
A fully functional ransomware has been observed targeting OS X users by posing as infected BitTorrent installer files. On Saturday, users of Transmission, a free BitTorrent client, began posting on the site's forum that whenever they attempted to download Transmission 2.90 on their Macs, a message would pop up warning them that the BitTorrent installer was infected with a malware sample known as "OSX.KeRanger.A." Claud Xiao and Jin Chen, security researchers at Palo Alto Networks, examine the malicious software in a post on their company's blog.
"On March 4, we detected that the Transmission BitTorrent ailient installer for OS X was infected with ransomware, just a few hours after installers were initially posted. We have named this Ransomware 'KeRanger,'" the researchers explain. "The only previous ransomware for OS X we are aware of is FileCoder, discovered by Kaspersky Lab in 2014. As FileCoder was incomplete at the time of its discovery, we believe KeRanger is the first fully functional ransomware seen on the OS X platform."
The infected installer files, which were signed by a legitimate certificate issued by Apple, contains a malicious executable known as "kernel_service" which pretends to be a RTF file. Upon execution, KeRanger creates three files--“.kernel_pid”, “.kernel_time” and “.kernel_complete”--under ~/Library directory. It then sleeps for three days, all the while sending information about the infected Mac to a command-and-control (C&C) server. The ransomware wakes up again when it receives two lines of encoded data from the C&C server. One of these lines contains an RSA public key, which the malware uses to encrypt all files found in the /Users and /Volumes directories. After all the files have been encrypted, the ransomware displays a ransom note and asks the victims to penny up approximately US$400 in exchange for a decryption key.
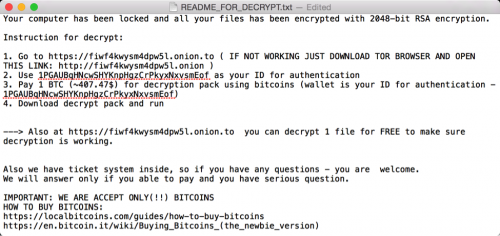
README file ask victim to pay Bitcoin Xiao and Chen reported the malware immediately to Apple and Transmission. Apple has since revoked the abused certificate, and GateKeeper will now block the malicious installers. In the meantime, Transmission is urging those running version 2.90 on OS X to immediately upgrade to 2.92. The swift response of Apple and Transmission seems to have contained this outbreak of KeRanger. However, some feel that this incident marks the start of a new era in OS X malware.
"It is a little bit surprising because ransomware has been so incredibly popular for Windows, and mobile platforms," Ryan Olson of Palo Alto Networks told Ars Technica. "It's now of the most popular criminal business models. The fact that it hasn't made it to Mac shows that it's had a great amount of success on the Windows side. But the fact that [the malware] was distributed through a legit application demonstrates that we will see this again."
To learn more about KeRanger's functionalities, read Palo Alto Networks' blog post here. For information on how you can protect yourself against ransomware on any OS, please click here.

