
If there's one day of the year when everyone has their guard up, it's April Fool's Day. After all, who can put their hand up and say that they have never been duped by an April Fool's trick? Some of the classic April Fool's stunts have gone down in history, such as the BBC's news report from 1957 showing the annual spaghetti harvest in Switzerland. https://www.youtube.com/watch?v=tVo_wkxH9dU&rel=0 Simpler times, you say? Well, 50 years later the BBC pulled a similar stunt - getting Monty Python's Terry Jones to star in a short documentary revealing the phenomenon of flying penguins. And, like the spaghetti hanging from the branches of trees in southern Switzerland, some people believed it. They believed it because the BBC is a trusted source of information. If some nutter had sat next to you on the bus and tried to convince you that penguins could fly or that you could send a Gmail by making the motion of licking a stamp you probably wouldn't believe them. But if you're lulled into a false sense of confidence about who is sharing the information, don't verify the facts by checking with trusted and respected alternative sources, or simply forget what day it is then you might be all too easily duped. Scammers know that the weak link in any organisation is the user. Through social engineering tricks they can trick users into clicking on links, opening poisoned attachments or even handing over their passwords in the mistaken belief that they're communicating with the IT department or logging into a legitimate website. The problem is - we should treat every day like it's April 1st. Here are five types of computer scam you should look out for - regardless of the date.
That email from your friend wasn't sent by your friend
If a hacker has hijacked control of a friend or colleague's email account, they don't just have access to your friend's address book. They also have access to past messages that they have sent you, and that you may have exchanged with them. In short, if they want to, a scammer can easily replicate the style of past messages you have exchanged, refer to past conversations or simply continue an existing message thread. Being wary of messages from people you know isn't enough. Sometimes it can be an email from one of your closest contacts that is trying to trick you into making a bad decision. If in doubt, always verify that your friend or colleague really sent you the email - not by emailing them by back, but by - for instance - picking up the telephone instead.
Is that link going where you think it's going?
The invention of HTML email, with all its fancy fonts, images and colours, was great in some ways - but not necessarily a good step for security. Unlike a plaintext email, simple HTML tricks mean that you cannot always tell where that link is going to take your browser. For instance, where do you think clicking on http://www.example.com will take you? Online criminals regularly use this trick to dupe users into visiting phishing sites. Hovering your mouse over a link will often help determine where a link might really go before you click it, but there are still tricks that scammers can use in their attempt to fool you...
Is that an L or an I in that URL?
Is this the real Lloyds bank website?

Well, if you've got this far in the article you probably guessed that it's not. But how come it *looks* like the URL of the Lloyds Bank website? What you're seeing here is an IDN homograph attack. There are many different examples, but in this case an attacker could take advantage of the fact that an uppercase letter "i" looks just like a lower case "L" in this particular font.
Is that an attachment or a link?
Once again, scammers have found ways of exploiting HTML email to their own advantage. State of Security's David Bisson recently described a clever Gmail scam that would probably trick even many technical users. You receive an email with an attachment at your Gmail account, you click on the attachment, and in a new browser tab you are prompted to re-enter your Google password.
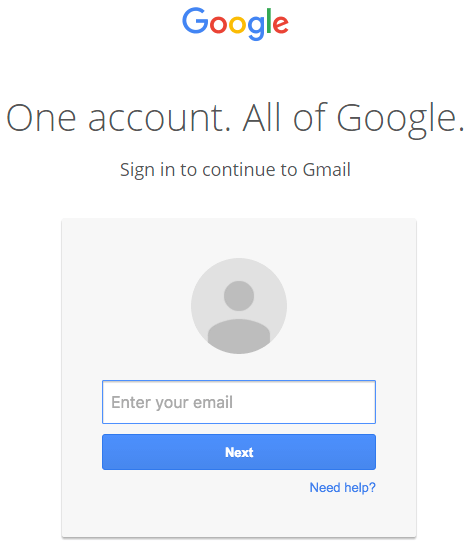
Would you dare enter your credentials? What's sneaky about this particular attack is not that the email attachment was infected by malware. No, what's crafty here is that there was no email attachment in the first place. What you clicked on, was an embedded image in the email which linked to a phishing page. Craftily the scammer has designed their image to look just like an attachment in Gmail. https://twitter.com/tomscott/status/812265182646927361
Bogus virus warnings
Hopefully we're all aware of the telephone scammers that prey on the vulnerable, pretending that they're calling from Google or Microsoft and offering to "help" remove a malware infection that they claim to have detected on a victim's PC. You may be suspicious if someone calls you at home claiming to know what's happening on your computer, but what if your computer itself tells you there's a problem? It's not uncommon today for scammers to exploit users by tricking computers into displaying bogus security warnings - designed to trick the unwary into installing risky software or calling bogus tech support numbers.
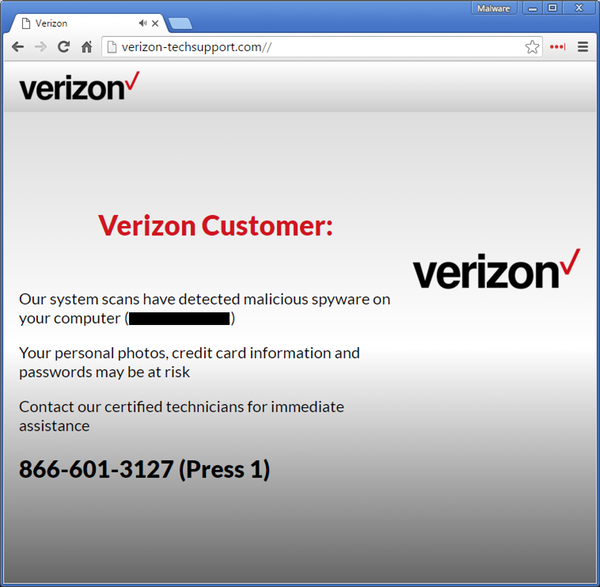
If you ever need to call a company, be wary of using the phone number offered to you in an email or in a warning message that has suddenly popped up. It could be someone trying to scam you. April Fool's day is almost upon us. Take care on the big day, but more than that - keep your guard up every day of the year. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

