
BSides is known for its collaborative and welcoming environment – something that truly sets it apart from the many other security conferences that are held these days. Today, the conference series has spread all across the world, yet its mission remains the same: to provide an open forum for infosec discussion and debate. Tony Martin-Vegue, a speaker at this year’s BSides San Francisco conference, said it best:
“It’s a natural evolution of hacker groups from the ‘70s and ‘80s where a group of like-minded individuals meet up and share knowledge, without vendor pitches, egos, or strict rules,” he said.
I was fortunate to attend the 2017 BSidesSF event earlier this month and had the opportunity to hear from many bright minds excited to share their ideas. Below is a brief summary of just a few talks that I enjoyed, along with the awesome visual notes that the talented Kelly Kingman drew in real-time. http://www.slideshare.net/Tripwire/top-talks-from-bsides-san-francisco-2017
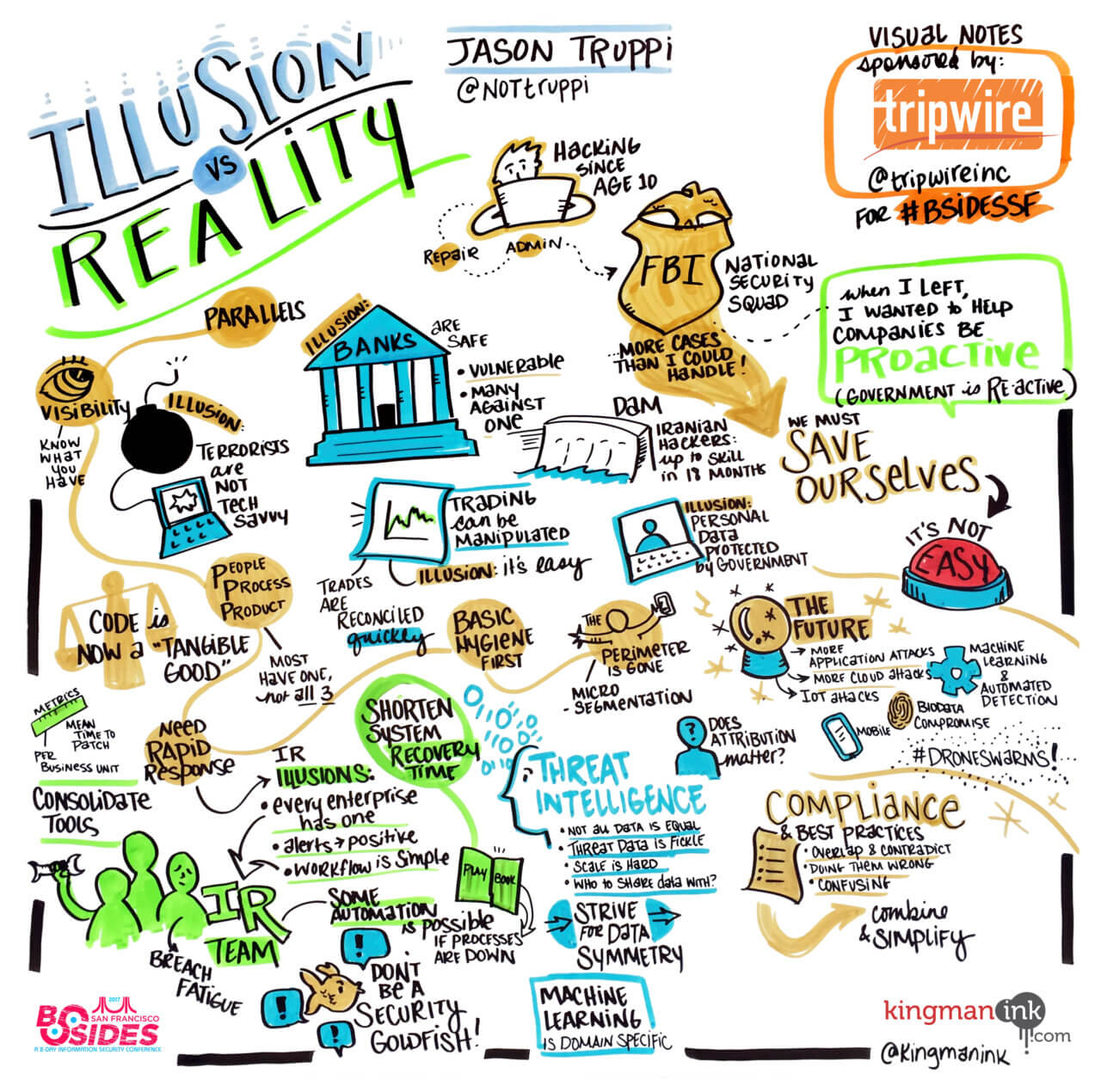
Illusion Vs. Reality: An FBI Agent’s Take on How Private Sector Realities Are Masked by Government Sector Illusions of Intelligence Sharing, Public-Private Partnerships and Best Practices
By Jason Truppi, Director of EDR at Tanium (@NotTruppi) Former FBI agent Jason Truppi kicked off the event with an intriguing presentation discussing his “illusions and realities” while working on some of the nation’s most notorious cyber intrusions. Now in the commercial sector, Truppi explained that there are many parallels between the government side and the private industry – from the extreme lack of visibility into the number of assets they own to the disconnect between people, process and product. Truppi added that most organizations “investing” in the most advanced tools don’t even have the most basic principles in place. Meanwhile, incident response teams are feeling overwhelmed with alerts when they’re using 10-15 different tools, meaning there’s a huge need for tool consolidation. Ultimately, Truppi urged the government and tech companies to work better together in order to solve the breach pandemic we have today.
“The Government needs help… but it can’t be our only savior. We need to help ourselves,” said Truppi.
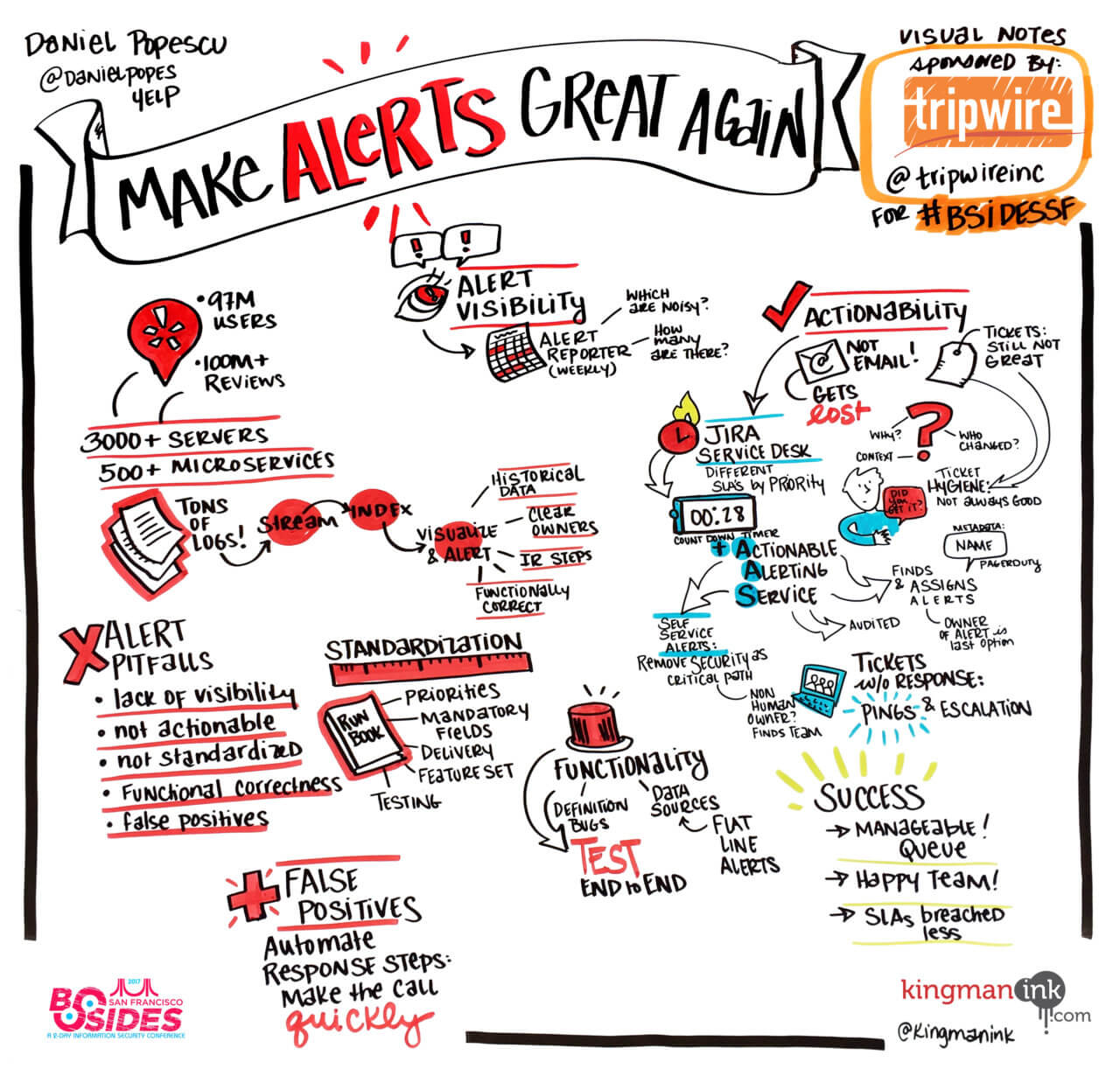
Make Alerts Great Again
By Daniel Popescu, Security Engineer at Yelp (@danielpopes) To gain visibility into the frequency of their alerts, ensure they were actionable and reduce false positives, Yelp’s security engineer Daniel Popescu explained how his team implemented certain tools and processes to help them address common alerting pitfalls. Yelp suffered from a lack of visibility into the frequency of their alerts; they spanned across multiple systems and had no comprehensive dashboard telling them how many alerts they had. Their solution was to create a service that built weekly reports in spreadsheet form from the various alert sources, allowing them to gain insight into which ones were firing too often, which produced too many false positives and focus their attention on the most important alerts. Another issue they addressed was the fact that their alerts were not actionable. When using emails to send these notifications, Popescu noticed they were easily ignored and it was difficult to assign ownership. Although ticketing systems are better, they also lack enforcement that the alerts are going to be dealt with, said Popescu. So, their solution was to enable JIRA service desk, which allowed them to set SLAs and queues. Popescu’s team also created a run-book for setting up new alerts, which identifies alerting priorities, mandatory fields and delivery mechanisms. His team performs end-to-end testing for 100% of new alerts to ensure they are firing off when they should. Through these implementations, Popescu said Yelp’s active ticket queue is now much more manageable, and SLAs are now met over 50% of the time.
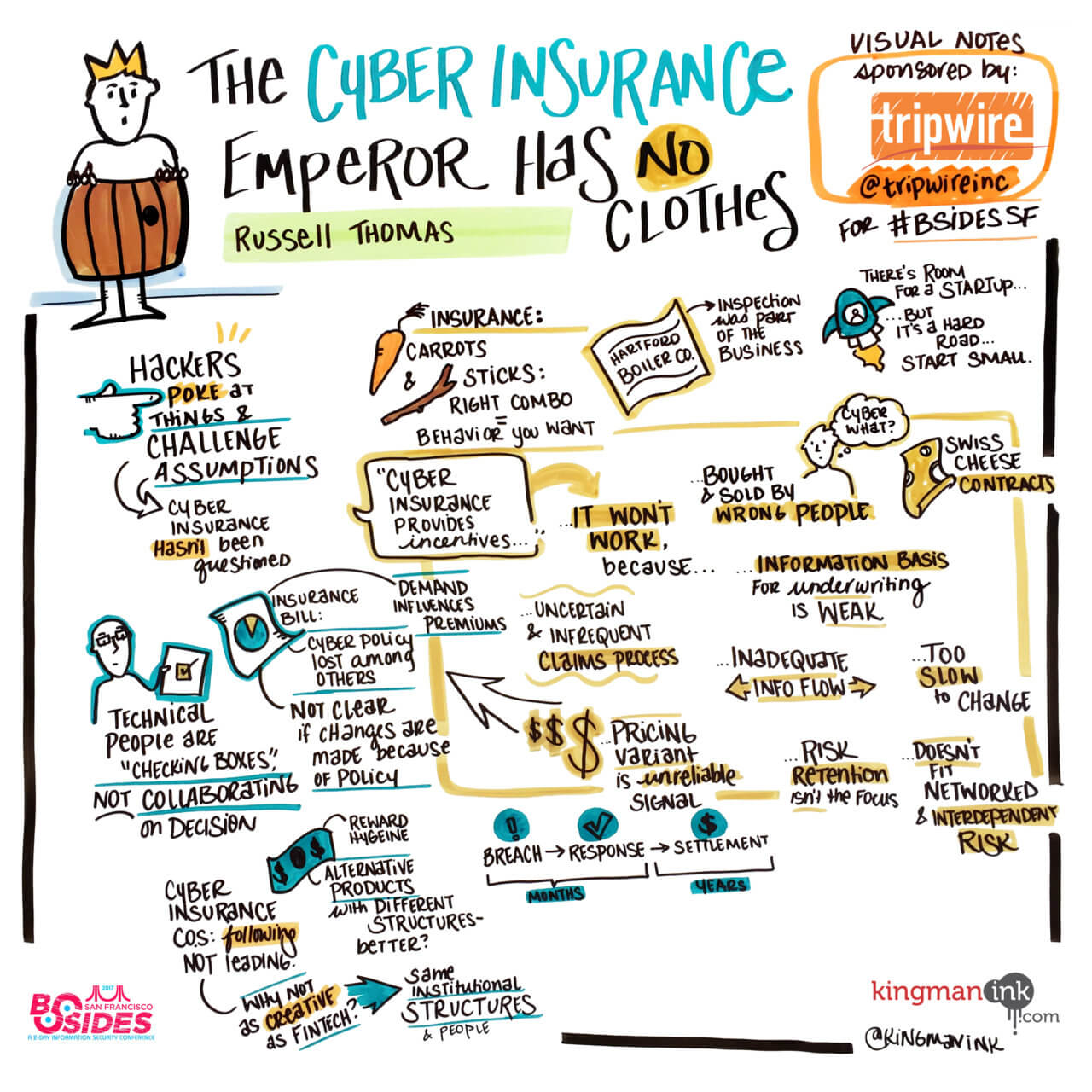
The Cyber Insurance Emperor Has No Clothes
By Russel C. Thomas, Data Scientist In this presentation, Thomas offered an alternative point of view on cyber insurance and argued whether it truly improves organizations' incentives. Thomas gave many reasons why cyber insurance is a misfit for the "job to be done," such as: 1. Cyber insurance is bought by, and sold to, the wrong people. Thomas argues that buyers are often in Finance or Legal, while some organizations even outsource the buying process. Furthermore, corporate insurance is commonly sold by brokers, who try to serve the needs of insurance providers and consumers, but in reality their interests are closely tied to providers. 2. The information basis for underwriting decisions is weak. According to Thomas, none of the information gathered by insurance companies about a firm is contextualized. Meanwhile, insurance underwriters are making "course grained decisions" based on a random collection of qualitative information that may or may not have anything to do with risk posture. 3. The structure of cyber insurance contracts is a poor fit. Contracts are long and complex, with limits, deductibles, co-pays, etc; this makes it more difficult, not easier, for companies to do risk pricing, so it can be factored into their current investments and decisions. 4. The claims process is too expensive, too uncertain, and not frequent enough. Rather than infrequent claims – which are expensive for insurance companies to process and for insured parties to file – Thomas argues that what society needs is frequent reporting of breaches and incidents. This will help us gather data that is rich enough to model risk at all scales. 5. The information flow between insured and insurance firms is woefully inadequate. Thomas believes the capability of insurance firms to take in and process information from all of their customers is close to zero. "Insurance firms don't learn about near misses, early warning signs, or even evidence that the information they may have received is incomplete, ambiguous, or erroneous," he said. Thomas went on to explain other reasons why there should be better incentive instruments. He concluded stating that cyber insurance is still in its infancy and that it needs more time to grow – check out his very detailed blog post for more of his thoughts.
"Cyber insurance has the wrong clothes for the purposes and social value to which it aspires."
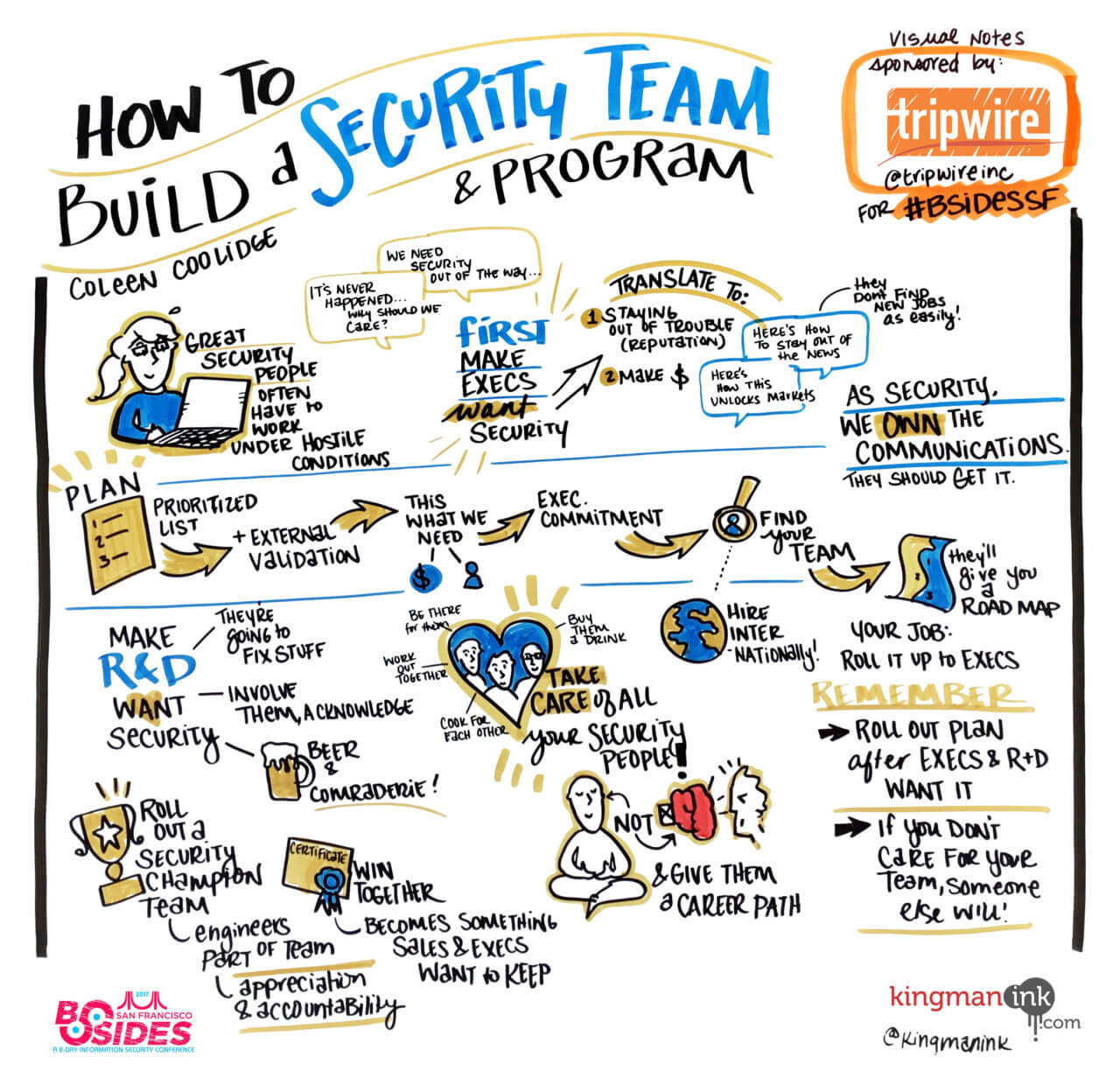
How to Build a Security Team and Program
By E. Coleen Coolidge, Director of Information Security at Twilio (@coleencoolidge) As the director of information security for a local startup, Coolidge shared with us her "war stories" and lessons learned from building a security team and program from scratch. Coolidge broke this down into practical steps – the first being to develop a plan. It's important to make executives want security first, she said. When Coolidge attempted this in her position, she realized she wasn't getting the response she wanted because she wasn't talking to executives in a way that would appeal to them. Executives care about 1) staying out of trouble and 2) making more money – she tied these factors back to security in order to make them care. She also recommended bringing in external validation, such as firms like PwC, Deloitte, or KPMG.
"When you have external validation, it means they can't ignore the problem," she said.
Then, as soon as you get your executives on board, move immediately to hiring your people, urged Coolidge. Another important step is to involve R&D heavily, make friends with them, and treat them as an extension of your security team. Lastly, Coolidge emphasized its just as important to take care of your team members – if not, someone else will.
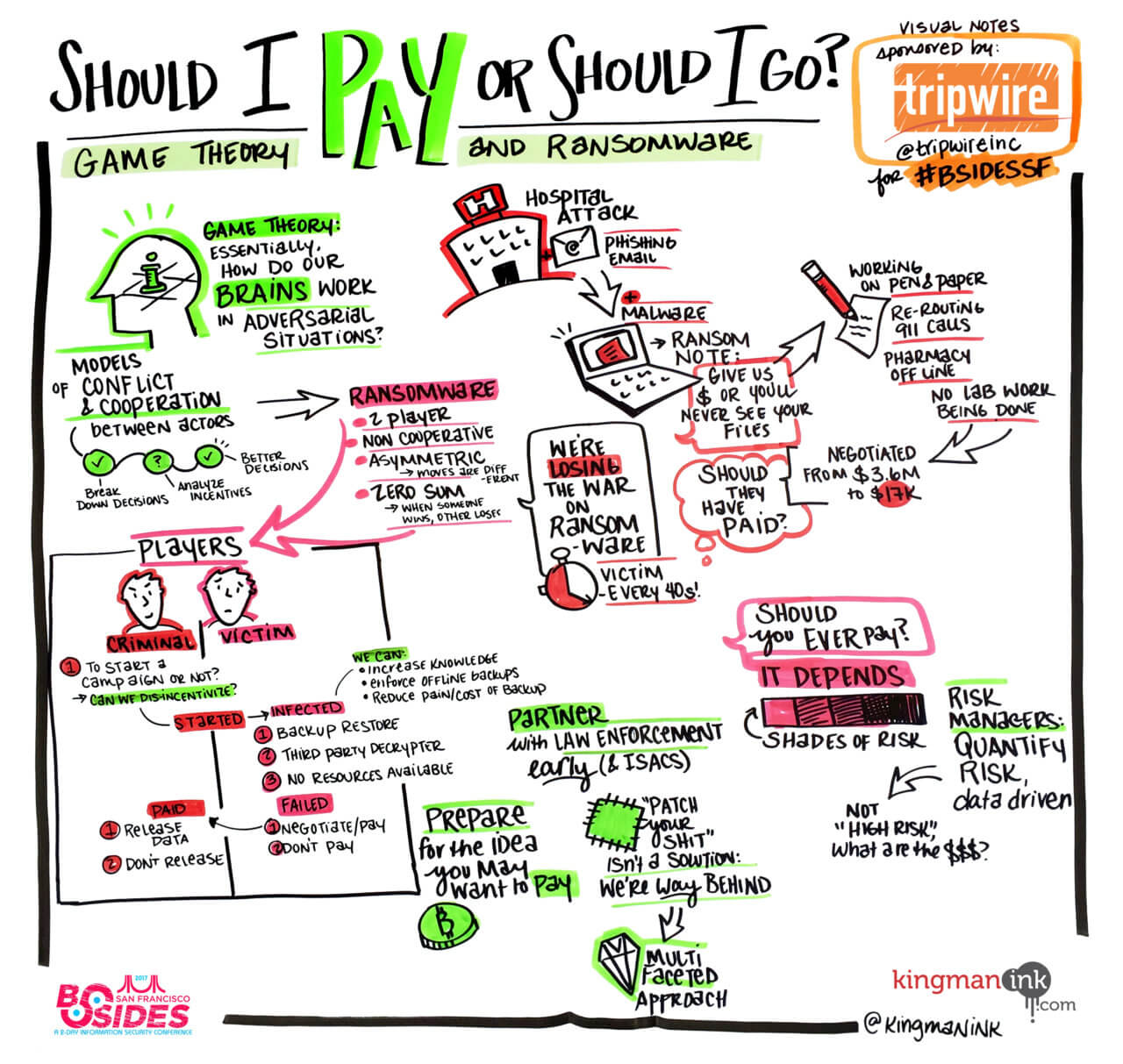
Should I Pay Or Should I Go? Game Theory and Ransomware
By Tony Martin-Vegue, Manager of Information Security Risk (@tdmv) Martin-Vegue began his presentation by explaining a recent ransomware attack that hit a Hollywood hospital. Cybercriminals demanded $3.6 million after the infection rendered the hospital's system completely unaccessible for nearly a week. Ultimately, the hospital negotiated the ransom payment down to $17,000 – but did they make the right decision? Ransomware response isn't black or white, and although we hate to hear it sometimes, the answer is "it depends." To help solve this dilemma, Martin-Vegue introduced the concept of game theory: "the study of mathematical models of conflict and cooperation between intelligent rational decision-makers," or essentially, how our brains work in adversarial situations. We first analyzed the "decision tree" or choices that both players have. For cybercriminals, their first decision is to start a ransomware campaign or not. Here, we should think of what their motives are and how we can disincentivize them (e.g. harsh penalties, jail time). After an infection, the victim has the option to restore a back-up (if available) or use a third-party decrypter (if there is one). Martin-Vegue pointed to the "No More Ransom Project," which is a non-profit initiative aimed at helping victims of ransomware retrieve their encrypted data without having to pay the criminals. To interrupt this, however, we should aim to increase knowledge of ransomware, enforce offline back-ups, and reduce the pain of restoring them. Lastly, victims have the decision to pay or negotiate – or not. And even after paying, victims face the chance that they won't receive a working decrypt key. Martin-Vegue stressed that thought leaders need to recognize this is an open problem without a solution (and that patching is not a solution). Some organizations are months to a full year behind on critical patches. So, what do we need? Martin-Vegue concluded by proposing the need for multi-faceted solutions, next-generation infosec and risk managers to be able to quantify this risk.
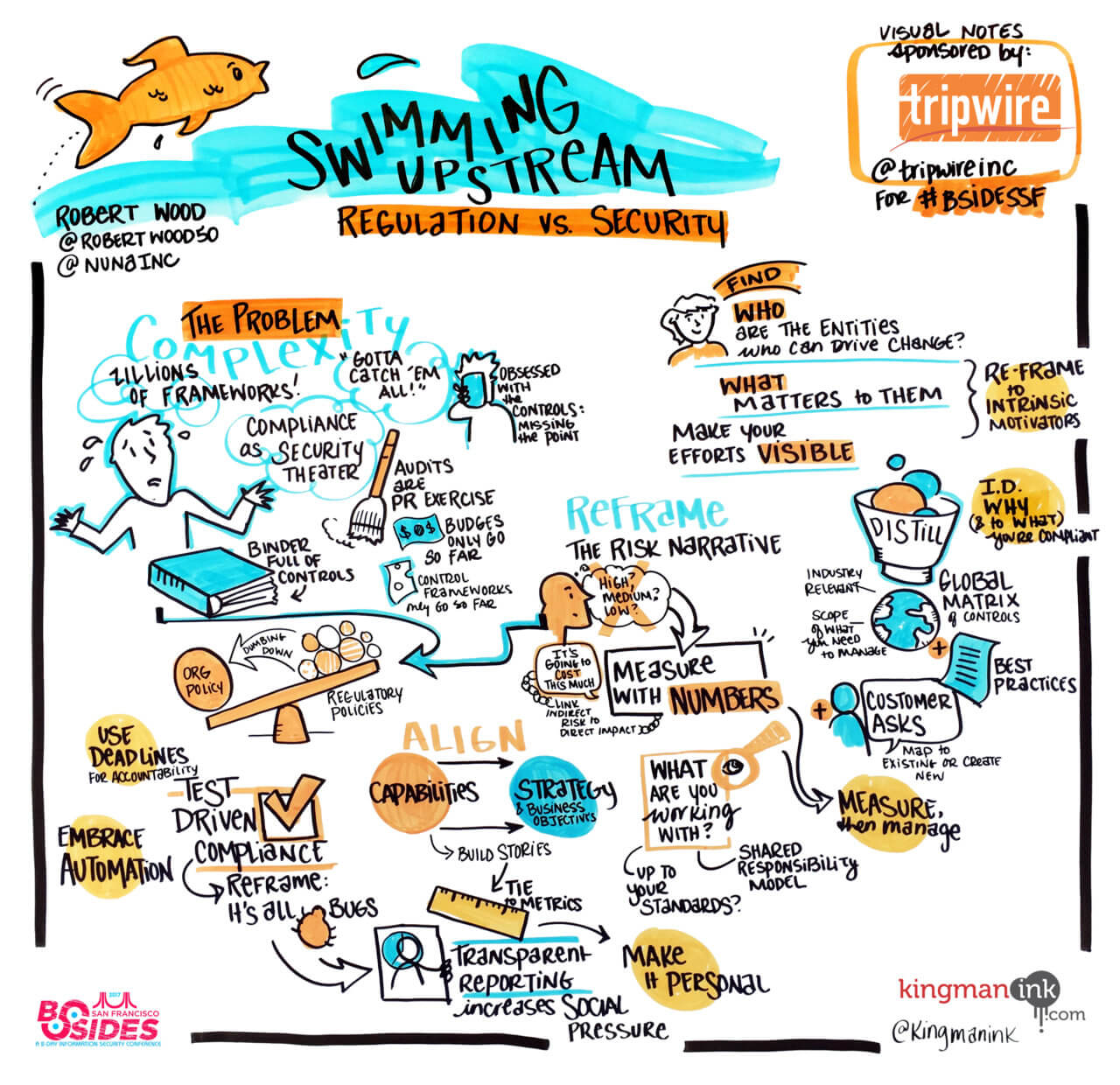
Swimming Upstream: Regulation vs. Security
By Robert Wood, Head of Security at Nuna (@RobertWood50) Wood walked us through several strategies that security teams and leaders can use to achieve their security goals while "navigating the murky waters of bureaucracy, compliance and politics." First, Wood addressed some of the problems with regulation, the first being that there are zillions of frameworks out there. We're drowning in regulations, and there's a notion that we "gotta catch 'em all," he said. Next, compliance is like security theater – much like when tidying up our house before guests make a visit, companies are also putting their best foot forward any time there's an assessment. Furthermore, in many cases, Wood notes budgets only go so far to cover compliance, and control frameworks don't cover it all. Lastly, Wood says people get so "enamored" tracking controls that they forget to see if they're really effective. Using examples from his own career, Wood suggested organizations focus on industry-specific regulations first. Then, security best practices (such as threat modeling) and customer requirements. Wood's key takeaways for "fighting upstream" included:
- Reframe the narrative around risk – learn how to report to people's motivation
- Identify why you need to be compliant and who you need to be compliant to
- Communicate effectively to who it matters
- Have an element of accountability and deadlines when it comes to remediation from audits or assessments
- Use numbers to drive how you talk about risk
- Embrace automation to implement/maintain/correct controls
Did you get a chance to attend #BSidesSF? What was your favorite talk? Let us know in the comments below.

