It’s the new byword in federal cyber security: “Act as though your network is already compromised.” But what does it mean? DHS’s big cybersecurity programs focus on solutions that either catch the bad guys at the perimeter (Einstein), or harden individual assets to make compromise more difficult (CDM investments in asset management, vulnerability management, configuration auditing). If we are already compromised, if the attackers are already within our gates, what do we need to be doing differently than what we are doing today? FISMA, of course, has many security controls to guide you – over 800, by my count. But one that is not that well-understood in the federal space is SI-7: SOFTWARE, FIRMWARE, AND INFORMATION INTEGRITY. While relatively new to FISMA, this control has a long history in the Payment Card Industry where it appeared as “file integrity monitoring” in the very first PCI Data Security Standard over ten years ago. The PCI DSS provides a little more context for the control than SP800-53; today it reads like this:
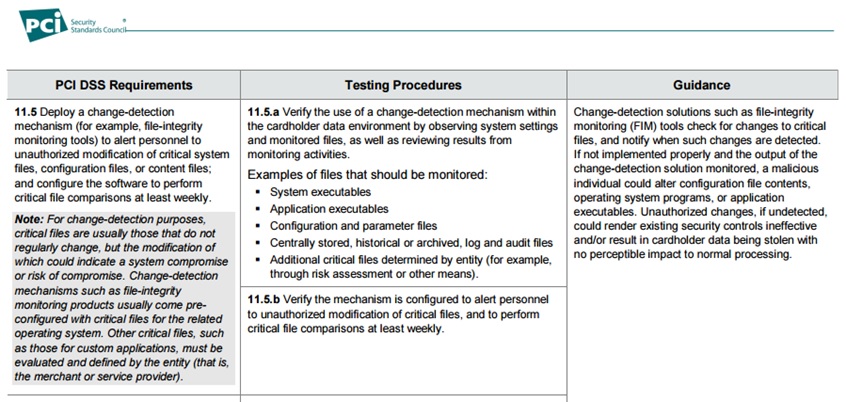
Why is change detection so important? The intruder in your network must make changes in order to move about, conduct reconnaissance, escalate his privilege and do damage. He’s got to insert executables, create accounts, change access rights, alter security configuration files, tweak something in the OS. Of course, these are the kinds of changes forensics experts use, post-breach, to try to understand what an attacker did. Helpful, but a scenario we’d prefer to prevent. The point of file integrity monitoring solutions is that they can alert you that suspicious changes are taking place, before the breach is complete. So, a critical factor to consider in addressing SI-7/DSS 11.5 or related controls, is how quickly a solution can update you on changes. The DSS standard only requires a weekly scan but solutions exist to detect change instantly and alert you (and your other security solutions) in near real-time (i.e., seconds). “But,” you say, “There must be millions of changes taking place in my network! Even if I’m seeing the intruder’s actions in real-time, how can I possibly differentiate his changes from everything else that is happening?” To address that question, I’ll have to move from talking about integrity monitoring solutions in the abstract, to talking about the one I know, Tripwire Enterprise. Lots of products can collect change data; it’s how you determine what’s important that makes change data useful. Interested in learning more? Read the follow on post titled, 5 Tips for Detecting Suspicious Changes in Your Network Title image courtesy of ShutterStock
5 Things Your FIM Solution Should Be Doing for You
Discover the pivotal role of File Integrity Monitoring in maintaining system security and compliance with major standards. Tripwire Enterprise stands out as an advanced solution, offering real-time detection and detailed context for system changes, making it a superior choice for robust cybersecurity.

