by the malware. Disadvantages: Higher potential impact to system stability and not as scalable to a large number of endpoints.
Media (Disk Image) Analysis
Drovorub contains several file-based artifacts that are present and persistent on compromised endpoint disk media, though hidden from normal system binaries and system calls by the rootkit. In addition, acquiring raw media images is a viable detection method for known Drovorub samples using indicators of samples (e.g. file names and paths) or Yara rules. Advantages: Provides visibility into Drovorub files on disk, including configuration data. Disadvantages: Loss of memory-resident artifacts, higher potential impact to system stability, and not as scalable to a large number of endpoints.
Preventative Mitigations
Apply Linux Updates
It’s going to sound like a broken record, but sysadmin’s should continually check for and run the latest version of vendor-supplied software. Keeping updated software enables the user to take advantage of software advancements and the latest security detection and mitigation safeguards. Most importantly sysadmin’s should update to Linux Kernel 3.7 or later in order to take full advantage of kernel signing enforcement.
Prevent untrusted Kernel Modules
System administrators are advised to configure systems to load only modules with a valid digital signature making it more difficult for an actor to introduce a malicious kernel module into the system.
Conclusion
The GTsSS and GRU have developed a malware that acts like a swiss-army knife. The amount of tools provided by this malware has set the stage for companies and organization to step up their security detection and safeguard mitigation techniques. But what if I told you this wasn’t the first major malware these organizations have released. Not too long ago in 2018 VPNFilter which was a malware designed to infect enterprise and small office/home office routers compromising over five hundred thousand. In 2017 NotPetya (which shouldn’t be confused with Petya) was a ransomware unleashed on the world, but unlike Petya, NotPetya was a wolf taking the sheep’s clothing and turning it into a state-sponsored cyberattack. I feel that Drovorub is only the beginning of what we will see in the coming future.
Author note: All images were sourced from the NSA/FBI security alert here.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

