
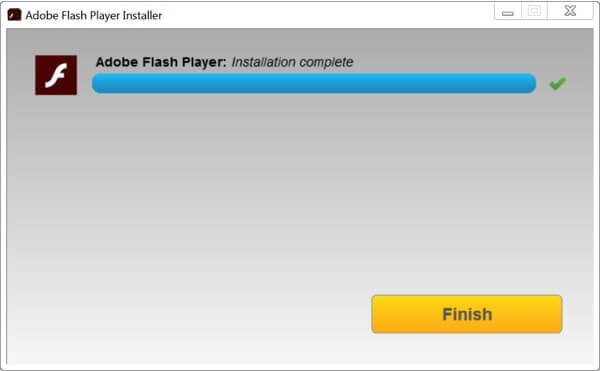
Online criminals have frequently distributed their malware attacks as fake updates for Adobe Flash. Security-savvy computer users haven't found such attacks difficult to spot and know to only get updates to Adobe Flash Player from the company's own website. A new wave of attacks, however, has added a twist to the traditional malware attack disguised as an update to Adobe Flash Player by actually updating Adobe Flash... for real! Have malicious hackers had a surprising change of heart? Have online criminals replaced avarice with altruism? Sadly not, because although a fake Adobe update is really updating Adobe Flash, it is also sneakily installing cryptomining code onto the Windows computers of its unsuspecting victims. Security researchers at Palo Alto Networks published details of how XMRig cryptomining code has been installed under the cover of fake Adobe Flash updates. Fake Flash updates that borrow genuine pop-up notifications from the official Adobe installer do indeed update their victim's Flash Player installation. Of course, a user is less likely to suspect that an Adobe Flash update was bogus if their installation of Adobe Flash really is brought up-to-date. But that's not to say there are no clues that the installer is not the one approved by Adobe. One warning sign, for instance, is that the bogus installer has not been digitally signed by Adobe, which causes Windows to pop up a warning that the user is about to run code from an unknown publisher.
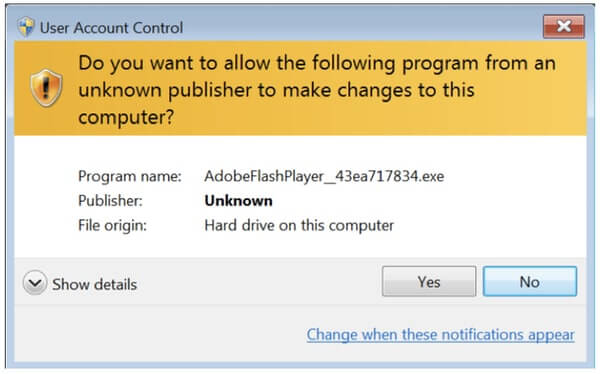
Unfortunately, many users may ignore the warning and grant permission for the program to execute regardless, causing the Adobe Flash installation to be updated and XMRig cryptomining code to be installed.
In tests conducted by Palo Alto's Brad Duncan, an infected Windows computer soon began to generate network traffic over TCP port 14444 associated with XMRig mining code in an apparent attempt to cryptomine Monero, a digital currency that has been widely adopted by cybercriminals. The observant may also notice that their computer's performance has become sluggish after the cryptomining code has been installed, although in practice, this can be difficult for many users to spot. According to the research, malicious samples that have borrowed the official Adobe installer's pop-up notifications have been seen since at least August 2018. Although the researchers have been unable to ascertain how potential victims are arriving at the URLs that serve up the bogus Adobe Flash updates, that doesn't prevent us from offering advice on how to protect against the threat:
- Use web and email filtering to protect your organisation from malicious URLs.
- Run an up-to-date anti-virus solution.
- Educate staff about the risks of running programs from unknown sources and help them understand the implications of ignoring security prompts that warn software is from an unknown publisher.
- Only trust Adobe updates that come directly from Adobe's own website, and perhaps consider uninstalling Flash altogether if you don't need it!
With an estimated $250,000 worth of Monero believed to be mined through illegitimate means every month, there is little indication that criminals will not continue to seek out inventive ways to disguise what they are doing on their victims' computers. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

