
An estimated 16,000 websites are believed to be running a vulnerable and no-longer-maintained WordPress plugin that can be exploited to display pop-up ads and redirect visitors to webpages containing porn, scams, and--worst of all--malware designed to infect users' computers. Researchers at WordFence went public about how hackers are exploiting a zero-day vulnerability in a third-party WordPress plugin called Rich Reviews to inject malvertising code into vulnerable WordPress sites. The threat is not theoretical. Website owners have posted publicly about how they have been hit by scripting malware, and they are pointing the finger of blame at the Rich Reviews plugin. Normally the advice would be for website administrators to update the plugin, thereby patching the security hole and preventing hackers from being able to compromise their websites. But in this instance, there is no update, and there may never be... because the developers of Rich Reviews stopped maintaining their software long ago. And in March 2019, after a total of 106,000 downloads, the plugin was removed from the official WordPress plugin library, reducing the chances of more websites installing it. The reason given for its removal? "Security issue."
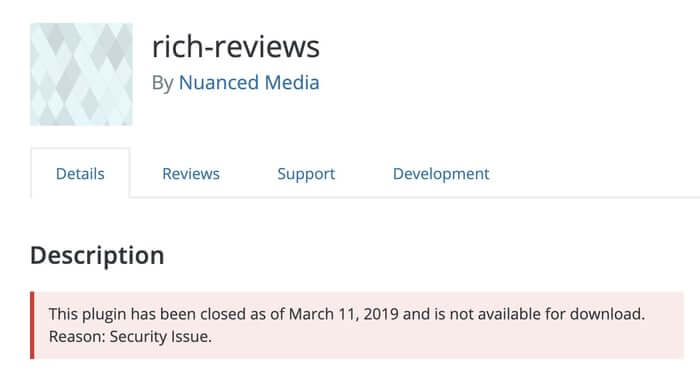
Despite the plugin being essentially defunct, thousands of businesses continue to still use it on their websites with the intention of displaying positive customer reviews.
With the plugin removed from the WordPress repository and no patch available, the most sensible step for websites is to uninstall the Rich Reviews plugin and--if they still want the functionality to display customer reviews--look for an alternative. The developers of Rich Reviews say they hope to release a patched version of the vulnerable plugin within "the next two weeks":
We’ve been working on an overall rewrite of this plugin for a while now, but someone out there apparently wanted us to work faster on it, and decided to exploit our plugin to get some malware out there. We’re now going double-quick on it, and hope to have it back up (and newly cozy and secure) within the next two weeks.
But even if Rich Reviews' developers were to create a fixed version of the previously dormant plugin, it would not be available to vulnerable websites until the software was reinstated to the WordPress plugin repository. Frankly, you're taking an enormous gamble if you continue to run a WordPress-powered website with the vulnerable Rich Reviews plugin, and you're taking a punt if you feel confident that a fix will be forthcoming in the near future. The only sensible thing to do is to take security into your own hands by removing the plugin immediately. Anything less puts visitors to your website at risk; it also risks doing serious harm to your brand. Unless you're comfortable with your website popping up porn ads and infecting visiting PCs with malware, of course?
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

