
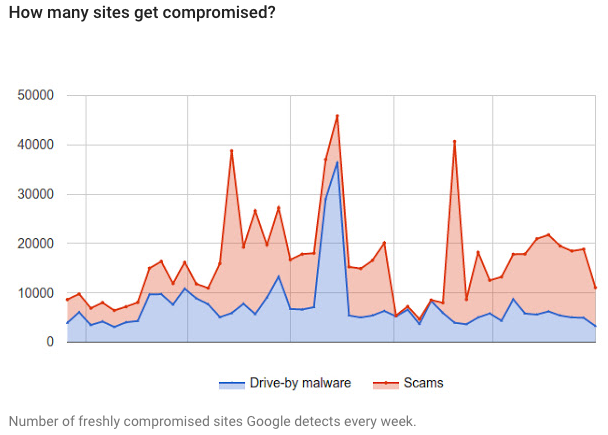
Over the last year, Google detected nearly 800,000 compromised websites – roughly 16,500 new sites every week – exposing unsuspecting visitors to malware and scams. The search engine giant detailed the findings of a study it conducted alongside the University of California, Berkley, which analyzed 760,935 hijacking incidents from July 2014 to June 2015. The sites observed were identified using the company’s Safe Browsing and Search Quality tools. The study aimed to determine the most effective ways to assist webmasters with re-securing their websites.
Source: Google Security Blog “Unfortunately, many webmasters for compromised sites are unaware anything is amiss,” explained Kurt Thomas and Yuan Kiu of Google’s Spam & Abuse Research. “Worse yet, even when they learn of an incident, they may lack the security expertise to take action and address the root cause of the compromise,” they said in a blog post. Researchers found that webmasters who proactively registered their domain with Search Console, and were notified by Google via email, had a higher success rate for recovering their compromised page, with 75 percent. Browser warnings and search warnings alone helped 54 percent and 43 percent of sites clean up respectively, noted Google. However, sites that were able to successfully recover were not always safe from falling victims to another security incident. Google and Berkley researchers monitored recently cleaned websites and found that 12 percent were compromised again within just 30 days. “This illustrates the challenge involved in identifying the root cause of a breach versus dealing with the side-effects,” said Thomas and Kiu. Google recommends webmasters register to receive security notifications through Google Analytics, as well as through Search Console. It also offers helpful tips for updating a site’s software and adding additional authentication for enhanced security.
“As we work to make the web a safer place, we think it’s critical to empower webmasters and users to make good security decisions. It’s easy for the security community to be pessimistic about incident response being ‘too complex’ for victims, but as our findings demonstrate, even just starting a dialogue can significantly expedite recovery,” Thomas and Kiu concluded.

