
What would you say if I told you that now a hacker doesn’t even have to trick you into installing malicious files on your computer in order to steal sensitive data? Let’s take a look at how this form of (non-) malware works and, more importantly, how to protect yourself against it.
How does this fileless malware attack occur?
The big picture involves taking control of legitimate Windows tools like PowerShell and Windows Management Instrumentation (WMI) and then undertaking nefarious activity at the command-line level. The sneaky part is that since PowerShell is such a trusted component of Windows, most security scans don’t check it. Meanwhile, once in the system by following the path of least resistance, the perpetrator can retrieve sensitive data and migrate to other machines on the network at their leisure.
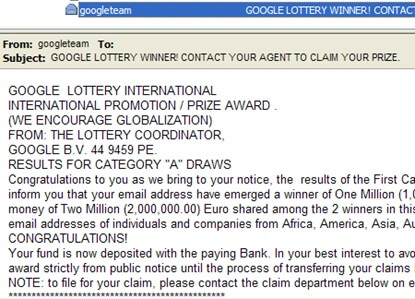
Let’s look at an example of how this might happen. Step 1: Perhaps at the behest of a clever spam message promising untold riches, a user clicks on a link and visits a website. Step 2: When Flash player loads, the fix is in. Step 3: Flash accesses PowerShell, and from here, operating only in the computer’s memory, instructions go through the command line. Those instructions tell it to download a malicious PowerShell script specializing in collecting sensitive data and sending it back to its creator. And there you go! Never once in the process did the criminal have to figure out how to sneak a malicious program past antivirus and malware defense. This is a big deal.
Why fileless malware now?
The reason sophisticated cyber criminals have shifted their focus away from popular malware strategies like brute force automated login attempts or sneaky spear phishing schemes is simple: traditional antivirus and anti-malware security aren’t even looking where these fileless malware attacks are going. They aren’t designed to stop this kind of thing. The AV suite on your computer is trained to sniff out trouble when one thing happens – a file is written. Does that mean traditional AV suites are useless in detecting this new type of computer takeover? Yep, that’s exactly what it means. There’s a good chance that once either PowerShell or the WMI is compromised, an attacker can sit there undetected for however long they like, pilfering data at their convenience.
Steps to protect yourself against fileless malware attacks
Despite the claim surrounding this brand of malware as being undetectable, let’s get it out there that it’s not literally undetectable. It just seems so when compared to previous malware iterations. The steps below aren’t foolproof but do provide a layered, systematic security approach that should minimize risk to your organization.
- Disable PowerShell and WMI if you’re not using them.
- Disable macros if you’re not using them. If you are, digitally sign and use only those vetted specifically for the company. No signature means don’t use it!
- Regularly check security logs for inordinate amounts of data LEAVING the network. Hint: it could be going to a bad guy.
- Look for changes in the system’s usual behavior patterns when compared against baselines.
- Update your software regularly.
Of course, another way to avoid these fileless malware attacks is to shut down your online business and never use a Windows system again, but that’s probably not a credible solution for the world. The five solutions presented above are meant as a starting point for a system administrator or IT staff to begin securing the network against these attacks. To learn more about how Tripwire can help detect changes on your systems, click here.

About the Author: Gary Stevens is an IT specialist who is a part-time Ethereum dev working on open source projects for both QTUM and Loopring. He's also a part time blogger at Privacy Australia, where he discusses online safety and privacy. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

