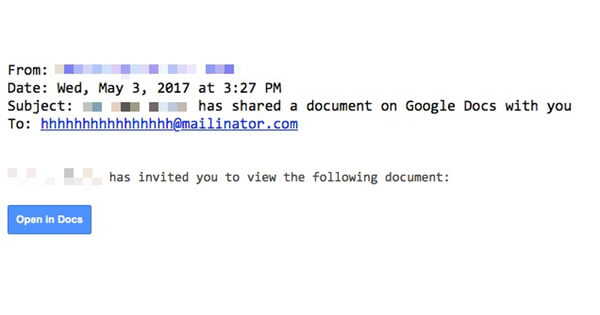
What's happened? You may well be one of the millions of internet users who received a dangerous email offering to share a Google Docs file with you. If you made the mistake of clicking on the link, you could start a process that could potentially result in your email archive and contact lists being slurped up in strangers and the same dangerous message being forwarded to everyone in your address book. What did the email look like? The malicious email looked just like a regular invitation to view a Google document. It might even appear to have been sent from one of your known friends, family members, or colleagues - lulling you into a false sense of security. What they have in common, however, is that the emails are addressed to a throwaway email address ([email protected]), with each victim BCC'd.
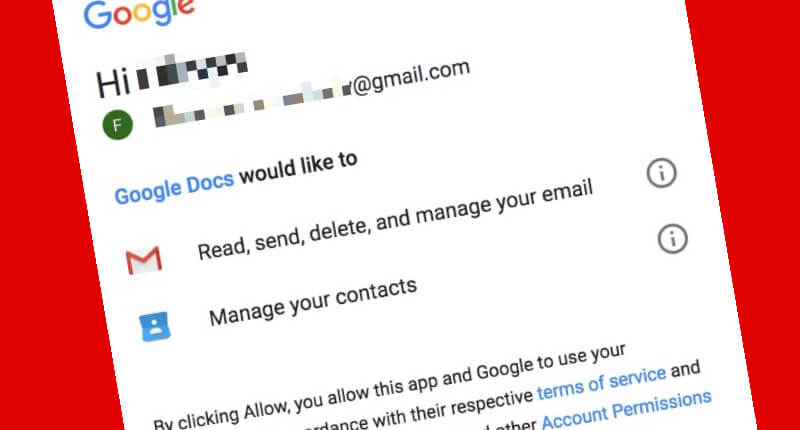
So what if I clicked? Clicking on the "Open in Docs" button *would* take you to a legitimate Google webpage, asking you to grant "Google Docs" permission to access your Gmail account.
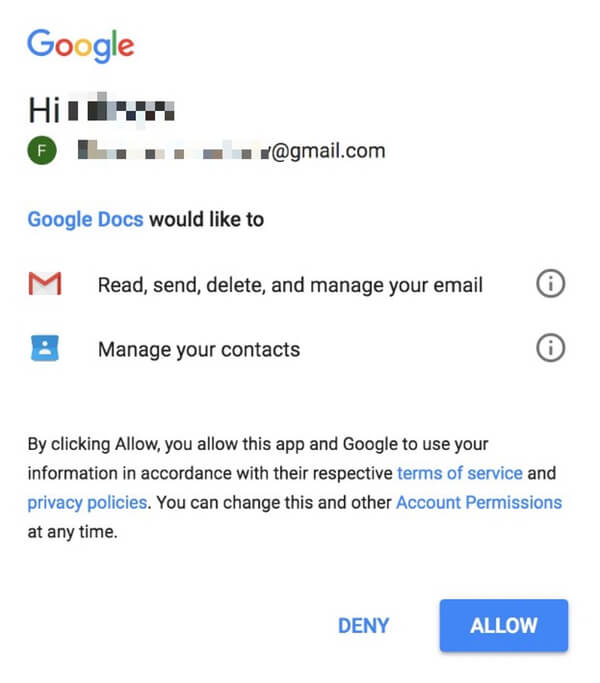
In the ultra-paranoid, that should have rung some alarm bells. After all, surely the genuine Google Docs is already connected to your Google account? And why would it need such over-arching control over your email messages? But this isn't the real Google Docs - a criminal hacker has created a bogus app called "Google Docs" and is trying to trick you into authorising it access to your account. "Since the awareness of phishing campaigns has been rising over the years, criminals have to increase their tactics to levels such as spoofing official apps such as Google Docs," explains Tripwire's Travis Smith. "Not only does this have a casual appearance of being legitimate, by being part of the official marketplace the link in the email went back directly to legitimate Google servers." In short, the weblink points a legitimate domain, owned and controlled by Google. It's understandable that you might not instantly think it's suspicious. What does the worm do? The attacker is hoping you will be tricked into creating a legitimate OAuth connection so they can ransack your account. With that connection in place, an attacker could download your email archive and contact lists and even spam out new copies of the message to people in your address book. Sure enough, the worm's code attempts to send a copy of itself to your contacts.
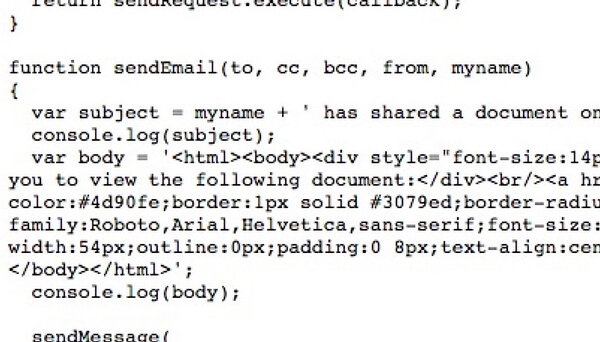
"At this time, there does not appear to be anything malicious in the sense of stealing sensitive data, however having your account compromised in this manner can still make you feel violated," Smith explains. If the worm spams out messages using my account, won't it appear as if they come from me? Yes. And that, of course, is likely to appear more convincing to the worm's next potential victim. Is there any harm don't if you don't authorise the app? No. You should be safe, as you haven't granted permission for the rogue app to have access to your account. Why would Google allow an app to call itself Google Docs? Why indeed. Clearly they didn't forsee this kind of abuse. One imagines that Google will be looking out for attacks like this in future and may block attempts by other malicious actors to create apps that pose as official Google properties. However, there may still be the potential for malicious hackers to use tricks like calling their apps "Gooogle Docs" or using homograph attacks. How can I review my app permissions to see if there are any unwanted apps that have access to my Google account? Visit myaccount.google.com/permissions and revoke permissions for any apps you don't trust. If you break a connection that it later turns out you did need, you'll receive a warning in due course. Would Google's two-step verification have helped protect my account? In this particular case, no. Nonetheless, I recommend that all Google users enable two-step verification What has Google done about this? Google responded very rapidly to early reports of the worm spreading and blocked the rogue application preventing new connections from being made. No doubt they will also be more closely policing the names of third-party apps that are allowed to connect to Google accounts in future to prevent similar attempts at abuse. Who might have been responsible for this attack, and why? The likelihood is that someone was attempting to harvest a large number of contact details, perhaps with the intention of selling them for profit to spammers and scammers. The attack appears to have been too aggressive and worm-like to have been intended as a targeted attack against a particular group, but it's interesting to note that just over a week ago researchers at Trend Micro blogged how the state-sponsored Pawn Storm hacking group was abusing OAuth in a similar fashion in an attempt to phish login credentials.
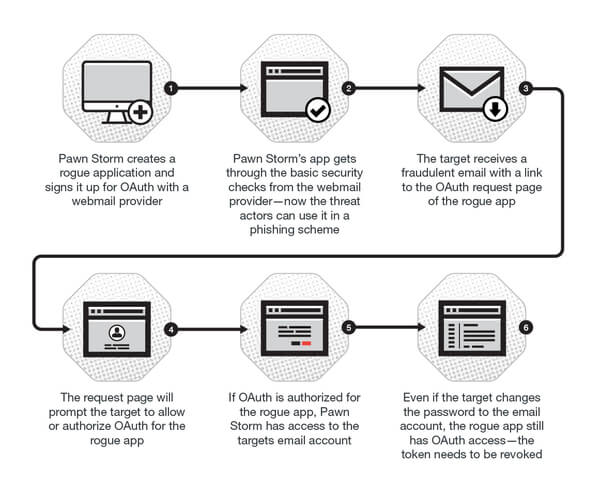
According to the researchers, the Pawn Storm group has used rogue applications with names such as Google Defender, Google Email Protection, Google Scanner, Delivery Service (Yahoo), and McAfee Email protection (Yahoo). What lessons can we learn from this? Never accept OAuth token requests from an unrequested service or person. Regularly check what applications you have granted access to your accounts. If you see a suspicious app connection, immediately revoke its access. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

