A ransomware outfit is advising its victims to secretly tell them how much insurance they have, so their extortion demands will be met.
As security researchers at Varonis describe, a new strain of the HardBit ransomware has taken the unusual step of asking targeted companies to spill the beans of whether they have cyber insurance (and the terms of that insurance) anonymously.
According to a part of a message in the ransomware note dropped on computers after an attack, sharing insurance details benefits both the victim and the attackers.
...since the sneaky insurance agent purposely negotiates so as not to pay for the insurance claim, only the insurance company wins in this situation. To avoid all this and get the money on the insurance, be sure to inform us anonymously about the availability and terms of insurance coverage, it benefits both you and us, but it does not benefit the insurance company.
HardBit 2.0 claims to steal files from compromised networks, encrypts the data it leaves behind, and demands a cryptocurrency ransom be paid - dangling the threat that company secrets will be released online.
Whether this threat is genuine or not is up for question, as to date no one seems to have discovered a data leak site operated by the HardBit gang.
However, the cybercriminals behind HardBit 2.0 do also warn that if payment is not made victims will not only never have access to their files again, but are warned that their company will be attacked again in the future.
Furthermore, if payment is not received or negotiations have not begun within 48 hours, HardBit 2.0 warns that the ransom will be doubled.
So, what's a company to do if it gets hit by HardBit 2.0?
It can restore from a (hopefully) working, uncompromised backup and replace its encrypted data and replace with uncorrupted versions. The business may cross its fingers that the HardBit attackers won't release any stolen data in future, and won't attempt another attack.
Or the corporate victim can make the difficult decision to negotiate with its attackers, in the hope that an agreement can be made.
That is clearly the cybercriminals' ideal scenario. After all, they don't win anything by releasing data (other than stoke their image of a ransomware gang that's not to be trifled with). They probably don't even want to hack the company again, if they don't think there is any prospect of extracting a ransom payment in future.
No, the attackers would rather that a simple financial transaction be made, and they can then go on to find their next victim. What they don't want is a third-party negotiator or insurer lowballing them.
And that's why part of their ransom note sets out that companies hit by HardBit 2.0 should be prepared to share the details of their cyber insurance:
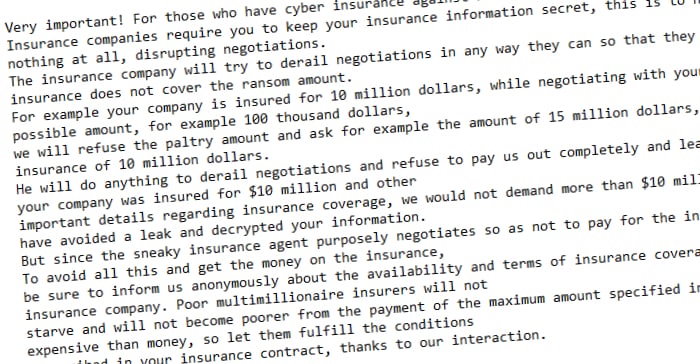
Very important! For those who have cyber insurance against ransomware attacks. Insurance companies require you to keep your insurance information secret, this is to never pay the maximum amount specified in the contract or to pay nothing at all, disrupting negotiations. The insurance company will try to derail negotiations in any way they can so that they can later argue that you will be denied coverage because your insurance does not cover the ransom amount. For example your company is insured for 10 million dollars, while negotiating with your insurance agent about the ransom he will offer us the lowest possible amount, for example 100 thousand dollars, we will refuse the paltry amount and ask for example the amount of 15 million dollars, the insurance agent will never offer us the top threshold of your insurance of 10 million dollars. He will do anything to derail negotiations and refuse to pay us out completely and leave you alone with your problem. If you told us anonymously that your company was insured for $10 million and other important details regarding insurance coverage, we would not demand more than $10 million in correspondence with the insurance agent. That way you would have avoided a leak and decrypted your information.
The cybercriminals behind HardBit even attempt to quash any pangs of guilt an IT administrator or CISO might be having about sharing details of their insurance:
"Poor multimillionaire insurers will not starve and will not become poorer from the payment of the maximum amount specified in the contract, because everyone knows that the contract is more expensive than money, so let them fulfill the conditions prescribed in your insurance contract, thanks to our interaction," the ransom note concludes.
Should you pay a ransom if cybercriminals have hit your company? Should you help them extract the maximum amount possible from your insurers?
That's a question ultimately only you can decide. Better, clearly, to have successfully managed to fend off an attack in the first place so your business is never placed in such a dilemma.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

