
A British man has been jailed for over six years after exploiting ad networks on pornographic websites to spread malware onto innocent users' computers. 24-year-old Zain Qaiser made massive profits from victims in over 20 countries around the world through a criminal scheme which involved malware and blackmail. According to the National Crime Agency (NCA) who investigated his activities, Qaiser's financial accounts reveal he received over £700,000 (approximately US $900,000) from his crimes, although the total is believed to be "very much higher." So high, in fact, that Qaiser was able to live a life of high-end hotels, gambling, drugs, prostitutes, and luxury purchases including a Rolex watch worth £5,000. In just one ten-month period, the NCA reported on Twitter, Qaiser spent a staggering £68,000 in a London casino. https://twitter.com/NCA_UK/status/1115638783007973381 Not bad going for a man who was registered unemployed and living with his family in Barking, Essex. So just how did Zain Qaiser manage to make so much money? The answer is somewhat elaborate. Firstly, it's worth knowing that Qaiser - who used the online handle of "K!NG" - wasn't working in complete isolation. Although he had been meddling with ransomware, and earning money from its criminal proceeds, since he was 17 years old, things ramped up a gear when he made contact with a Russian-speaking group of cybercriminals, believed to be the masterminds behind the notorious Angler Exploit Kit. With an agreement in place to split the profits with his Russian-speaking contacts, Qaiser used a variety of bogus identities and fake companies to pose as legitimate online advertising agencies, and booked ad space on some of the world's most popular legal adult websites. However, the online ads Qaiser promoted on the pornographic websites were poisoned with the Angler Exploit Kit, meaning that unpatched, unprotected computers visiting the webpages could be compromised and infected with malware. The result would be that large numbers of insufficiently defended computers would be infected by different types of malware including Reveton, a family of ransomware with a long history of being successfully distributed on a significant scale. Reveton would lock users' computers, claiming to be a warning from law enforcement or government agency that an online offence had been committed (such as viewing child abuse material) and that a find would need to be paid before normal operation of the PC would be returned.

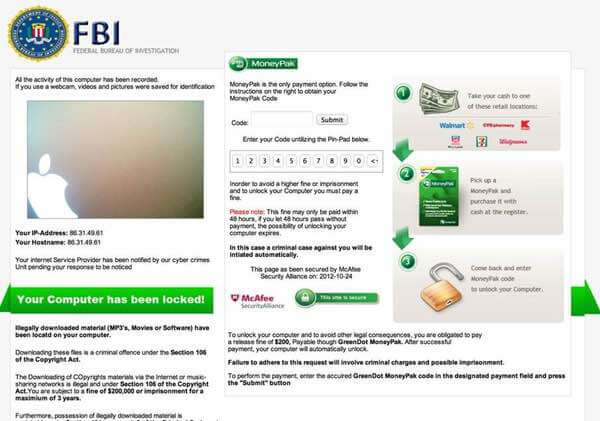
Typically a "fine" of between $300-$1,000 worth of cryptocurrency would be requested in order to unlock infected computers. Victims were told that if they didn't pay the fine immediately, they could face up to three years in prison. Many victims - no doubt fearful of the embarrassment if their friends, family members, or police discovered what had happened after they visited a porn website - simply paid the fine. Any virtual money sent by the extortion victims would be split between Qaiser, his Russian-speaking cohorts, and a network of online criminals from China and the United States who helped him launder the cash. Millions of computers around the world are said to have been infected through the campaign. The NCA calculated that every month just one of the poisoned ads appeared on 21 million web browsers. Of course, the fact that ads were spreading malware didn't go unnoticed. Indeed, some of the online ad networks that sold ad space to Qaiser tried to stop him. A Canadian ad broking firm asked Qaiser to stop, but received a response telling them it would be better if they co-operated:
"Really, it's just better if we work together. We can make some serious money together. It's my way or no way. The K!NG is back."
With his partnership offer rejected, Qaiser launched distributed denial-of-service (DDoS) attacks against agencies who complained about his activities, telling a director at one of the firms:
"I’ll first kill your server, then send child porn spam abuses."
These attacks are said to have cost the advertising networks, through lost revenue and mitigation costs, at least half a million pounds. After a long-running and complex investigation, involving law enforcement agencies in the UK, United States, Canada, and Europe, Qaiser has now been brought to justice, and sentenced to six years and five months in jail In addition, the FBI and US Secret Service have arrested people in relation to the malware campaign. NCA senior investigating officer Nigel Leary described the case as "one of the most sophisticated, serious and organised cyber crime groups the National Crime Agency has ever investigated." It certainly was an organised and successful (until Qaiser's apprehension) malware campaign that managed to fleece millions out of unsuspecting internet users. There's a certain irony that none of them would have fallen foul of the attack if they had taken the simple precaution of enabling an ad blocker before visiting the porn websites.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

