
Websites running vulnerable versions of the Drupal content management system are being targeted by the latest incarnation of the Kitty malware family. Security researchers at Incapsula report that Kitty is attempting to hijack servers using the highly critical Drupalgeddon 2.0 remote code execution exploit (CVE-2018-7600), which was made public at the end of March and exists in many versions of of Drupal 7.x and 8.x. As the researchers explain, Kitty is unusual because of how it distributes its Monero cryptocurrency-mining code. It compromises internal networks and web application servers as well as hijacks the browsers of visiting web visitors. Kitty avails itself of open-source mining code to take advantage of visiting browsers, installs a backdoor on infected systems, and contains an automatic updating routine that allows remote hackers to easily push out updates. The malware is commanded by a mining script named me0w.js. Embedded within the malware is a message that continues the feline theme:
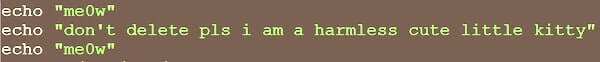
me0w, don’t delete pls i am a harmless cute little kitty, me0w
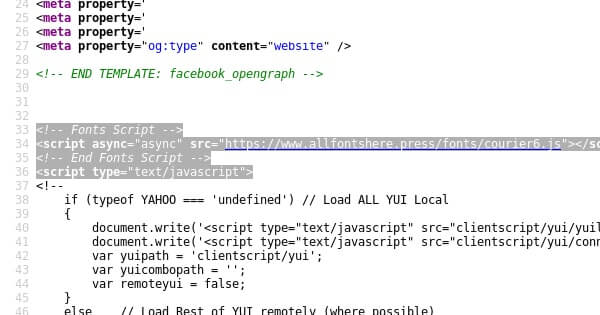
Last month, the Kitty malware was discovered targeting web servers running vulnerable versions of the vBulletin CMS. In that case, the attack exploited a vulnerability to embed malicious code posing as a script to load fonts into websites.
That attack, and this latest involving Drupal, underlines the importance of properly maintaining website content management systems with tight security and regular automated updates. Drupal has warned that it's not enough to simply update your CMS on affected web servers, as that won't remove any backdoors that may have been put in place by attackers or fix any unauthorised modifications that have been made to a site. For this reason, it's a good idea to update Drupal as soon as possible and *then* explore whether the site was compromised or not. Drupalgeddon 2.0 has also been blamed for a high profile ransomware attack that hit the Ukrainian Energy Ministry. Although not specific to Kitty malware infections, some advice has been published on the Drupal site about some of the procedures you should follow if you believe your site has been compromised. Of course, prevention rather than a cure is always best. The last few weeks have uncovered a series of highly critical vulnerabilities in Drupal's code, causing patches and advisories to be rushed out to at-risk organizations. My recommendation is that companies should adopt a layered defense to counter threats such as this rather than just relying on the traditional model of waiting for a vulnerability to be discovered and then in due course rolling out a patch. Web application firewalls, for instance, can help strip out malicious web requests before they can do any damage to a potentially vulnerable CMS. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

