
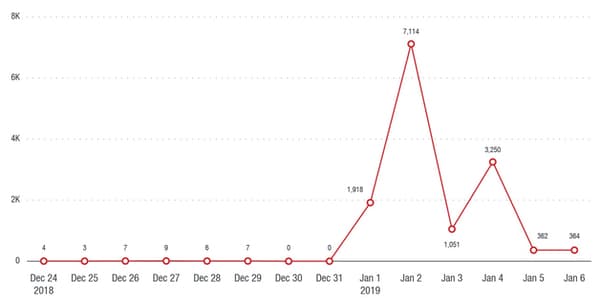
A criminal Magecart gang successfully compromised hundreds of e-commerce websites via a malicious script that silently harvested personal data and payment card information as customers bought goods and services online. Rather than specifically target individual websites, the hackers audaciously hacked a third-party Javascript library from French advertising network Adverline, allowing the malicious skimming code to run on at least 277 websites. According to researchers at Trend Micro and Risk IQ, websites affected by the breach at Adverline included ticketing, travel and flight booking services as well as online stores selling cosmetic, healthcare and apparel products. The fundamental problem is this - just about every website uses third-party Javascript used by other people. It's an easy way to add functionality to a site with no coding required. A very common example is Google Analytics, used by many millions of websites to provide webmasters with a way of collecting web traffic statistics. But Javascript is very powerful. It can do things inside your browser that may make you uncomfortable, such as modifying, reading and exfiltrating any information displayed or entered onto a webpage. Your company may have security in place to prevent hackers from successfully breaking into your systems. But with a Magecart-style attack, they haven't directly compromised your IT infrastructure. Instead, they have poisoned a third-party script used by your website. It's equivalent to poisoning a water supply upstream from where it's being drunk. Furthermore, the exploitation of the Adverline ad network underlines a tactic often seen in Magecart attacks. Criminals will take advantage of the fact that a typical website’s security team is more likely to be fully-staffed during the working week and left less well-defended at other times. Often exploitation appears to take place at weekends or -- in this case -- between January 1st and January 5th, 2019 when many IT workers would be expected to be on vacation or still nursing their New Year's hangover.
In recent months, there have been numerous companies impacted by Magecart attacks skimming their customers' payment details. Businesses hit have included British Airways, Feedify, Umbro, Vision Direct and Newegg. Hundreds of millions of customers have had their payment card details stolen through Magecart attacks. The costs are obviously significant to the companies involved and the financial institutions required to issue new payment cards to customers who have had their details stolen. And it's important to recognize that users will almost always be oblivious of the technical details of how the attack took place -- in this instance, it proceeded through malicious Javascript supplied by a third party ad company. In the eyes of the typical customer, it is the online store selling perfume or plane tickets that has been careless with their payment card details. And as a result, it is those companies whose brand is damaged. It takes years to build a brand that your customers trust. Trust takes years to build, seconds to lose and a lifetime to regain - if you’re lucky.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

