
Fancy a career as a blackmailing cybercriminal but don't have the technical nous? Don't worry, you can easily find people all too willing to help you embark on your life in cybercrime via popular freelance-hiring websites. And, it seems, you may only need to pay five dollars to get a hacker to launch a debilitating denial-of-service attack against the website of your choice. That's the finding of Incapsula security researchers Igal Zeifman and Dan Breslaw who discovered that "DDoS testing services" were being openly offered for hire on Fiverr for as little as $5.
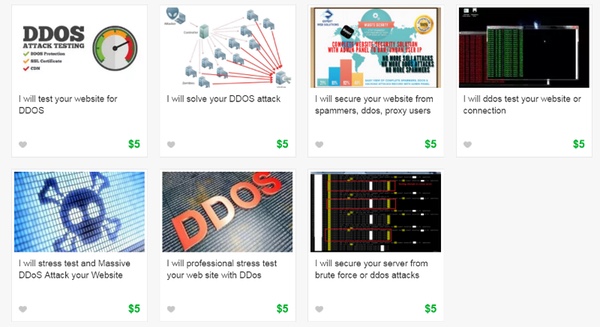
A mere five dollars is an extraordinarily low figure for a DDoS attack, and suggests that the large number of people able to offer similar "services" has pushed the price down. Last year, for instance, a study by Incapsula found the average cost of an hour-long DDoS attack was considerably higher (although though still absurdly affordable) at $38. Typically those advertising DDoS-for-hire services are promoting them as "website stress tests" rather than all-out criminal attacks, but Zeifman and Breslaw managed to get at least some of those advertising on Fiverr to admit that they would be prepared to "test" sites not owned their prospective client:
Not wanting to rush to judgment, we decided to investigate and see if the users were the innocent stress testers they claimed to be. To do so, we created an account on Fiverr and asked each of the stresser providers the following question: “Regarding the stress test, does the site have to be my own?” Most had the good sense to ignore our message. One suggested that we talk on Skype. In the end, it was skull-and-bones guy who spilled the beans, saying: "Honestly, you [can] test any site. Except government state websites, hospitals."
As more and more organisations become reliant on their internet presence to do business and stay in touch with their customers, so the potential increases for distributed denial-of-service (DDoS) attacks to strike a painful blow. Whether the motivation be political or financial, And it's not just conventional computers which run the risk of being commandeered into botnets launching DDoS attacks. As we previously reported, even compromised CCTV surveillance cameras located in shopping malls have been hijacked to launch attacks against websites, and there is plenty of potential for other poorly-secured Internet of Things devices to be exploited for similar purposes in the future. A $5 DDoS attack is unlikely to be the hardest type of attack for well-prepared websites and DDoS-mitigation services to deflect, but at the other end of the spectrum there are very hard-hitting DDoS attacks of immense magnitude. Kris Beevers, the CEO of DNS and traffic management provider NS1, has gone on the record this week describing how his company has been fighting "a series of concerted assaults from a determined attacker" this month, using different strategies and a "rare degree of sophistication and scale":
Over the course of last week, we sustained dozens of large DDoS attacks, ranging in strategy from simple volumetric attacks, to complex direct DNS lookup attacks, to concentrated attacks against our upstream network providers and other vendors. These attacks are an escalation above and beyond a recently observed increase in malicious activity broadly targeting the DNS, CDN, and internet infrastructure industries. Unfortunately, our customers were impacted early in the attacks by partial loss of service for brief periods on Monday and Tuesday, primarily in Europe. As we analyzed and adjusted our response to the shifting attacks, we prevented further impact, despite continuing attacks through the remainder of the week and into this week.
The DDoS attacks weathered by NS1 are thought to have increased in volume to 30-50Gbps range. Beevers goes on to say that he believes NS1 is the target of the attack, rather than one of its customers. If an internet infrastructure company like NS1 is challenged by DDoS attacks you have to wonder how regular online firms are supposed to cope if they become the targets of DDoS attackers. In Beevers' opinion, what's needed is greater co-operation in the industry between companies, sharing information on attacks and developing greater resilience:
"As an industry, DNS service providers can do better to limit the impact of malicious attacks on our customers and the internet at large. Over the last decade, as the threat of attacks has escalated, we have entered an arms race, with DNS providers continually evolving the scale and sophistication of our networks to match those of the attacks themselves. We have treated the issue as one for individual providers to solve independently, and even as a commercial opportunity. This approach has exacerbated the impact of DDoS attacks because of the lack of a cohesive, industry-wide approach to solving such attacks and limiting the impact on customers."
Ultimately, it's probably not the $5 DDoS attacks that we should be worrying too much about. It's the larger scale attacks that have the most potential to disrupt legitimate uses of the internet, inconvenience innocent users and cost companies money. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

